Google Boosts Android Mobile Security with New AI Protections
Globally, billions rely on Android smartphones. These devices handle everything from banking and messaging to sensitive documents and personal photos. This ubiquitous use makes mobile devices prime...
Globally, billions rely on Android smartphones. These devices handle everything from banking and messaging to sensitive documents and personal photos. This ubiquitous use makes mobile devices prime targets for scammers, cybercriminals, and other threat actors. These adversaries constantly evolve their tactics, often bypassing existing defenses, as detailed in Google’s recent The threat landscape facing Android users has grown more complex with each passing year. Attackers now use spoofed caller IDs, fake banking apps, and malicious software disguised as legitimate tools to steal money and personal data.
These threats do not just affect tech-savvy users but target everyday people, exploiting trust in familiar institutions like banks and financial services. Phone-based scams and fraud cause an estimated hundreds of billions of dollars in annual losses worldwide.
Researchers and security experts at Google’s Android Security and Privacy Team, led by Director Eugene Liderman, have been closely monitoring how these attack methods are changing. They noted that bad actors increasingly use internet-based calling systems to spoof caller IDs, a tactic known as “spoofing,” which makes a fraudulent call appear to come from a trusted bank or institution. This social engineering tactic is behind a growing wave of financial fraud across multiple countries.
Google has now responded with a comprehensive set of new AI-powered security features built directly into Android. These updates span everything from real-time call monitoring to stronger device protection when a phone is lost or stolen. The company says its focus heading into the rest of 2026 is on making these intelligent defenses even more seamless and powerful for every user.
The upgrades represent a meaningful shift in how Android approaches mobile security, moving away from reactive fixes and toward proactive, always-on protection that runs quietly in the background. Whether guarding against a spoofed bank call or detecting a suspicious app, the new features are designed to act before harm is done.
AI-Powered Threat Detection
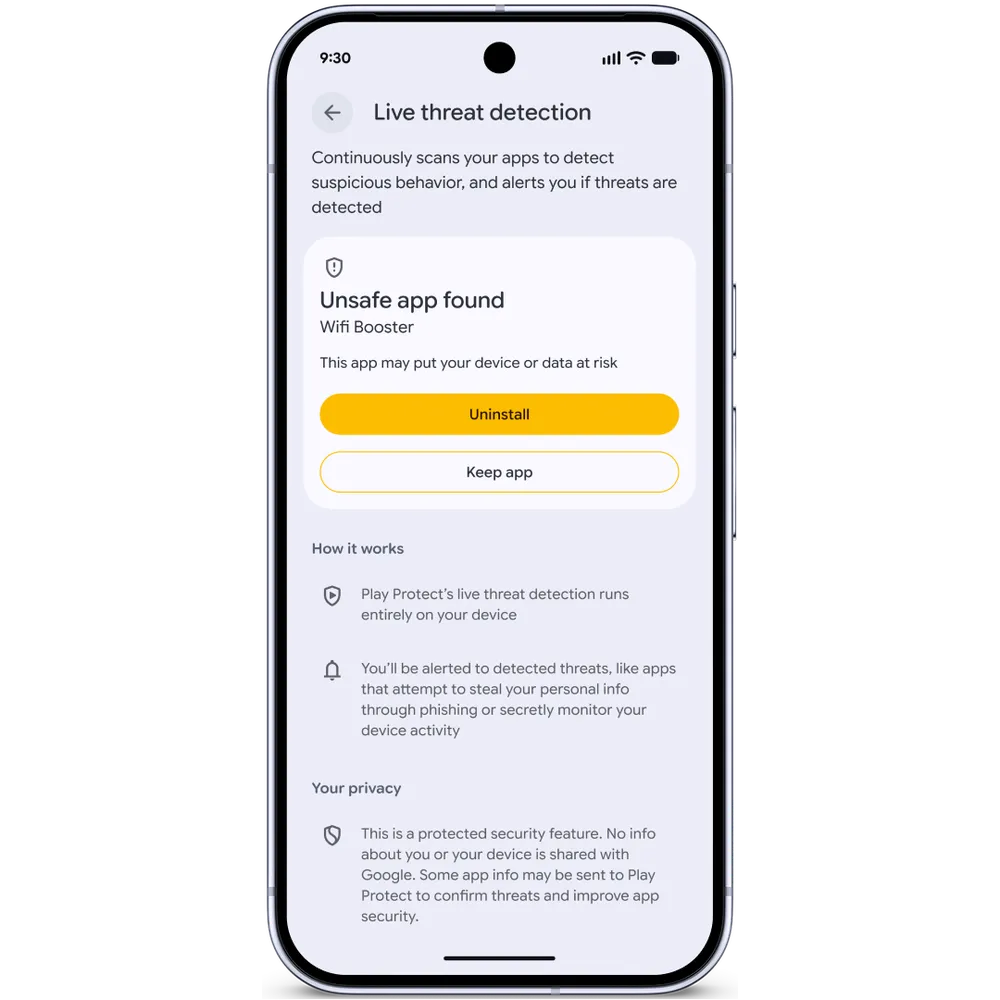
One of the most notable new features is an enhanced version of Live Threat Detection, which uses on-device artificial intelligence to analyze app behavior and alert users if an app starts acting suspiciously. Google is expanding this system to catch more apps that attempt to scam or harm users by monitoring for known suspicious patterns in real time.
