Foxconn Confirms Cyberattack by Nitrogen Ransomware Gang
Foxconn has confirmed a cyberattack against its North American operations. This acknowledgment followed the Nitrogen ransomware gang’s public listing of the company on their data leak site,...
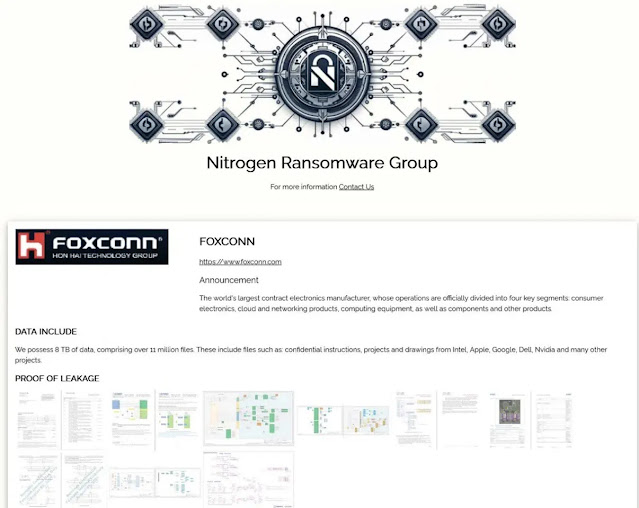
Foxconn has confirmed a cyberattack against its North American operations. This acknowledgment followed the Nitrogen ransomware gang’s public listing of the company on their data leak site, where they claimed to have stolen 8 terabytes of sensitive data.
The Nitrogen ransomware group made its move on Monday, posting Foxconn on its breach and extortion portal and asserting it had exfiltrated more than 11 million files from the company’s systems. The following day, Foxconn acknowledged the breach.
“Some of Foxconn’s factories in North America suffered a cyberattack,” a company spokesperson confirmed to The Register. “The cybersecurity team immediately activated the response mechanism and implemented multiple operational measures to ensure the continuity of production and delivery.”
Reports indicate the affected facilities include Foxconn’s plant in Mount Pleasant, Wisconsin, as well as a factory in Houston, Texas, with some staff temporarily forced to use pen and paper or stay home during the disruption.
The Nitrogen gang claims the stolen data includes confidential instructions, internal project documentation, and technical drawings tied to projects at Intel, Apple, Google, Dell, and Nvidia.
Analysis of publicly released sample files revealed financial documents connected to the Houston facility, along with circuit board layouts, temperature sensor data, and integrated circuit documentation.
Critically, sample files also contained network topology maps for AMD, Intel, and Google projects, a detail that alarmed security analysts.
“The real concern is that Google and Intel’s network topologies have been stolen. Because this is an architectural map of operational infrastructure, attackers could use this data to identify vulnerabilities in data centers around the world,” security analyst Mark Henderson warned.
Despite Nitrogen’s claims that Apple project files were among the stolen data, AppleInsider reported that the available sample files do not appear to contain Apple circuit diagrams, product development documents, or quality control data, noting that Foxconn’s Mount Pleasant facility primarily manufactures televisions and data servers, not Apple devices.
Nitrogen is a ransomware operation that has been active since 2023 and is believed to be built on leaked source code from the Conti 2 builder.
The group is suspected of having links to the infamous ALPHV/BlackCat ransomware ecosystem and operates a double-extortion model — encrypting victim data while simultaneously threatening to publish it publicly.
Foxconn stated that affected factories are currently resuming normal production, though the company declined to confirm whether any customer data was actually stolen. The incident marks at least the third time Foxconn has faced a major ransomware attack, underscoring persistent security vulnerabilities within global electronics supply chains.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.