Cybercriminal Cryptocurrency Transactions Peaked in 2025 Following
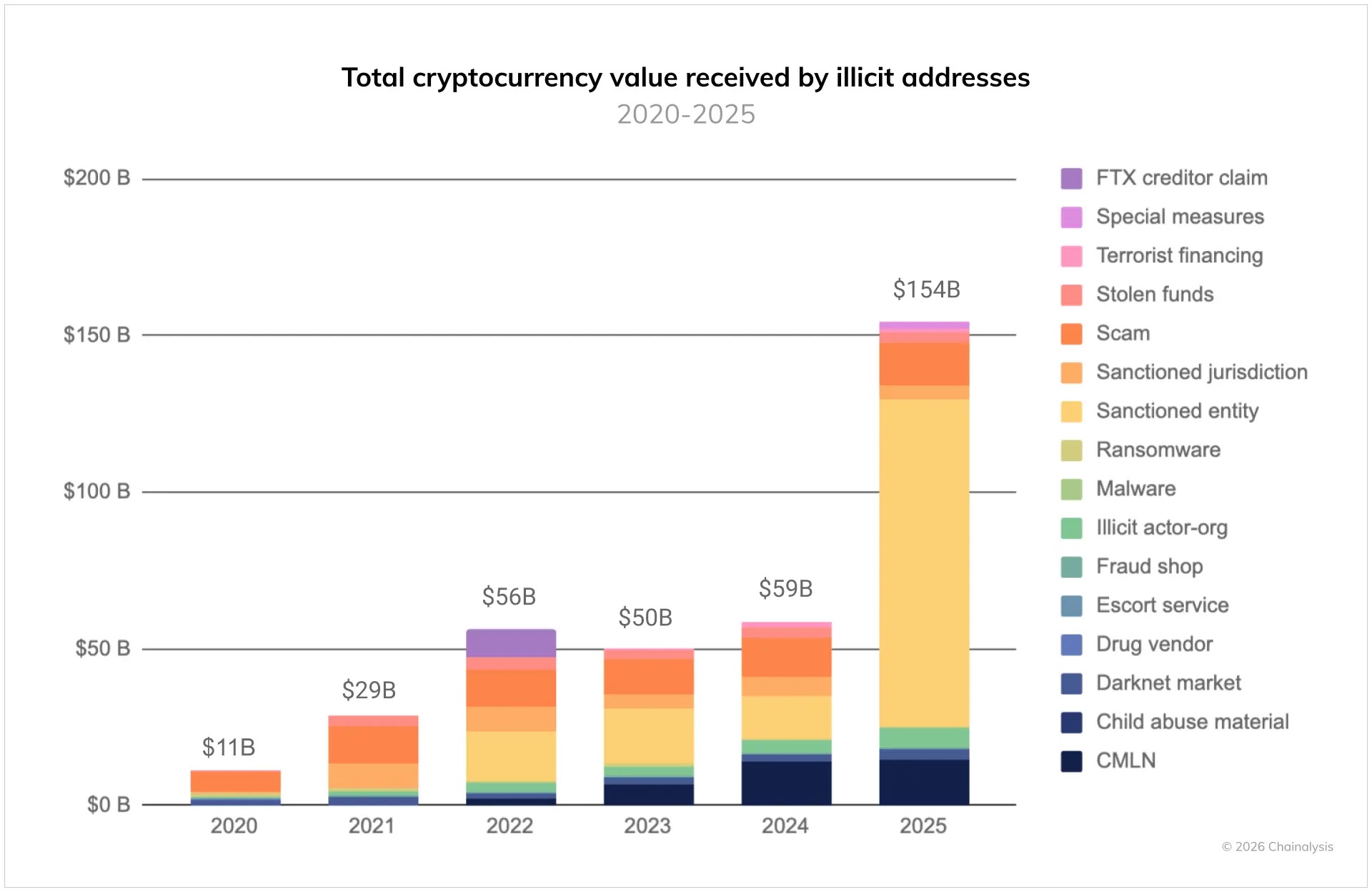
Illicit cryptocurrency addresses received at least $154 billion in 2025, a figure that represents an unprecedented peak in the cryptocurrency crime landscape. This staggering figure represents a 162...
Illicit cryptocurrency addresses received at least $154 billion in 2025, a figure that represents an unprecedented peak in the cryptocurrency crime landscape.
This staggering figure represents a 162 percent increase compared to the previous year, driven largely by nation-states moving into cryptocurrency ecosystems to evade international sanctions at scale.
The shift marks a critical turning point where geopolitical tensions are now directly manifesting within blockchain networks, creating new challenges for regulatory bodies and security teams worldwide.
Over the past few years, the crypto crime ecosystem has become remarkably professionalized.
Illicit actors have developed sophisticated on-chain infrastructure to support transnational criminal networks, enabling them to procure goods and services while laundering stolen digital assets.
