Weaponized Performance Reports Deploy Guloader Malware
As cybersecurity threats evolve, attackers increasingly deploy creative social engineering techniques to compromise organizations. A recent threat has emerged involving the Guloader malware, which is...
As cybersecurity threats evolve, attackers increasingly deploy creative social engineering techniques to compromise organizations.
A recent threat has emerged involving the Guloader malware, which is being disguised as employee performance reports to trick users into downloading and executing malicious files.
This sophisticated attack vector exploits human trust and workplace familiarity to distribute dangerous malware that can compromise sensitive company data and personal information.
The attack begins with a phishing email claiming to contain an October 2025 employee performance report.
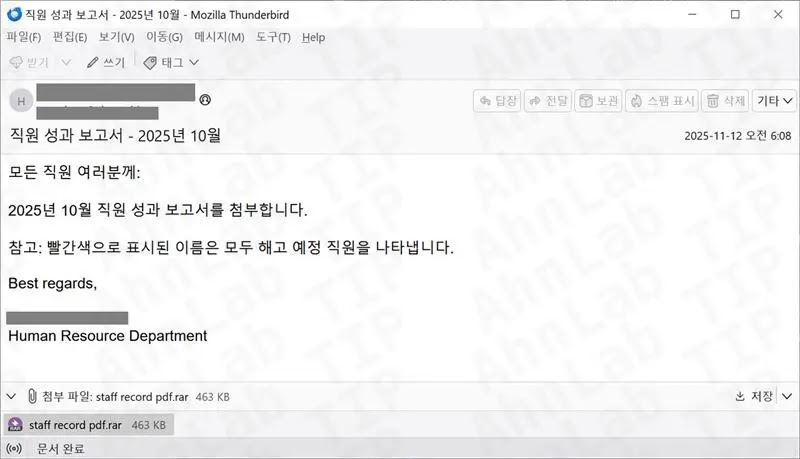
The email uses urgency tactics by mentioning potential employee dismissals, prompting recipients to open the attachment.
This psychological manipulation increases the likelihood of users bypassing security awareness and opening what appears to be a legitimate business document.
The deceptive nature of this campaign makes it particularly dangerous, as it targets the intersection of workplace communication and security vulnerability.
ASEC analysts and researchers noted that the attached file is a RAR compressed archive containing an NSIS executable file disguised as “staff record pdf.exe”.
If users have file extensions hidden in their operating system settings, this executable appears as a standard PDF document.

Once executed, the malware initiates a multi-stage infection process designed to evade detection and establish persistent access to the victim’s system.
The Multi-Stage Infection Mechanism
Understanding how Guloader operates reveals the sophisticated nature of this attack.
When the executable runs, it connects to a remote server and downloads encrypted shellcode from a Google Drive URL, specifically from “hxxps://drive.google[.]com/uc?export=download&id=1bzvByYrlHy240MCIX7Cv41gP9ZY3pRsgv” and retrieves a file named “EMvmKijceR91.bin”.
The downloaded shellcode is then injected directly into the system’s memory, allowing the malware to run without writing files to disk.
This memory-only execution technique makes detection significantly more challenging for traditional security solutions that rely on file-based scanning.
The final payload delivered by Guloader is Remcos RAT, a remote access trojan that provides attackers with comprehensive control over infected systems.
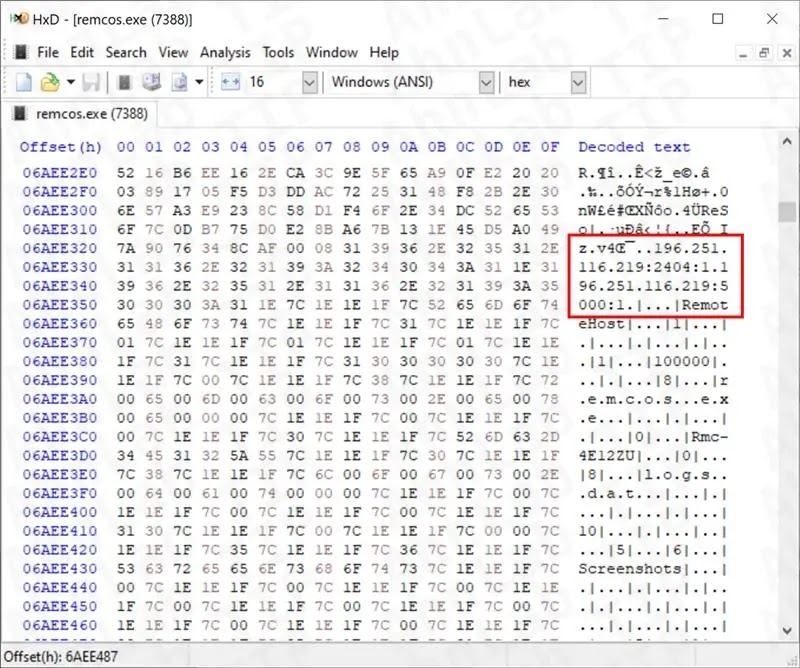
Remcos enables threat actors to perform keylogging, capture screenshots, control webcams and microphones, and extract browser histories along with stored passwords.
The malware communicates with command and control servers located at “196.251.116[.]219” on ports 2404 and 5000, establishing a persistent connection for ongoing unauthorized access.
Organizations should implement email filtering rules to block suspicious attachments, disable file extension hiding in user systems, and deploy advanced endpoint detection and response solutions to identify and block this threat at multiple stages of the attack chain.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.