Attacks
Reports on active cyber attacks, security incidents, breach attempts, and real-world attack campaigns. Covers attack methodologies, techniques, and incident response.
Popular
JDownloader Compromised: Malicious Windows & Linux
Malicious JPEG Images Exploit PHP Memory Safety Could Trigger
Critical Linux Kernel Flaw: Read SSH Keys & Passwords
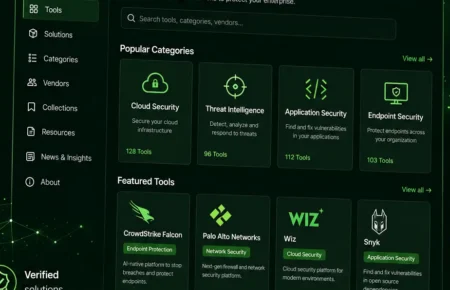
Top 15 Best Ethical Hacking Tools for Cybersecurity
In the dynamic landscape of cybersecurity, utilizing the best...
Top 10 Most Dangerous Injection Attacks to Watch Out for
Cybersecurity professionals, particularly those on network and...
20 Best Malware Protection Solutions In 2026
Malware threats are evolving at an unprecedented pace in the...
10 Most Notable Cyber Attacks of 2026
Driven by rapid technological advancements, increased...
Top 10 Cybersecurity Risk Management Tools for 20 Best
Log360 provides a customizable solution engineered to protect...
Top 10 Best DDoS Protection Tools & Services – 2026
A comprehensive suite of edge services typically integrates...
Discover the 10 Best IT Asset Management Tools for
IT asset management (ITAM) software is now indispensable for...
Top 10 Best Server Monitoring Tools in 2026
Effective server monitoring is crucial for maintaining system...
Malicious Chrome Extension Steals ChatGPT Data from 90
Two rogue Chrome extensions have compromised over 900,000 users,...
INTERPOL Warns of Rising Cyber Attacks in Sharp Rise
INTERPOL Warns of Rising Cyber Attacks in Sharp Rise So,...