Malicious Chrome Extension Steals ChatGPT Data from 90
Two rogue Chrome extensions have compromised over 900,000 users, illicitly exfiltrating sensitive data including ChatGPT and DeepSeek conversations, alongside full browsing histories, to...
Two rogue Chrome extensions have compromised over 900,000 users, illicitly exfiltrating sensitive data including ChatGPT and DeepSeek conversations, alongside full browsing histories, to attacker-controlled servers. This widespread data breach highlights a significant threat from malicious browser add-ons, with reports indicating identified the threat during routine analysis, revealing extensions that clone AITOPIA’s interface for chatting with LLMs like GPT and Claude.
Table Of Content
Named “Chat GPT for Chrome with GPT-5, Claude Sonnet & DeepSeek AI” (600K+ users, ID: fnmihdojmnkclgjpcoonokmkhjpjechg, version 1.9.6) and “AI Sidebar with Deepseek, ChatGPT, Claude and more” (300K+ users, ID: inhcgfpbfdjbjogdfjbclgolkmhnooop), they request “anonymous analytics” consent to mask data theft.
Threat actors host privacy policies on Lovable.dev to obscure origins, and uninstalled extensions redirect to the other.
How the Malware Operates
Installed extensions monitor tabs via chrome.tabs.onUpdated API, generating a unique “gptChatId” per victim. On detecting chatgpt.com or deepseek.com URLs, they scrape DOM elements for prompts, responses, and session IDs, storing data locally before Base64-encoding and sending batches to C2 servers like deepaichats.com or chatsaigpt.com every 30 minutes.
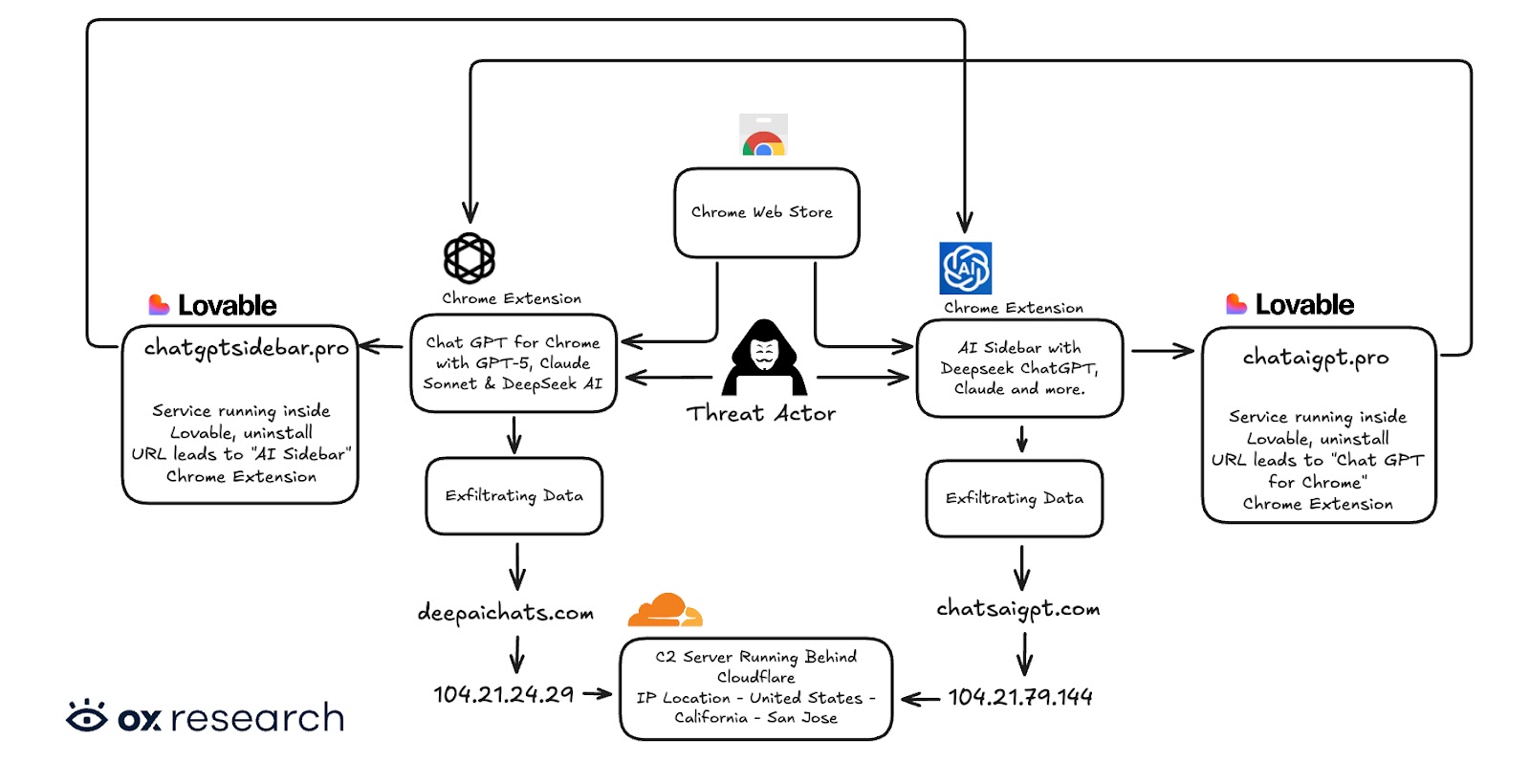
This captures proprietary code, business strategies, PII, search queries, and internal URLs missed by AITOPIA’s disclosed server storage.
Stolen chats risk exposing intellectual property, corporate secrets, and personal data for espionage or sale on dark web forums. Browsing logs reveals habits, tokens, and org structures, enabling phishing or identity theft across affected enterprises.
As of January 7, 2026, both extensions remain downloadable, with the first stripped of its “Featured” status post-disclosure but updated as recently as October 2025.
Users should visit Chrome Extension, AI Sidebar. Avoid unverified extensions regardless of badges; stick to reputable sources.
IoCs
| Type | Value | Notes |
|---|---|---|
| Extension name | Chat GPT for Chrome with GPT-5, Claude Sonnet & DeepSeek AI | Malicious Chrome Extension |
| Extension ID | fnmihdojmnkclgjpcoonokmkhjpjechg | Chrome Web Store ID |
| Version | 1.9.6 | Reported malicious build |
| SHA-256 hash | 98d1f151872c27d0abae3887f7d6cb6e4ce29e99ad827cb077e1232bc4a69c00 | Package hash |
| Extension name | AI Sidebar with Deepseek, ChatGPT, Claude and more | Second malicious extension |
| Extension ID | inhcgfpbfdjbjogdfjbclgolkmhnooop | Chrome Web Store ID |
| Version | 1.6.1 | Reported malicious build |
| SHA-256 hash | 20ba72e91d7685926c8c1c5b4646616fa9d769e32c1bc4e9f15dddaf3429cea7 | Package hash |
Network and C2 IoCs
| Category | Domain / Endpoint | Notes |
|---|---|---|
| C2 endpoint | deepaichats[.]com | Receives stolen chat data and URLs |
| C2 endpoint | chatsaigpt[.]com | Additional C2 for exfiltrated data |
| Lovable-hosted server | chataigpt[.]pro | Used for privacy policy / infra hosting |
| Lovable-hosted server | chatgptsidebar[.]pro | Used for uninstall redirect and infra |
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.