New warnings now cover behaviors like SMS forwarding, where an app quietly routes messages to another number, and accessibility overlay abuse, where an app uses permissions to display deceptive content on screen.
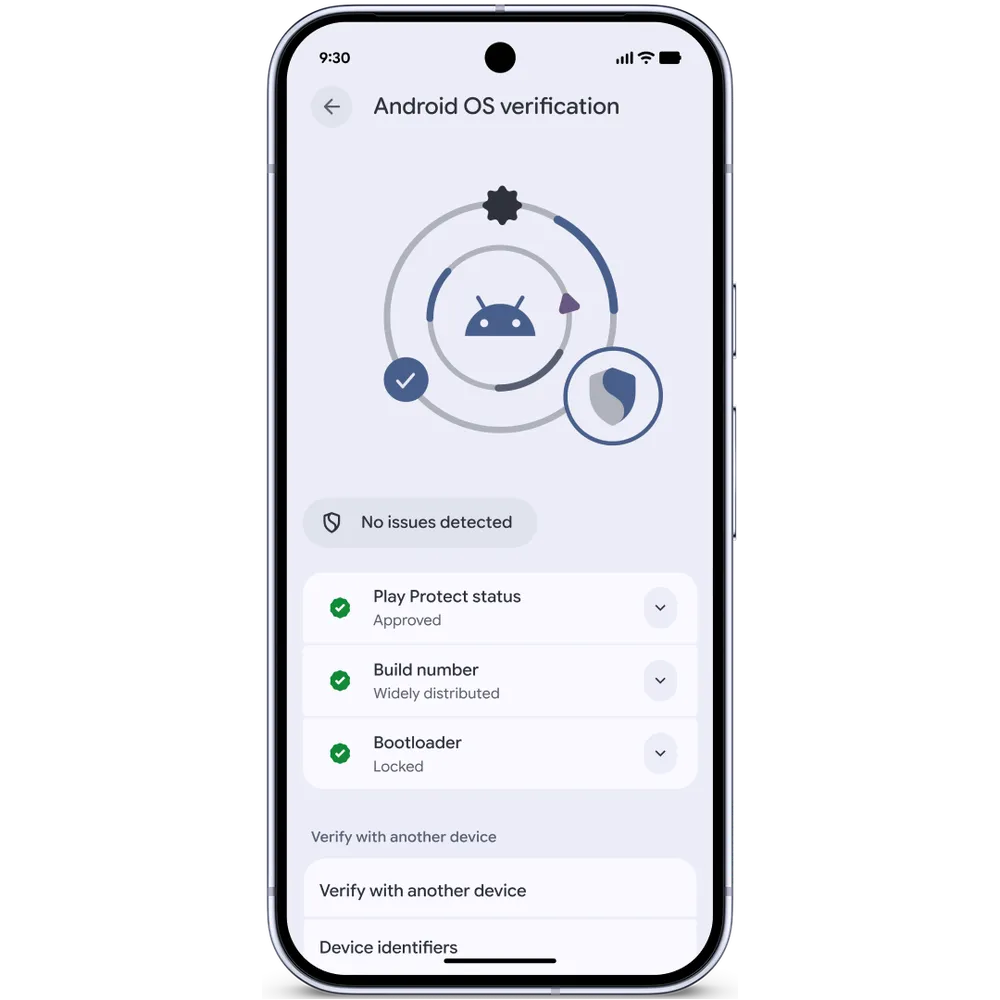
Dynamic signal monitoring is also being introduced on Android 6 devices, tracking how apps interact with the operating system to catch abusive behaviors early. For Chrome on Android, a new layer of protection checks an app’s package identifier against a malware database before a download completes, stopping users from unknowingly installing harmful apps.
