New Phishing Attack: DocuSign Impersonation De Impersonate Deploys
A new phishing wave is abusing fake DocuSign notifications to drop stealthy malware on Windows systems. The emails copy real DocuSign branding and urge users to review a pending agreement, pushing...
A new phishing wave is abusing fake DocuSign notifications to drop stealthy malware on Windows systems.
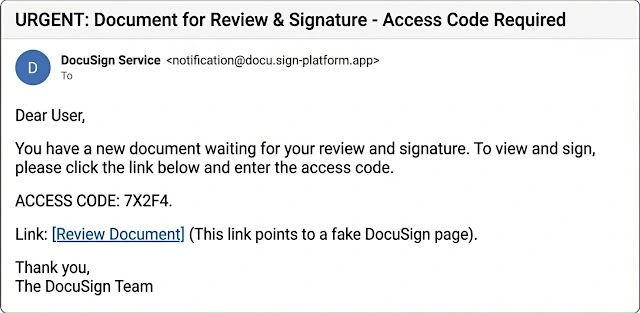
The emails copy real DocuSign branding and urge users to review a pending agreement, pushing them toward a link that claims to host the file.
Once clicked, the chain shifts from browser to a multi‑stage loader built to dodge basic email and endpoint defenses.
The phishing link leads to a web page that asks the victim for an access code before showing the supposed document.
This gate boosts trust and also blocks many automated sandboxes, which do not know the correct code.
Behind the page, a script selects the next stage, often a download that looks like a harmless PDF or zipped contract.
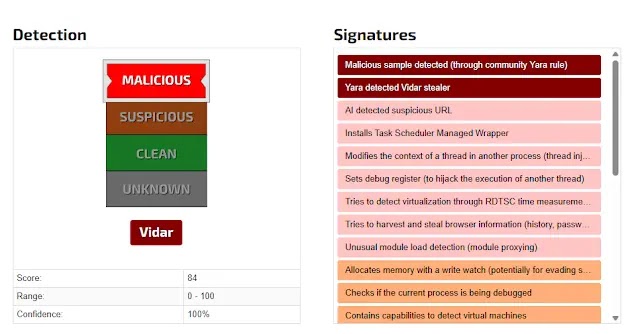
JOEsecurity analysts/researchers noted and later identified the malware while running samples in Joe Sandbox Cloud Basic, where the access‑code gate, time‑based checks, and extra packing became visible.
Their complete technical breakdown shows how the loader waits for certain time windows and then decrypts its real payload only in memory.
This presents the process tree and network calls that expose this behavior. While the targets range from small firms to large global enterprises.
Infection Mechanism and Stealth Tactics
Once the victim opens the downloaded lure, a small script or macro launches a PowerShell command that pulls the next stage from a remote server under attacker control.
The command uses long, obfuscated strings, environment variables, and encoded blocks to hide its intent from simple rules.
A common pattern seen in this campaign, where PowerShell is started with an encoded payload and a hidden window.
powershell -EncodedCommand $enc -WindowStyle Hidden -ExecutionPolicy BypassAfter decoding, the script loads a .NET component directly into memory, starts it as a child of a trusted process such as explorer.exe, and injects the main payload into that host.
The malware then sets light persistence by adding a Run key in the registry or a scheduled task that calls the script with a fresh access code.
Because most work happens in memory and inside trusted hosts, strong endpoint logs and network monitoring are vital to spot this DocuSign themed attack.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.