INTERPOL Warns of Rising Cyber Attacks in Sharp Rise
INTERPOL Warns of Rising Cyber Attacks in Sharp Rise So, INTERPOL just dropped their 2025 Africa Cyberthreat Assessment Report, and honestly, the findings are pretty stark. We’ This alarming...
INTERPOL Warns of Rising Cyber Attacks in Sharp Rise
So, INTERPOL just dropped their 2025 Africa Cyberthreat Assessment Report, and honestly, the findings are pretty stark. We’
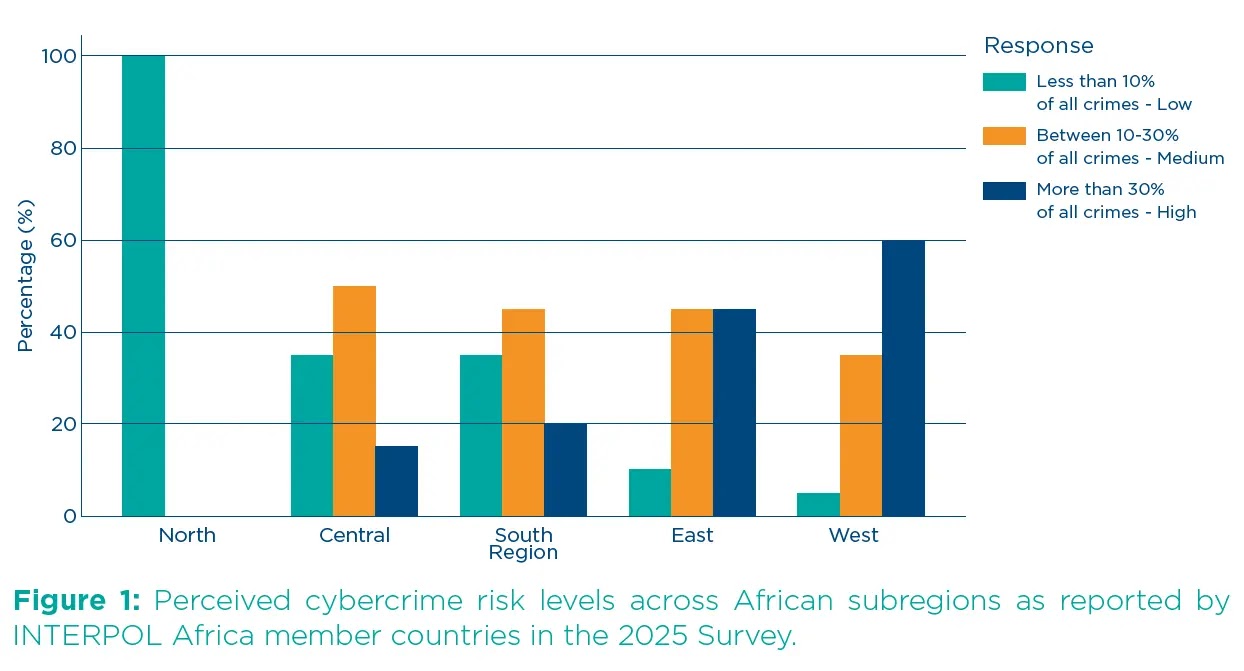
This alarming statistic represents a dramatic shift in the continent’s threat landscape, where two-thirds of African member countries now report that cyber-related offenses constitute a medium-to-high share of all criminal activities.
The emergence of sophisticated cyber threats has transformed the digital security paradigm across the continent, with online scams, ransomware attacks, business email compromise schemes, and digital sextortion campaigns leading the charge.
These attacks have evolved from opportunistic strikes to highly organized criminal enterprises that exploit Africa’s rapidly expanding digital infrastructure and increasing internet penetration rates.
The threat actors behind these campaigns have demonstrated remarkable adaptability, leveraging artificial intelligence and machine learning technologies to enhance their attack vectors and evade traditional detection mechanisms.
Perhaps most concerning is the exponential growth rate of these cyber threats, with suspected scam notifications rising by up to 3,000 percent in some African countries over the past year.
INTERPOL analysts identified this surge as part of a broader pattern of cybercriminal organizations targeting the continent’s emerging digital economies, taking advantage of gaps in cybersecurity infrastructure and law enforcement capabilities.
The scope and sophistication of these attacks have prompted urgent calls for enhanced international cooperation and coordinated response strategies.
Neal Jetton, INTERPOL Cybercrime Director, emphasized the urgency of the situation, stating that the assessment “paints a clear picture of a threat landscape in flux, with emerging dangers like AI-driven fraud that demand urgent attention”.
The report reveals that 90 percent of African countries acknowledge needing significant improvement in their law enforcement or prosecution capacity to address these evolving threats.
This capacity gap has created an environment where cybercriminals can operate with relative impunity, establishing Africa as both a target and a launching pad for international cybercrime operations.
The financial and social impact of these cyber attacks extends far beyond immediate monetary losses, affecting critical infrastructure, government operations, and citizen trust in digital services.
Ambassador Jalel Chelba, Acting Executive Director of AFRIPOL, noted that “cybersecurity has become a fundamental pillar of stability, peace, and sustainable development in Africa,” directly impacting “the digital sovereignty of states, the resilience of institutions, citizen trust and the proper functioning of economies”.
Ransomware Campaign Analysis: Infrastructure Targeting and Persistence Mechanisms
The ransomware threat landscape in Africa has demonstrated unprecedented growth, with detection rates revealing the concentrated nature of these attacks across key economic hubs.
South Africa leads with 17,849 ransomware detections in 2024, followed by Egypt with 12,281 detections, Nigeria with 3,459, and Kenya with 3,030 cases.
These statistics illuminate a clear pattern where cybercriminals are strategically targeting nations with advanced digital infrastructure and significant economic activity.
The attack methodology employed by these ransomware groups reveals sophisticated understanding of African infrastructure vulnerabilities.
Critical infrastructure breaches, such as the attack on Kenya’s Urban Roads Authority (KURA), demonstrate how threat actors are moving beyond traditional targets to disrupt essential services.
Similarly, the compromise of Nigeria’s National Bureau of Statistics (NBS) database highlights the strategic value these attackers place on government data repositories.
These incidents suggest that ransomware operators are conducting extensive reconnaissance phases, identifying high-value targets within government and infrastructure sectors before deploying their payloads.
The persistence mechanisms observed in these campaigns indicate advanced operational security practices.
While specific code analysis remains limited due to the evolving nature of these threats, security researchers have noted the increasing use of living-off-the-land techniques, where attackers leverage legitimate system tools to maintain persistence and avoid detection.
The integration of AI-driven fraud capabilities into these ransomware campaigns represents a concerning evolution, as traditional signature-based detection systems struggle to identify dynamically generated attack patterns.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.