ValleyRAT_S2 Malware Steals Financial Details from Organizations
The ValleyRAT_S2 malware is behind a new series of attacks, designed to covertly breach organizations, maintain persistence, and pilfer critical financial details. ValleyRAT_S2 is the second-stage...
The ValleyRAT_S2 malware is behind a new series of attacks, designed to covertly breach organizations, maintain persistence, and pilfer critical financial details.
ValleyRAT_S2 is the second-stage payload of the ValleyRAT family and is written in C++. Once inside a network, it behaves like a full remote access trojan, giving attackers strong control over infected systems and a reliable way to move data out.
The current campaign spreads mainly through fake Chinese-language productivity tools, cracked software, and trojanized installers that pose as AI-based spreadsheet generators.
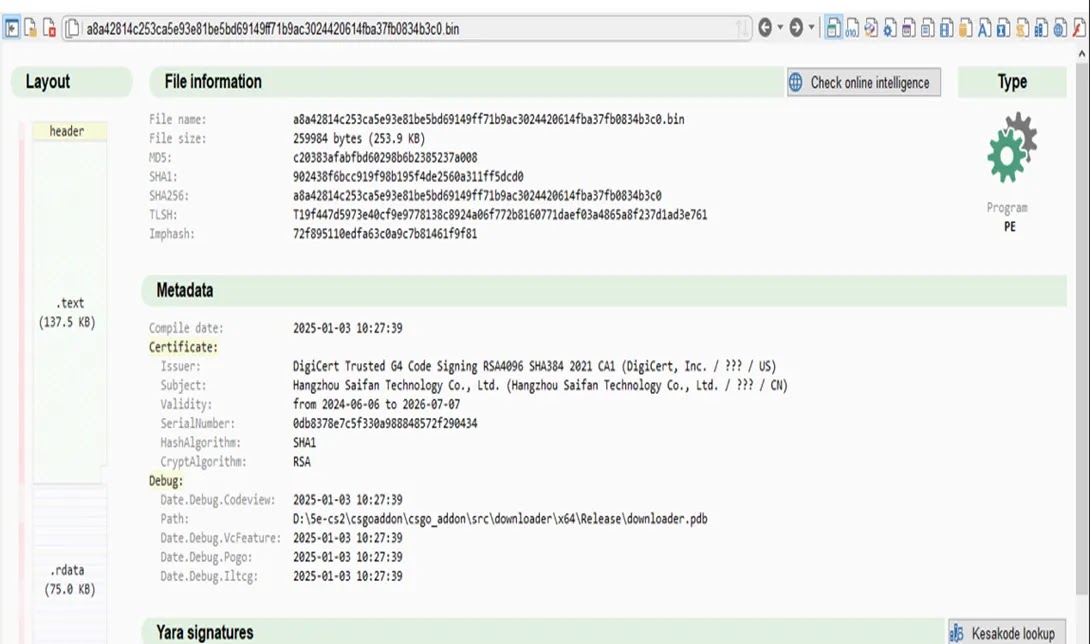
In many cases, the malware is delivered through DLL side‑loading, where a legitimate signed application is tricked into loading a malicious DLL named like a normal library, such as steam_api64.dll.
After tracking these operations, APOPHiS identified ValleyRAT_S2 as the core second-stage backdoor driving these intrusions.
The malware also arrives through spearphishing attachments and abused software update channels.
Malicious documents and archives drop payloads into locations like the Temp folder, for example:-
C:UsersAdminAppDataLocalTempAI自动化办公表格制作生成工具安装包steam_api64.dll.
From there, Stage 1 focuses on evasion, while ValleyRAT_S2 takes over long-term control, system discovery, credential theft, and financial data collection.
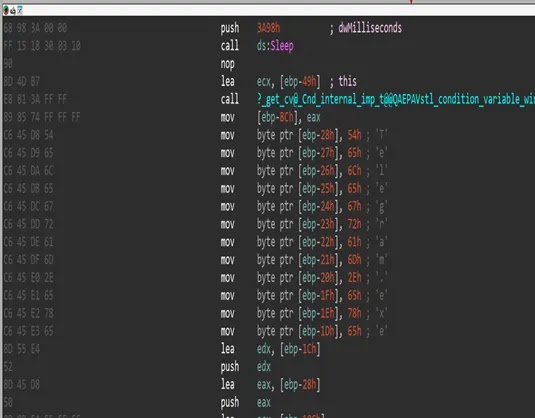
Once active, ValleyRAT_S2 scans processes, file systems, and registry keys, then reaches out to hardcoded command‑and‑control servers such as 27.124.3.175:14852 over a custom TCP protocol. It can upload and download files, run shell commands, inject payloads, and capture keystrokes.
This makes it well-suited for harvesting online banking credentials, payment data, and internal financial documents.
Persistence and watchdog behavior
One of the most dangerous parts of ValleyRAT_S2 is its layered persistence and watchdog design, which helps it survive reboots and manual cleanup.
The malware first stages files in the user’s Temp and AppData paths, creating markers such as %TEMP%target.pid and configuration paths under %APPDATA%PromotionsTemp.aps.
It also abuses Windows Task Scheduler through COM APIs to re‑run itself on startup, and may use registry run keys for backup startup paths.
A key feature is a generated batch script, monitor.bat, which acts as a watchdog loop.
The script reads the stored process ID from target.pid, checks if the main malware process is still running, and silently restarts it if needed.
A simplified version looks like this:-
@echo off
set "PIDFile=%TEMP%target.pid"
set /p pid=<"%PIDFile%"
del "%PIDFile%"
:check
tasklist /fi "PID eq %pid%" | findstr >nul
if errorlevel 1 (
cscript //nologo "%TEMP%watch.vbs"
exit
)
timeout /t 15 >nul
goto checkThis loop allows ValleyRAT_S2 to recover if security tools or admins kill the main process. Combined with structured exception handling, sandbox checks, and process injection into trusted names like Telegra.exe and WhatsApp.exe, the malware maintains a quiet but strong presence.
For defenders, this means simple process killing is not enough; full removal must target the scheduled tasks, batch and VBS watchdog scripts, staged files, and the backdoor process all at once.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.