China-Aligned Attackers Use ShadowPad, IOX Proxy WMIC Multi-Stage
A China-aligned threat group is conducting a sophisticated, multi-stage espionage campaign against government agencies and critical infrastructure across Asia, according to a new report detailing the...
A China-aligned threat group is conducting a sophisticated, multi-stage espionage campaign against government agencies and critical infrastructure across Asia, according to a new report detailing the threat activity. This meticulously planned operation involves the use of tools like ShadowPad and IOX Proxy, alongside Windows Management Instrumentation Command-line (WMIC), to compromise critical networks for intelligence gathering.
The group, tracked under the temporary designation SHADOW-EARTH-053, has been active since at least December 2024, quietly targeting organizations in at least eight countries.
The campaign uses a combination of malware tools and living-off-the-land techniques to stay hidden inside victim networks for as long as possible.
The attackers gain initial access by exploiting known but unpatched vulnerabilities in Microsoft Exchange and Internet Information Services (IIS) servers.
The group specifically targeted the ProxyLogon vulnerability chain, which includes CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065.
Even though patches for these flaws have long been available, many organizations still run unpatched Exchange servers, making them easy targets.
Once inside, the attackers deploy web shells such as GODZILLA to maintain persistent backdoor access and execute remote commands at will.
Trend Micro researchers Daniel Lunghi and Lucas Silva identified this campaign through ongoing analysis of ShadowPad implants targeting South and Southeast Asia.
Their investigation uncovered a related cluster, SHADOW-EARTH-054, sharing identical tool hashes and overlapping attack methods.
In nearly half of the targeted environments, both clusters compromised the same organizations, with victims confirmed in Pakistan, Thailand, Malaysia, India, Myanmar, Sri Lanka, Taiwan, and Poland.
The research team assessed that these operations align with China’s broader strategic interests and are most likely aimed at cyberespionage and intellectual property theft.
The primary malware used is ShadowPad, a modular backdoor first used by APT41 in 2017 and later shared among multiple China-aligned groups starting in 2019.
Beyond ShadowPad, the attackers deployed IOX proxy to create covert communication channels, used Windows Management Instrumentation Command-line (WMIC) for lateral movement, and relied on open-source tunneling tools including GOST and Wstunnel to tunnel traffic over SOCKS5 and HTTPS connections to external infrastructure.
How the Attack Unfolds: ShadowPad’s Infection Mechanism
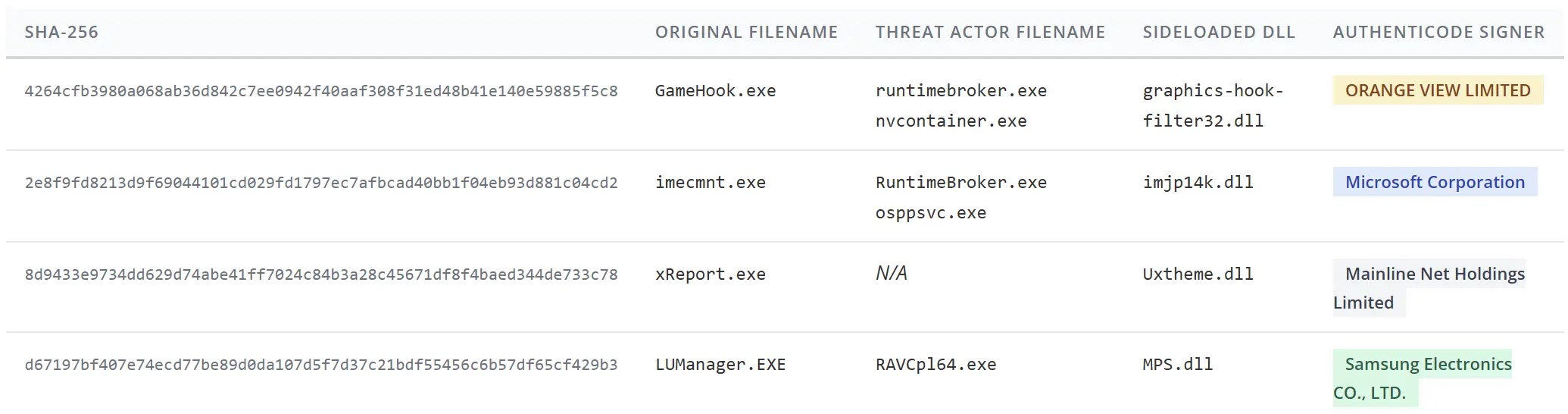
The way ShadowPad is loaded onto victim machines is one of the more technically notable parts of this campaign. The attackers use a DLL sideloading technique, placing a malicious DLL alongside a legitimate signed executable.
When the legitimate program runs, it unknowingly loads the malicious DLL instead. The group abused executables from vendors including Toshiba, Samsung, and Microsoft, renaming them to blend in with normal system activity.
What makes this loader especially stealthy is that the ShadowPad payload is not stored inside the DLL itself. Instead, the loader retrieves an encrypted payload from a machine-specific registry key at HKEY_CURRENT_USERSoftware.
Persistence was maintained through a scheduled task named “M1onltor,” configured to run the sideloaded binary every five minutes with the highest available privileges.
WMIC was then used to push backdoors onto additional hosts, and credential-harvesting tools including Mimikatz and Evil-CreateDump were executed through IIS worker processes to extract passwords and account data.
Organizations running internet-facing Microsoft Exchange or IIS servers should apply the latest security patches immediately, as the ProxyLogon vulnerability chain remains an active entry point for this group.
Where patching is not possible right away, deploying Intrusion Prevention Systems (IPS) or Web Application Firewalls (WAF) with virtual patching rules is strongly advised.
Security teams should implement File Integrity Monitoring (FIM) on critical web directories and configure alerts for any new or modified .aspx, .ashx, or .jsp files.
Endpoint Detection and Response (EDR) telemetry should be reviewed for IIS worker processes spawning command shells or reconnaissance tools.
Directories such as C:UsersPublic and C:ProgramData should be closely watched, as the group consistently used these as staging areas throughout the campaign.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.