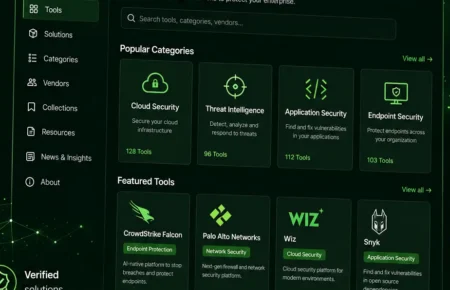
Vulnerability
Weaknesses in software, hardware, systems, or processes that attackers exploit for unauthorized access, data theft, or disruption. Covers discoveries, CVEs, …
Popular
JDownloader Compromised: Malicious Windows & Linux
Malicious JPEG Images Exploit PHP Memory Safety Could Trigger
Critical Linux Kernel Flaw: Read SSH Keys & Passwords
Pwn2Own Day 2: Microsoft Exchange, Win Windows Cursor
Day Two of Pwn2Own Berlin 2026 delivered a fresh wave of...
JDownloader Compromised: Malicious Windows & Linux
JDownloader, a download manager widely trusted by millions,...
Malicious JPEG Images Exploit PHP Memory Safety Could Trigger
Two critical memory-safety vulnerabilities in PHP’s...
Critical Linux Kernel Flaw: Read SSH Keys & Passwords
A newly disclosed Linux kernel vulnerability is raising serious...
Google Project Zero Reveals Pixel 10 Zero- Discloses Zero-Click
A newly disclosed zero-click exploit chain, targeting Google...
Android 16 VPN Bypass Exposes User IP Lets Malicious
A recently disclosed vulnerability in Android 16 has ignited...
Hackers Abuse OAuth Flow to Steal Microsoft Device Authorization
Attackers are abusing a lesser-known element within...
Microsoft Warns: Attackers Use HPE Agent for Malware-
Microsoft has issued a warning concerning a sophisticated attack...
Critical cPanel Flaws Allow Access to Sensitive System
A critical wave of security vulnerabilities impacting cPanel and...
Amazon Redshift JDBC Driver Flaws Allow Remote Code Execution
A critical vulnerability within the Amazon Redshift JDBC driver...