Deep#Door Stealer Harvests Passwords, Cloud Browser Tokens
Cybersecurity researchers have identified a new Python-based malware, dubbed The malware enters a target system through an obfuscated batch script, typically named “finallyJob.bat”, which acts as the...
Cybersecurity researchers have identified a new Python-based malware, dubbed
The malware enters a target system through an obfuscated batch script, typically named “finallyJob.bat”, which acts as the initial execution trigger.
Rather than relying on external payload downloads, DEEP#DOOR uses a self-contained approach, embedding the full Python backdoor directly within the batch file itself.
This design drastically reduces the chances of network-based detection tools catching the threat before it takes hold.
The infection begins the moment a user opens what appears to be a routine batch file on a Windows machine.
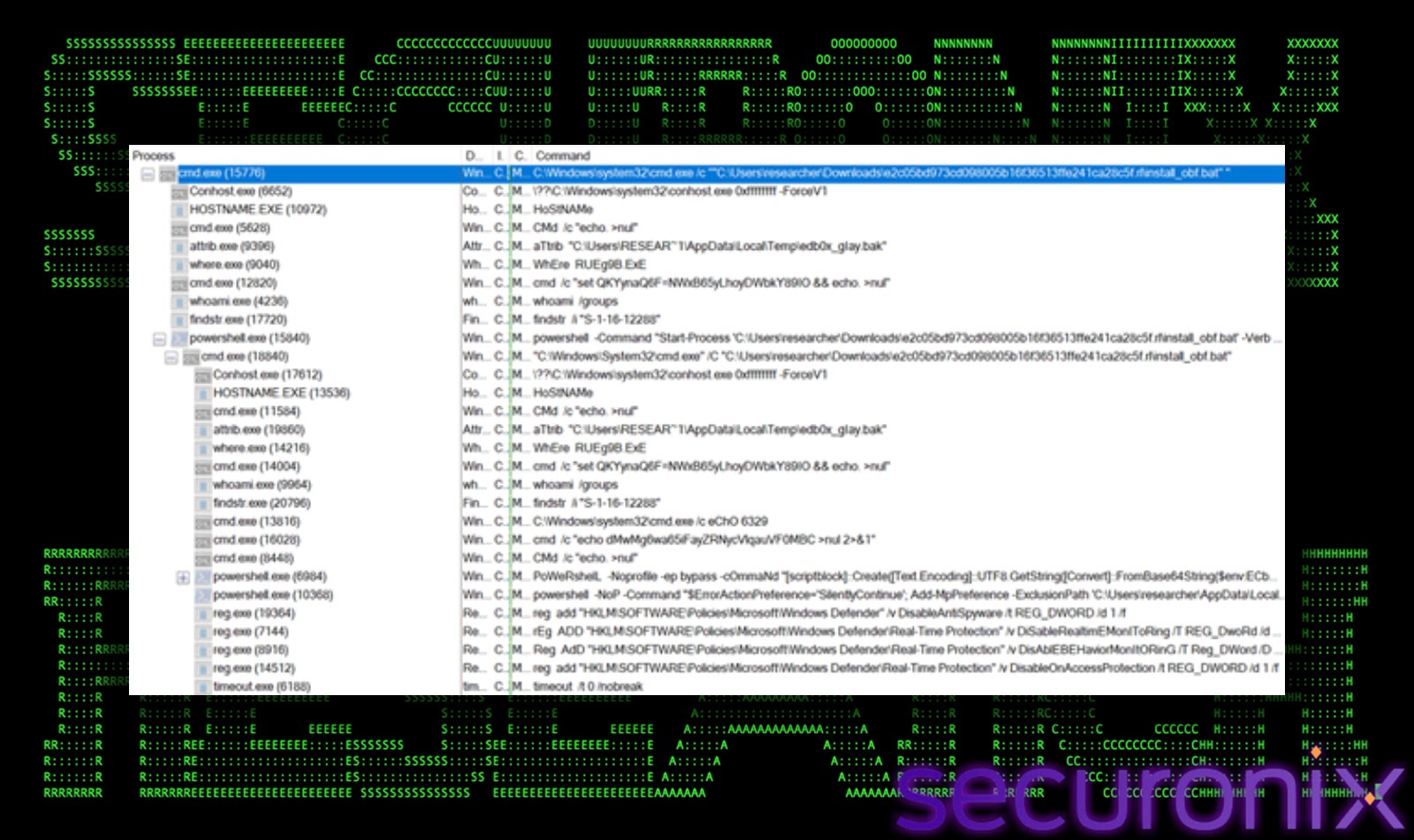
Securonix Threat Research analysts identified and analyzed this Python-based backdoor framework, dubbed DEEP#DOOR, which operates as an obfuscated batch loader designed to deploy a persistence and credential-stealing implant on Windows systems.
