Browse Category
Comparisons
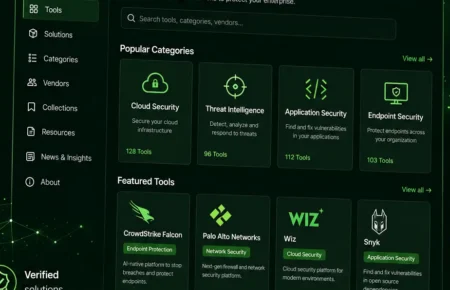
Comparative analysis of security tools, products, services, and solutions. Includes reviews, comparisons, best practices, and recommendations for cybersecurity tools and platforms.
1 Article
Popular
JDownloader Compromised: Malicious Windows & Linux
Malicious JPEG Images Exploit PHP Memory Safety Could Trigger
Critical Linux Kernel Flaw: Read SSH Keys & Passwords
Beyond the Click: A Human-Centric Approach to Phishing Defense
Phishing remains a persistent and evolving threat, often proving...