Phoenix PhaaS Fuels Brand Smishing in Finance Platform Drives
Phoenix, a potent new Phishing-as-a-Service (PhaaS) platform, is quietly expanding its global footprint, fueling a concerning rise in brand impersonation smishing. Attackers are leveraging this...
Phoenix, a potent new Phishing-as-a-Service (PhaaS) platform, is quietly expanding its global footprint, fueling a concerning rise in brand impersonation smishing. Attackers are leveraging this platform to deploy fake SMS messages, meticulously crafted to mimic legitimate communications from trusted entities across the finance, telecom, and logistics sectors. Its operations and impact are detailed in a
This platform works on a subscription basis, making it easy for cybercriminals with limited technical skills to launch large-scale smishing campaigns in minutes.
Phishing-as-a-Service, or PhaaS, has become one of the fastest-growing threats in the cybercrime world. Instead of building tools from scratch, cybercriminals now rent ready-made phishing kits that come with pre-built templates, real-time dashboards, and automated victim tracking.
The Phoenix System builds on this model by offering a centralized administrative panel that lets operators manage multiple phishing campaigns at once across different countries and industries.

Since January 2024, the platform has been linked to two primary campaign types: Reward Points Phishing, which impersonates banks and mobile operators, and Failed Parcel Delivery Phishing, which impersonates logistics and shipping companies.

Group-IB researchers uncovered the Phoenix System while analyzing global smishing operations spanning APAC, LATAM, Europe, and MEA regions.
The investigation revealed that despite targeting different industries and victim groups, both campaign types share the same backend infrastructure, confirming they are not separate operations but part of a single, organized phishing ecosystem.
The platform is the direct successor to an earlier tool known as the Mouse System, which has since been decommissioned.
The Phoenix System inherits much of the same JavaScript logic and administrative framework from its predecessor, with significant updates that make it harder to detect and easier to operate at scale.
So far, the campaigns driven by Phoenix have targeted more than 70 organizations worldwide, with over 1,500 phishing domains identified since the beginning of 2024.
What makes Phoenix particularly alarming is its combination of speed, flexibility, and evasion capabilities. Operators can configure campaigns for specific countries using geofencing and IP filtering controls, ensuring that only victims from the intended region ever see the phishing content.
The platform charges around $2,000 for annual access and is distributed through dedicated Telegram channels.
Inside the Phoenix Phishing Panel
One of the most technically notable aspects of Phoenix is its centralized administrative panel, which gives operators full control over every stage of a phishing campaign.
Once configured, the panel allows operators to oversee active campaigns, set traffic filtering rules by IP range or device type, and monitor all harvested credentials in real time through a live dashboard.
The smishing messages are delivered using a combination of ordinary mobile numbers and Base Transceiver Station injection.
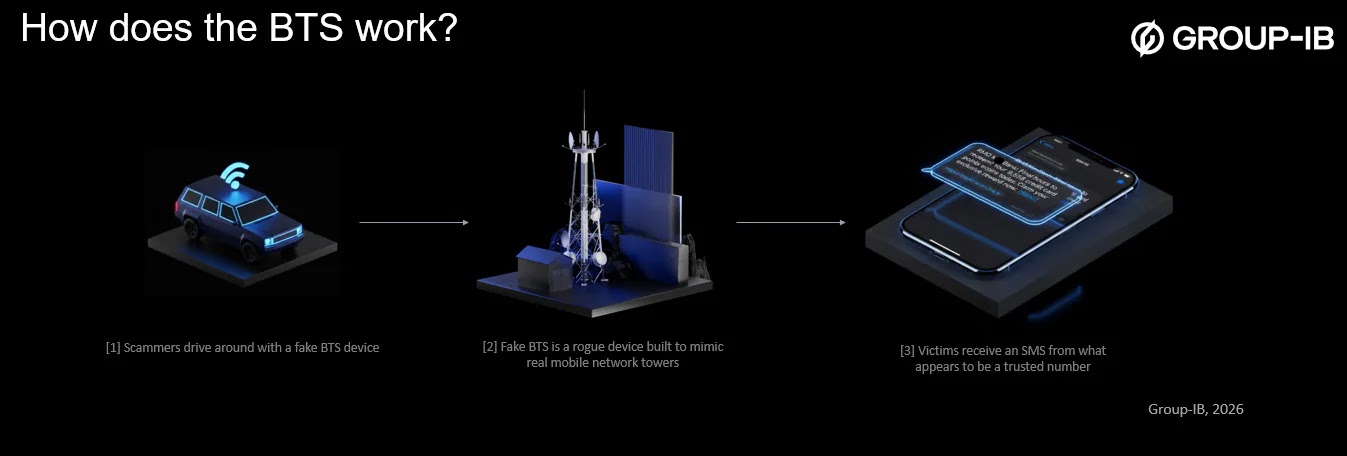
BTS-based delivery involves rogue equipment that broadcasts stronger signals than legitimate towers, forcing nearby devices to connect and receive injected SMS messages directly.
Since these messages bypass carrier-level filtering, they appear to arrive from legitimate sender names and branded short codes, making them much harder for both users and telecom operators to detect.
When a victim clicks the link inside the SMS, the phishing page first checks the visitor’s IP address and device type.
Only users from the targeted country and on approved devices can see the fraudulent page.
Everyone else is silently redirected to an error page or a default system redirect, effectively hiding the infrastructure from security researchers.
The phishing pages are crafted to closely mimic official websites of well-known brands with matching logos, layouts, and wording.
Victims are first prompted to enter their phone number to check reward status or update delivery details.
After submission, they are taken through a series of pages that collect full credit card details, shipping addresses, and personally identifiable information.
Organizations can reduce their exposure by continuously monitoring for SMS-linked brand abuse and tracking newly registered domains.
Telecom teams should enable rapid takedown workflows and coordinate with carriers when BTS-based injection is suspected.
Individual users should avoid clicking links inside unsolicited SMS messages, verify any alerts through official apps or websites, and never enter payment or personal details through links received by text.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.