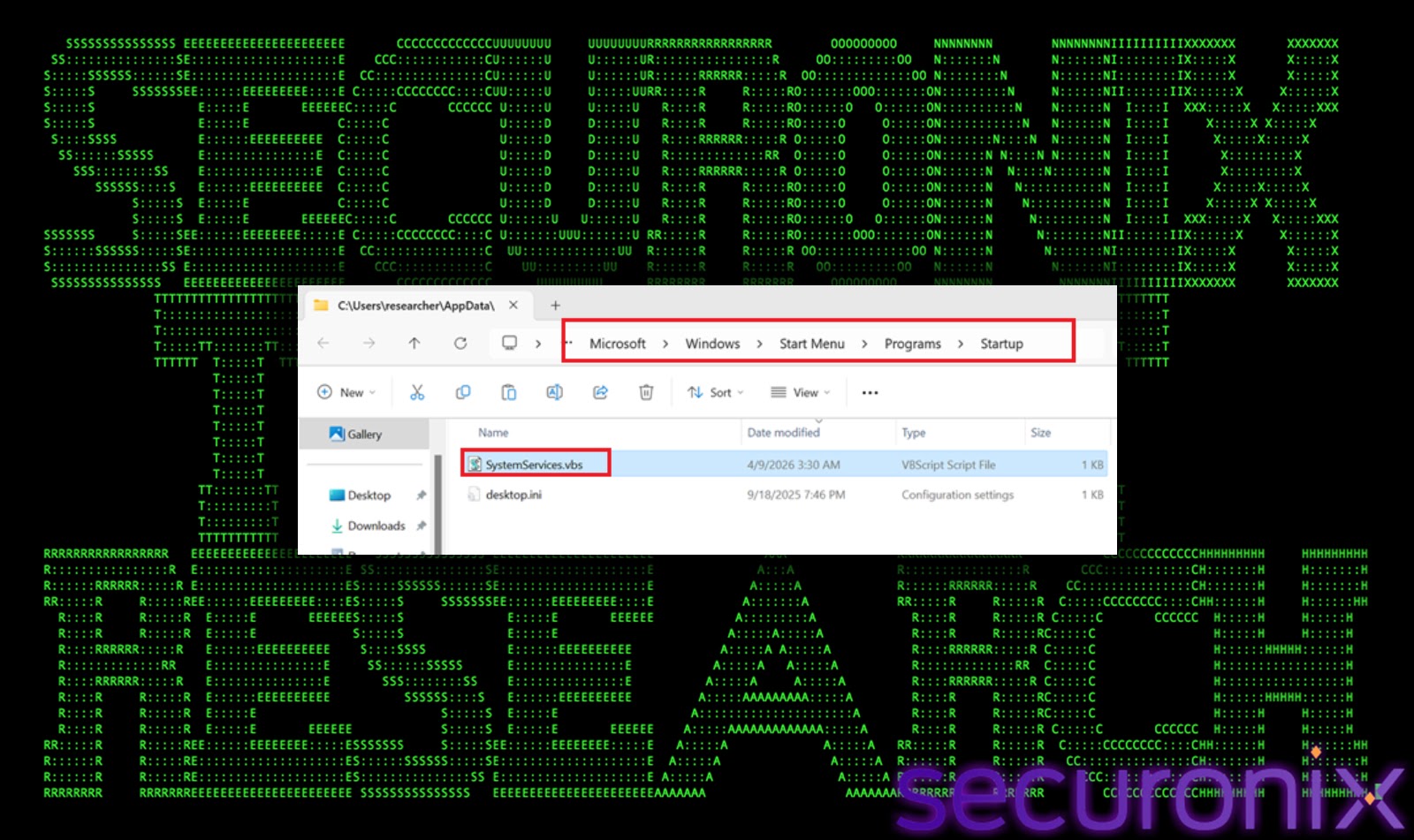
The researchers noted that the infection chain begins with execution of a batch script that dynamically extracts and runs an embedded Python Remote Access Tool payload (c.py), and establishes persistence through Startup folder scripts, Registry Run keys, Scheduled Tasks, and optional WMI subscriptions.