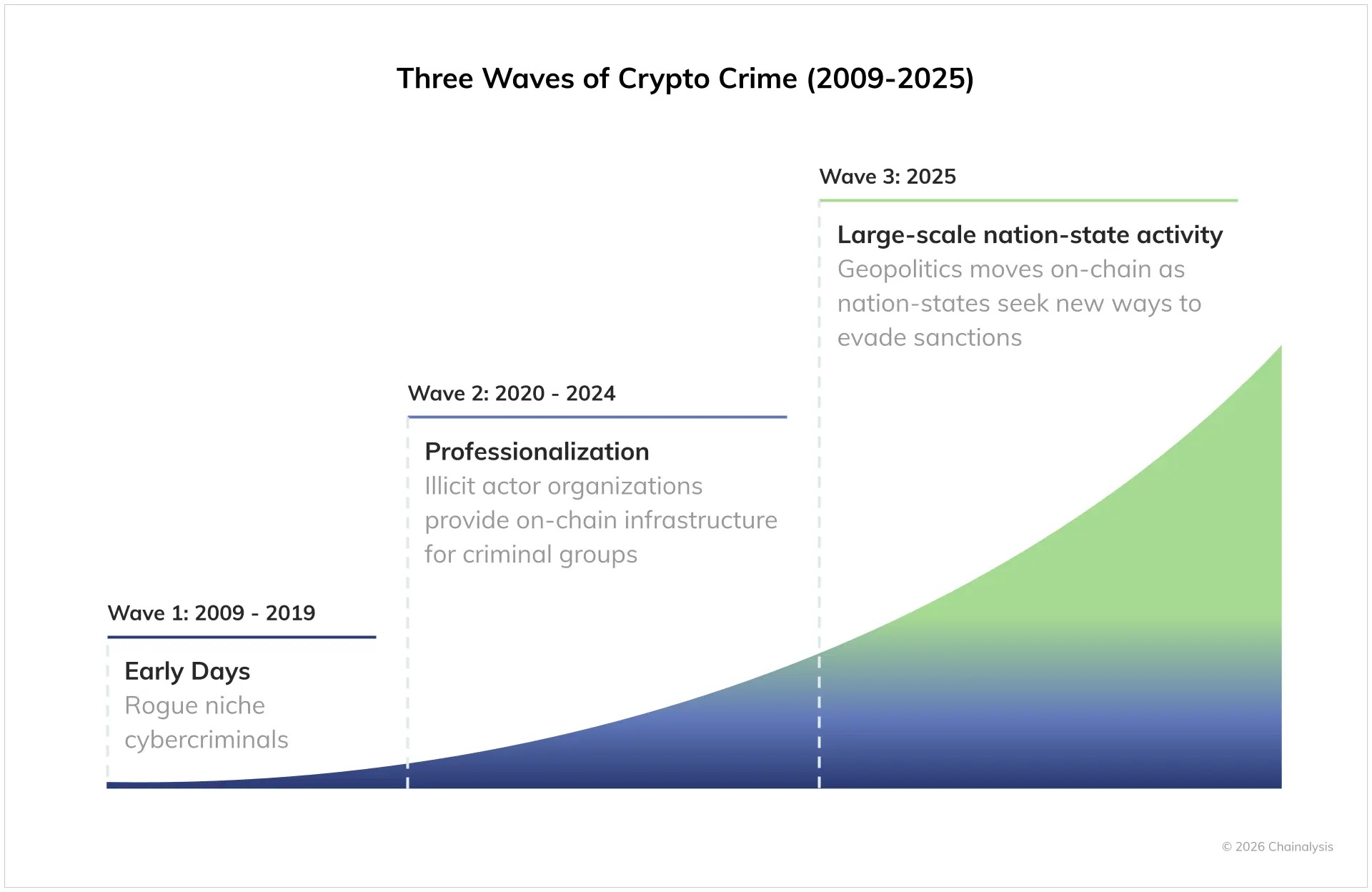
The landscape has evolved through distinct waves: from early rogue cybercriminals operating in isolated niches between 2009 and 2019, to organized illicit actor organizations providing infrastructure services from 2020 to 2024, and now to 2025’s large-scale nation-state activity fundamentally reshaping the entire ecosystem.
Chainalysis analysts identified that this transformation represents the maturation phase of illicit on-chain infrastructure, where government agencies now face significantly higher stakes on both consumer protection and national security fronts.
The most striking development involves Russia’s creation of the ruble-backed A7A5 token in February 2025.
This purpose-built infrastructure processed over 93.3 billion in transactions within less than one year, demonstrating how nation-states have shifted from theoretical sanctions evasion strategies to operational on-chain activities.
Stablecoin Dominance and Infrastructure Evolution
The technical shift in illicit cryptocurrency activity reveals a critical pattern in asset utilization.
Stablecoins now account for 84 percent of all illicit transaction volume, up from smaller percentages in previous years.
Their practical advantages including easy cross-border transferability, lower volatility, and broader utility across trading platforms have made them the preferred choice for actors seeking to move value quickly and securely.
Beyond direct nation-state participation, Chainalysis researchers documented how North Korean-linked hackers stole over 2 billion in 2025, including the February Bybit exploit marking the largest digital heist in cryptocurrency history at nearly 1.5 billion.
Simultaneously, Iranian proxy networks facilitated money laundering operations totaling 2 billion through confirmed wallets in sanctions designations, while Chinese money laundering networks emerged as dominant forces providing full-service criminal infrastructure including laundering-as-a-service capabilities.
This professionalization of illicit infrastructure now supports everything from traditional ransomware operations to state-level sanctions evasion, representing a fundamental restructuring of cryptocurrency crime itself.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.