Stronger Device and Privacy Controls
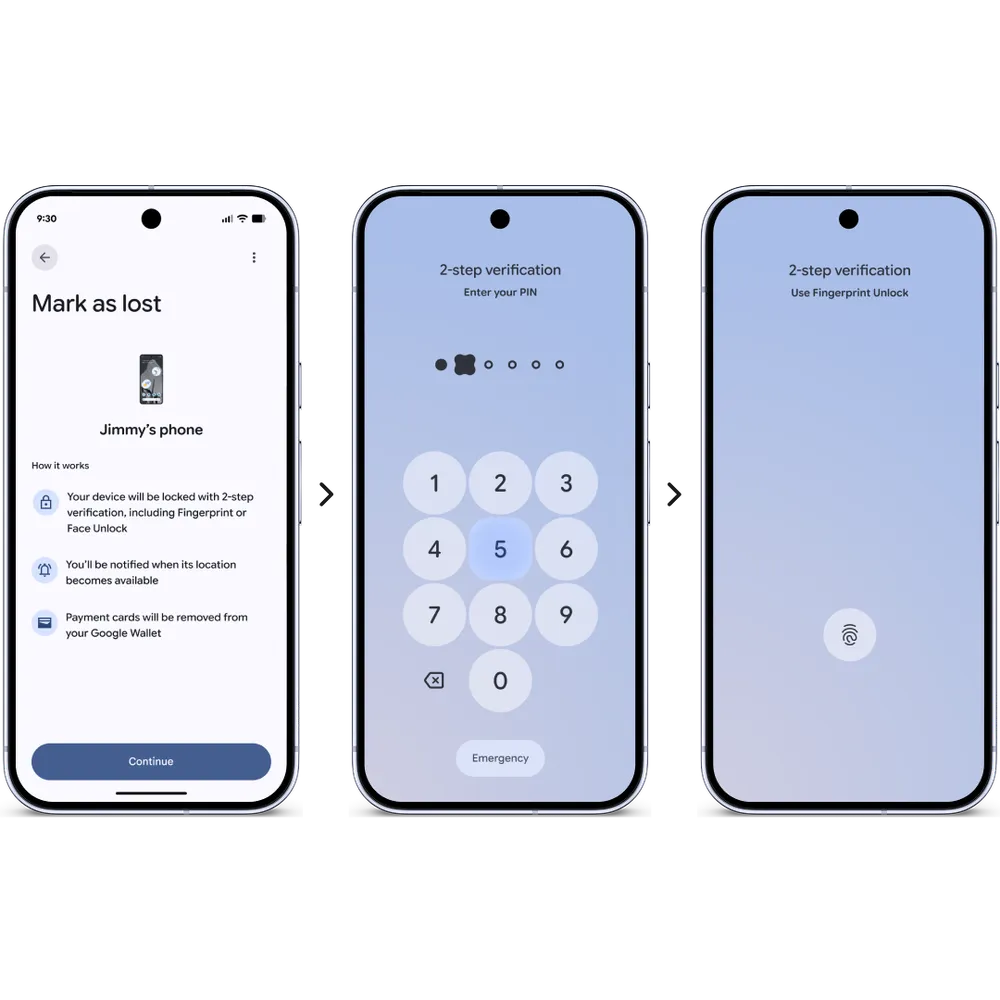
Google is also strengthening protections for situations when a device falls into the wrong hands. The Find Hub’s “Mark as Lost” feature is being upgraded in Android 16, now requiring biometric authentication to unlock a device that has been reported lost. A thief who knows someone’s PIN or password still cannot unlock the phone once the owner marks it as lost, closing a loophole attackers have exploited.
To give users more control over their location data, Android 16 is introducing a location button that allows sharing precise location temporarily while a specific app is open. This eliminates the need to grant permanent location permissions just to complete a quick task, like finding a nearby place. A new location indicator will also appear at the top of the screen whenever an app is accessing location data, similar to the existing camera and microphone indicators.
Android is also tightening protections around one-time passwords. Scammers sometimes use malicious apps granted the SMS permission to read and steal OTPs from text messages. Android now automatically hides these sensitive security codes for three hours from most apps, ensuring OTPs stay protected from unauthorized access while they are still active.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.