X Suspends Account for Rule Violation on Its Platform
X has suspended the iconic @twitter handle on its platform, replacing its profile with a standard notice indicating an account rule violation. Screenshots of the suspension screen circulated widely...
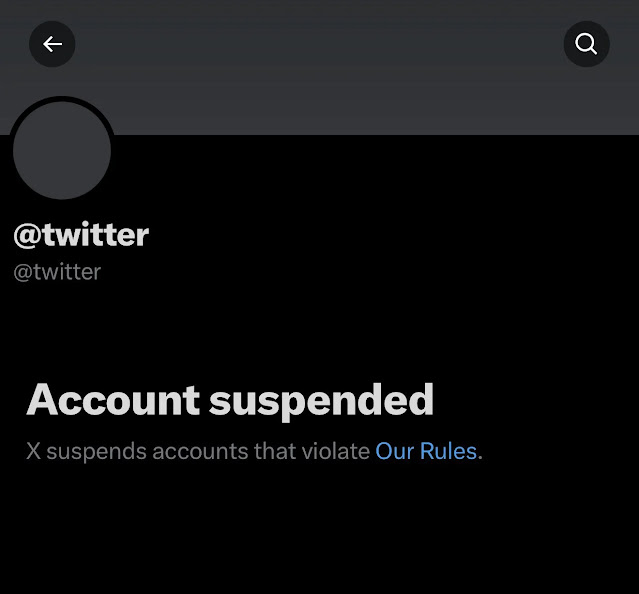
X has suspended the iconic @twitter handle on its platform, replacing its profile with a standard notice indicating an account rule violation. Screenshots of the suspension screen circulated widely late last week, sparking immediate discussions regarding the platform’s rebranding efforts.
The @twitter account had remained inactive since before Elon Musk’s 2022 acquisition of the platform, formerly known as Twitter. Following the 2023 rebrand to X and domain shift to x.com in 2024, the handle symbolized the site’s past identity but saw no new activity.
Visitors now encounter a black screen with white text: “Account suspended X suspends accounts that violate Our Rules,” mirroring notifications for other rule-breaking profiles.
Reports emerged on January 11, 2026, via posts from accounts like @rawsalerts, confirming the suspension of this original handle. News outlets noted it as a final step in erasing Twitter remnants, with the page redirecting users toward @x for updates.
While some observed similar notices months prior, the latest iteration appears permanent, lacking any appeal option typical for active accounts.
Social media buzz mixed nostalgia, “RIP Twitter,” one post lamented with humor about X “suspending its own history.” AI chatbot Grok, built by xAI, described it as a deliberate move to retire legacy branding rather than a true violation.
No official statement from X or Musk addresses specifics, fueling theories from trademark cleanup to automated moderation sweeps.
This suspension underscores X’s ongoing enforcement of its rules against spam, impersonation, and policy breaches, even for dormant profiles.
As “Twitter” lingers in everyday language years post-rebrand, the act closes a chapter, aligning the platform fully under its new identity. Cybersecurity experts note that such moderation aids brand integrity amid rising impersonation threats on social platforms.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.