UAT-7290 Hackers Attacking Critical Infrastructure Entities in
Threat group UAT-7290 has been actively
Threat group UAT-7290 has been actively Critical Infrastructure Entities across South Asia since at least 2022.
This advanced threat actor operates with clear signs of Chinese government connections and poses a serious risk to vital communication networks in the region.
The group’s recent expansion into Southeastern Europe shows their growing reach and ambition.
Cisco Talos analysts and researchers identified that UAT-7290 employs a calculated approach to break into targeted systems. The group starts with careful planning and technical reconnaissance to understand their targets before launching attacks.
They use a mix of different attack methods, including exploiting known security weaknesses and using brute force attacks on systems that face the internet.
The group also functions as an initial access provider, meaning they compromise systems that other hacking groups can later use for their own operations.
UAT-7290’s toolkit includes sophisticated malware designed to work on Linux systems, which powers many edge networking devices.
The malware families tracked by Cisco Talos include RushDrop, a dropper that starts the infection process; DriveSwitch, which helps execute the main malicious software; and SilentRaid, the central program that maintains ongoing access.
These tools show the group’s technical sophistication and their focus on gaining deep control over compromised networks.
Infection process
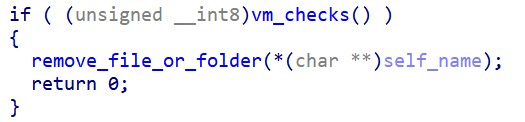
The infection process reveals the group’s technical expertise. When RushDrop runs on a system, it first checks whether it is operating on a real computer or a test environment to avoid detection.
If the checks pass, RushDrop creates a hidden folder named “.pkgdb” and unpacks three components into this location.
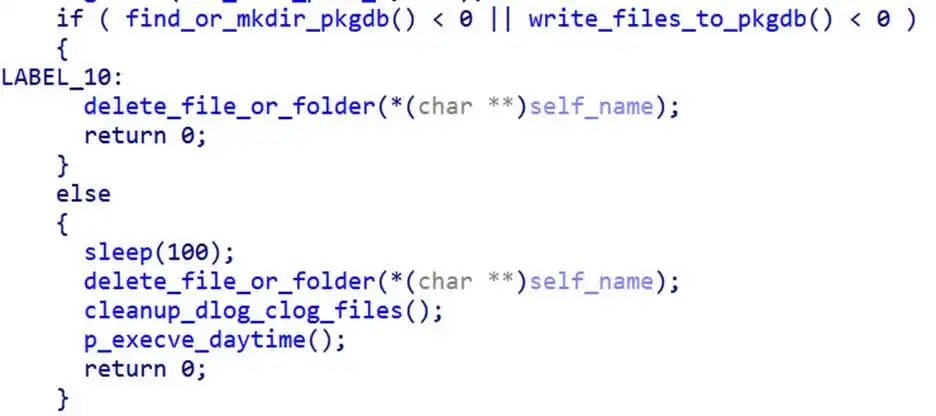
The process includes extracting “chargen,” which is the SilentRaid implant, along with “busybox,” a legitimate Linux tool that can execute commands on the system.
This step-by-step approach shows how the attackers hide their tools and maintain control without raising immediate suspicion.
SilentRaid operates using a modular plugin system that gives attackers multiple capabilities. The malware can open remote shells, forward internet ports, and manage files on infected systems.
When SilentRaid starts, it communicates with its control server using a domain name and Google’s public DNS service (8.8.8.8) to find the server’s address.
This communication method helps the malware hide its activities within normal-looking internet traffic, making detection harder for network defenders.
The plugin system allows the attackers to mix and match different tools during compilation, giving them flexibility to customize their attacks for each target.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.