Fragnesia Linux Vulnerability Let Attackers Gain Root Privileges
A recently disclosed Linux kernel vulnerability, dubbed Fragnesia, enables any local unprivileged user to escalate privileges to root. Crucially, this exploit does not require a race condition,...
A recently disclosed Linux kernel vulnerability, dubbed Fragnesia, enables any local unprivileged user to escalate privileges to root. Crucially, this exploit does not require a race condition, making it one of the more reliable local privilege escalation exploits identified in recent years.
Discovered by William Bowling of the V12 security team, Fragnesia joins a growing class of dangerous kernel bugs that silently rewrite the rules of Linux security.
Fragnesia belongs to the Dirty Frag vulnerability class, a cousin of the infamous Dirty Pipe and Copy Fail bugs, but targets a separate logic flaw in the Linux XFRM ESP-in-TCP subsystem.
The name itself hints at the mechanism: the kernel “forgets” that a fragment is shared during socket buffer coalescing, corrupting memory it was never supposed to touch.
Fragnesia Works Linux Kernel Vulnerability
The exploit weaponizes a subtle logic bug in how the kernel handles ESP-in-TCP ULP (Upper Layer Protocol) mode.
When a TCP socket transitions to espintcp ULP after file data has already been spliced into the receive queue, the kernel mistakenly processes those queued file pages as ESP ciphertext.
This causes a single AES-GCM keystream byte to be XORed directly into a read-only file’s kernel page cache no race condition needed.
By carefully selecting an IV nonce to produce any desired keystream byte, an attacker can flip any byte in a cached file to any value, one byte per trigger invocation.
The exploit constructs a 256-entry lookup table mapping all possible keystream bytes to their corresponding nonces, then iterates over a malicious payload, overwriting the first 192 bytes of /usr/bin/su in the page cache with a small ELF stub that calls setresuid(0,0,0) and executes /bin/sh.
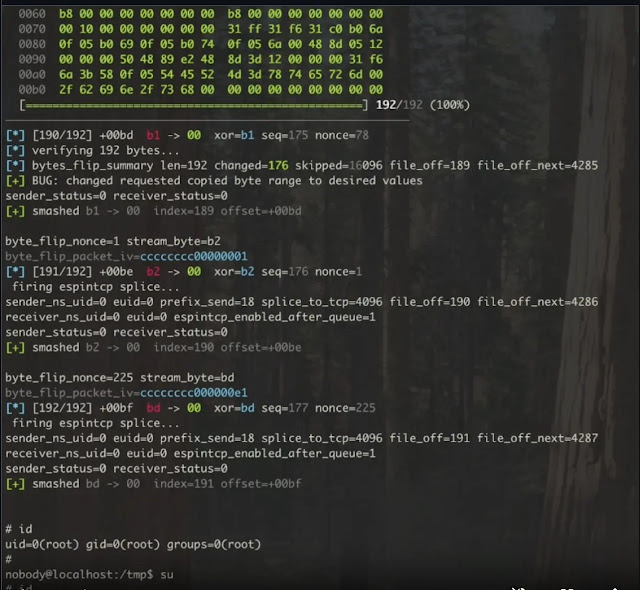
Crucially, the on-disk binary remains completely untouched; only the in-memory page cache is modified.
Affected Versions and Mitigation
Every Linux kernel version affected by Dirtyfrag, effectively any kernel before May 13, 2026, is vulnerable. The patch has been submitted upstream, but unpatched systems remain exposed.
Until patching is possible, administrators should immediately unload the affected ESP modules:
textrmmod esp4 esp6 rxrpc
printf 'install esp4 /bin/falseninstall esp6 /bin/falseninstall rxrpc /bin/falsen' > /etc/modprobe.d/dirtyfrag.conf
A critical post-exploitation warning: once the exploit runs, /usr/bin/su in the page cache remains modified and will re-spawn a root shell on every invocation until the cache is flushed. Administrators must run echo 1 | tee /proc/sys/vm/drop_caches or reboot before leaving any affected machine unattended.
A public proof-of-concept is already available on GitHub, lowering the barrier to exploitation significantly.
Organizations running Linux servers should treat this as a critical priority and apply the upstream patch immediately.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.