Once active, the malware establishes communication with attacker-controlled infrastructure through a publicly available TCP tunneling service, enabling remote operators to interact through dedicated ports.
The backdoor then enables full remote command execution and surveillance capabilities including keylogging, webcam photo capture, microphone recording, screen capture, and credential harvesting.
Before deploying the Python backdoor, DEEP#DOOR also evades runtime defenses by disabling SmartScreen, patching AMSI and ETW, clearing event logs, and using timestamp stomping to conceal its activity.
The malware further incorporates sandbox detection, unhooking, Windows Defender tampering, and command-line stripping.
The resulting implant operates as a fully-featured Remote Access Tool capable of long-term persistence, lateral movement, and post-exploitation within compromised environments. This combination of evasion and remote control makes DEEP#DOOR exceptionally difficult to detect once it has taken hold inside a network.
How DEEP#DOOR Steals Your Credentials
The most damaging capability of DEEP#DOOR is its broad credential-harvesting engine.
It methodically targets browser-stored passwords, cloud authentication tokens, sensitive environment credentials, and SSH access keys, enabling lateral movement and account compromise across targeted infrastructure.
The stealer calls the get_chrome_cred() and get_edge_cred() functions to access browser SQLite databases and extract stored login data.
A dedicated get_ssh_key() function discovers and exfiltrates private SSH keys used for remote server access.
The malware also runs get_cloud_cred() to search configuration files and environment variables containing AWS, Azure, and GCP credentials. In addition, get_wifi_cred() scans the Windows Credential Manager and related registry locations to pull saved Wi-Fi passwords.
This multi-vector collection means a single infection can expose an entire organization’s access surface in one sweep. Once these credentials are in the attacker’s hands, re-entry into the network becomes trivial even after the malware is detected and removed from the original host.
Organizations and security teams should apply the following steps to reduce exposure from DEEP#DOOR.
Avoid opening unknown batch files or script attachments, especially those received through email or shared links. Monitor for unusual PowerShell and cmd.exe activity combined with Base64-encoded commands.
Audit Registry Run keys, Startup folders, and Scheduled Tasks regularly for unauthorized entries. Enable Windows Defender tamper protection to prevent the malware from disabling built-in security features.
Rotate cloud authentication tokens and SSH keys regularly following any suspected compromise. Deploy network monitoring to detect suspicious outbound tunneling traffic over non-standard ports.
Investigate any process making unexpected webcam, microphone, or screen capture calls. Isolate affected systems promptly and conduct forensic analysis to identify lateral movement paths.
Because DEEP#DOOR relies on Python-based execution and obfuscated scripting rather than compiled binaries, traditional antivirus tools may offer limited coverage.
Behavioral analytics and anomaly detection should serve as the primary defense layer for organizations looking to stay protected against evolving threats of this nature.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.