Vidar Malware Steals Browser Credentials, Wallets &
Vidar malware, a long-active information stealer in circulation since late 2018, is once again making headlines. This Vidar was not built from scratch. It was developed using the source code of an...
Vidar malware, a long-active information stealer in circulation since late 2018, is once again making headlines. This
Vidar was not built from scratch. It was developed using the source code of an older stealer called Arkei and has grown into one of the more resilient commodity malware families tracked today.
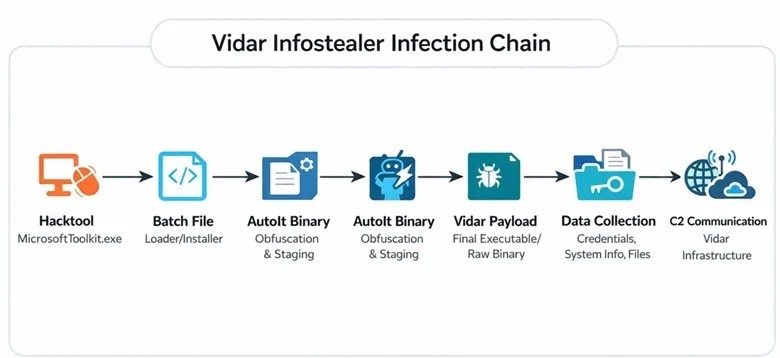
What makes recent activity particularly alarming is not just what Vidar steals, but how carefully attackers prepare before deploying it. Each step in the infection chain is designed to avoid detection before the actual payload runs.
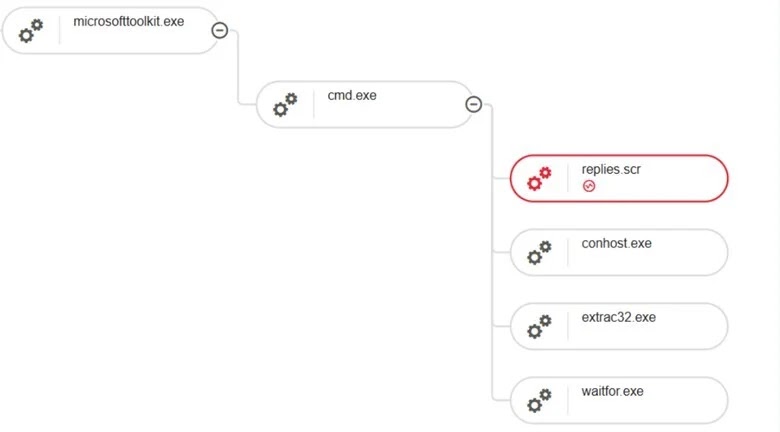
Researchers at LevelBlue, through proactive threat hunting in a client environment, uncovered this multi-stage loader campaign. Their endpoint telemetry and dynamic analysis revealed a chain of processes showing script masquerading, staged payload extraction, and command-and-control communication.
The discovery highlights how well-known malware families are being wrapped in increasingly clever delivery mechanisms to extend their reach. The attack begins with what looks, to an unsuspecting user, like a legitimate software activation tool.
How Vidar Steals Sensitive Data
A commonly abused hack tool called MicrosoftToolkit.exe serves as the entry point, tricking users into running it under the belief they are activating real software. This user-driven approach reduces the need for phishing emails or software exploits, making the initial entry harder for traditional security filters to catch.
Once the tool runs, a disguised file named Swingers.dot gets renamed as a batch script and executed, kicking off a chain of commands. The system checks for active security processes, extracts additional payload components, and eventually runs an AutoIt-compiled loader called Replies.scr. Outbound connections to Vidar-associated infrastructure then confirm the final payload has been deployed and is actively harvesting data.
Vidar focuses on pulling information that can be converted into financial gain or used to access other systems. Once the loader completes its work and the payload runs, the malware targets browser-stored credentials, saved session cookies, cryptocurrency wallet files, and general system data. Even a single infected machine can hand attackers a significant amount of usable information.

The malware uses public platforms like Steam and Telegram as part of its command-and-control setup, disguising its traffic as ordinary web activity. It constructs HTTP GET requests to pull configuration data from these platforms before moving forward with exfiltration.
Calls HttpOpenRequestA to construct an HTTP request (Source – LevelBlue)
DNS lookups were also observed pointing to gz.technicalprorj.xyz, resolved through a public DNS server, suggesting the attackers rely on dynamic infrastructure to stay ahead of blocklists.
Defense Evasion and Post-Attack Cleanup
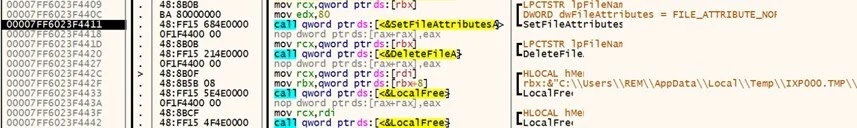
One of the most notable features of this campaign is how thoroughly the malware covers its tracks after running. Once payload extraction is complete and data has been sent, MicrosoftToolkit.exe deletes every file it dropped during execution, resets file attributes, frees associated memory, and terminates its own process. This leaves very little behind for investigators, making traditional incident response far more difficult.
The malware also checks for debuggers and security monitoring tools before proceeding, using low-level Windows functions to detect analysis environments. If it senses observation, it can alter its behavior accordingly.
This anti-analysis capability, combined with the cleanup routine and use of legitimate Windows tools throughout the chain, gives this campaign a moderate-to-high level of sophistication despite relying on a commodity stealer at its core.

LevelBlue recommends that any affected systems be isolated immediately from the network to stop further data loss. Full system reimaging is strongly advised given the malware’s ability to download additional payloads.
All exposed credentials, including browser passwords, email accounts, VPN logins, and admin accounts, should be reset and active sessions closed. Enforcing multi-factor authentication across critical services is equally important. Organizations should also monitor outbound traffic and DNS queries for unusual connections, and restrict execution of unauthorized tools to prevent similar intrusions.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA256 | fc27479ff929d846e7c5c5d147479c81e483a2ec911bd1501a53aa646a29620d | MicrosoftToolkit.exe |
| SHA256 | d4fe9f48178cdf375a3be30d17f1dc016b5861dff8683f0bb35a0ba8d44f892f | swingers.dot.bat |
| SHA256 | 978ad86c90d85b74947bb627ec24f8bcd26812b500e82f5af202160506ac29c6 | Beds.dot |
| SHA256 | 881619a47b62b52305d92640cc4d4845a279c23a5a749413785fc8fcb0fdf7fb | replies.scr |
| SHA256 | 968ecf51c442ec0ff91f91689ac524e7e8e9eab0c1a2a65cf13e54cf95194efe | D (payload file) |
| IP Address | 149.154.167.99 | Vidar-associated C2 IP |
| Domain | telegram[.]me | C2 domain |
| Domain | gz[.]technicalprorj[.]xyz | Vidar-associated C2 domain |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.