ODINI Malware Breaches Air-Gapped Exploits Magnetic
Capable of breaching air-gapped computers secured by Faraday cages, ODINI is a sophisticated proof-of-concept malware designed to extract sensitive information. By modulating the targeted computer’s...
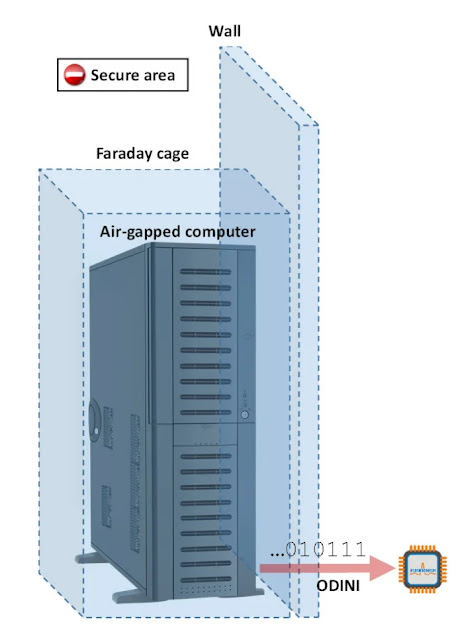
Capable of breaching air-gapped computers secured by Faraday cages, ODINI is a sophisticated proof-of-concept malware designed to extract sensitive information.
By modulating the targeted computer’s CPU workload to generate low-frequency magnetic fields, this covert channel successfully transmits data through advanced physical isolation barriers.
Developed by a team led by Mordechai Guri at Israel’s Ben-Gurion University, the ODINI research highlights severe vulnerabilities in environments traditionally deemed impenetrable.
Organizations in the military, financial, and critical infrastructure sectors heavily rely on air-gapped systems and Faraday cages to shield sensitive data from electromagnetic interference and remote network intrusions.
Despite these robust precautions, ODINI demonstrates that motivated threat actors who initially infect a system via supply-chain attacks or compromised USB drives can still retrieve high-value assets, such as passwords, authentication tokens, and encryption keys.
ODINI Malware on Air-Gapped Networks
The core exfiltration mechanism of ODINI relies entirely on the precise manipulation of the compromised machine’s central processing unit.
The malware intentionally overloads the CPU cores with calculations, causing dynamic fluctuations in power consumption that inherently generate low-frequency magnetic fields.
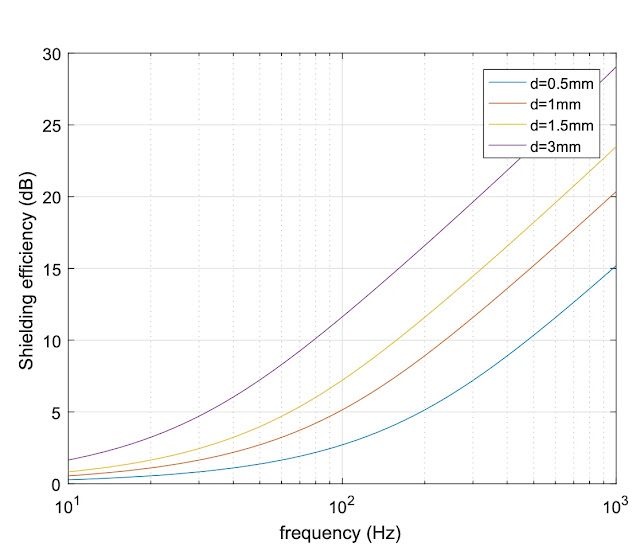
Because low-frequency magnetic waves have extremely low impedance, they easily penetrate standard computer chassis components and the solid metal shielding of Faraday cages.
The transmitting code requires no elevated administrative privileges to execute its tasks and utilizes simple processor operations to evade detection by conventional antivirus software or runtime monitoring tools.
Furthermore, the malware uses advanced data modulation schemes, including amplitude-shift keying and frequency-shift keying, to encode the stolen information onto the magnetic waves accurately, Mordechai Guri said.
Once the data is encoded and broadcast as a magnetic signal, an attacker must position a receiving device nearby to capture the covert emanations.
The ODINI technique utilizes a dedicated magnetic sensor located within a physical range of 100 to 150 centimeters from the compromised machine, achieving a maximum data transfer rate of 40 bits per second.
A parallel attack variant, named MAGNETO, exploits the identical CPU manipulation technique but uses an infected smartphone’s built-in magnetometer as the receiver.
MAGNETO is effective at distances up to 12.5 centimeters and transfers data at 5 bits per second, notably functioning even if the receiving smartphone is placed inside a Faraday bag or switched to airplane mode.
Defending against magnetic field exfiltration poses a substantial engineering challenge for security operations centers.
Conventional Faraday cages cannot block these low-frequency transmissions, and constructing physical shields from specialized ferromagnetic materials like mu-metal is often prohibitively expensive and highly impractical.
Security professionals recommend implementing hardware-based signal jamming, which utilizes commercial magnetic field generators to actively produce counter-magnetic noise that completely drowns out the covert transmissions.
Alternatively, software-based jamming can be deployed to introduce random CPU workloads that disrupt the attacker’s encoded signal, though this defensive approach may temporarily degrade overall system performance.
Ultimately, strict physical zoning policies that completely ban external electronic devices from the immediate vicinity of air-gapped computers remain the most reliable defensive measure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.