Sandworm SSH-over-Tor Tunnel for Hidden Persistence
The state-sponsored threat group Sandworm, also tracked as APT-C-13 and FROZENBARENTS, has launched a targeted cyberattack campaign. This campaign employs a combined SSH and Tor tunneling technique...
The state-sponsored threat group Sandworm, also tracked as APT-C-13 and FROZENBARENTS, has launched a targeted cyberattack campaign. This campaign employs a combined SSH and Tor tunneling technique to maintain long-term, hidden access inside victim networks.
This campaign marks a clear upgrade from the group’s earlier intrusion tactics, shifting from simple malware callbacks toward a fully anonymous, encrypted remote control system capable of operating quietly behind enterprise firewalls.
The group has been active since at least 2014, primarily targeting government agencies, diplomatic departments, energy companies, and research organizations to steal political, military, and technological intelligence.
In this latest campaign, the attackers refined their methods by deploying dual-layer anonymous tunnels designed to blend into normal network traffic.
The infection begins with a spear-phishing email carrying a ZIP archive that, once opened, silently installs malicious tools while showing a legitimate-looking decoy document to keep the victim unaware.
Researchers at 360 Advanced Threat Research Institute identified multiple malicious samples tied to this campaign, noting that the group used SSH and Tor nested tunneling to build a double-encrypted anonymous channel between the attacker and the compromised host.
This architecture gave attackers unrestricted access to victim systems, allowing them to extract sensitive data without triggering standard traffic inspection tools or raising alerts from network monitoring systems.
The attack samples were delivered inside a ZIP archive named Iskhod_7582_Predstavlenie_na_naznachenie.zip with an MD5 hash of 2156c270ffe8e4b23b67efed191b9737.
Inside this archive, the group hid a malicious LNK shortcut disguised as a PDF document alongside a fake folder called $RECYCLE.BIN set to mimic the Windows Recycle Bin directory.
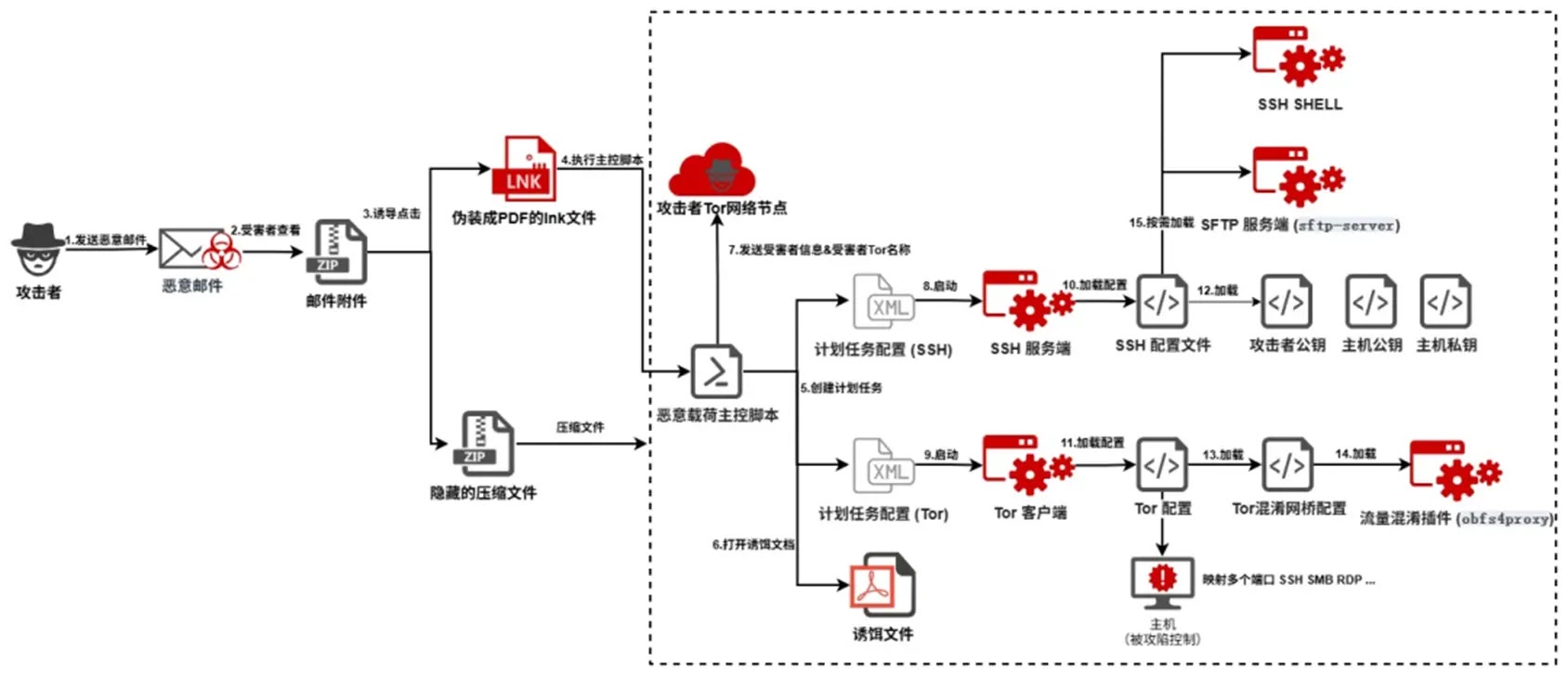
Once the victim clicked the LNK file, the full attack toolkit deployed silently in the background while the real decoy PDF opened to keep the user distracted from the installation.
The overall impact of this attack is severe. Once the toolkit was in place, attackers gained persistent control over the victim’s internal network, with the ability to move laterally, access sensitive files, and operate the remote desktop.
Critical local ports, including SMB port 445 and RDP port 3389, were mapped to a dark web Onion address, allowing the attacker to connect from anywhere in the world through the Tor network, bypassing all inbound firewall protections.
How Sandworm Achieved Persistent Hidden Access
The most technically notable part of this campaign is how Sandworm embedded long-term access inside victim systems using tools disguised as well-known applications.
After the LNK file triggered the main control script currentSessionTrigger, the script first verified whether it was running on a real machine by checking for at least 10 recent .lnk files and 50 or more active processes.
If the environment passed these checks, the script registered two scheduled tasks named OperagxRepairTask and DropboxRepairTask, both hidden from the default Task Scheduler view, ensuring malicious payloads launched automatically at every user login.
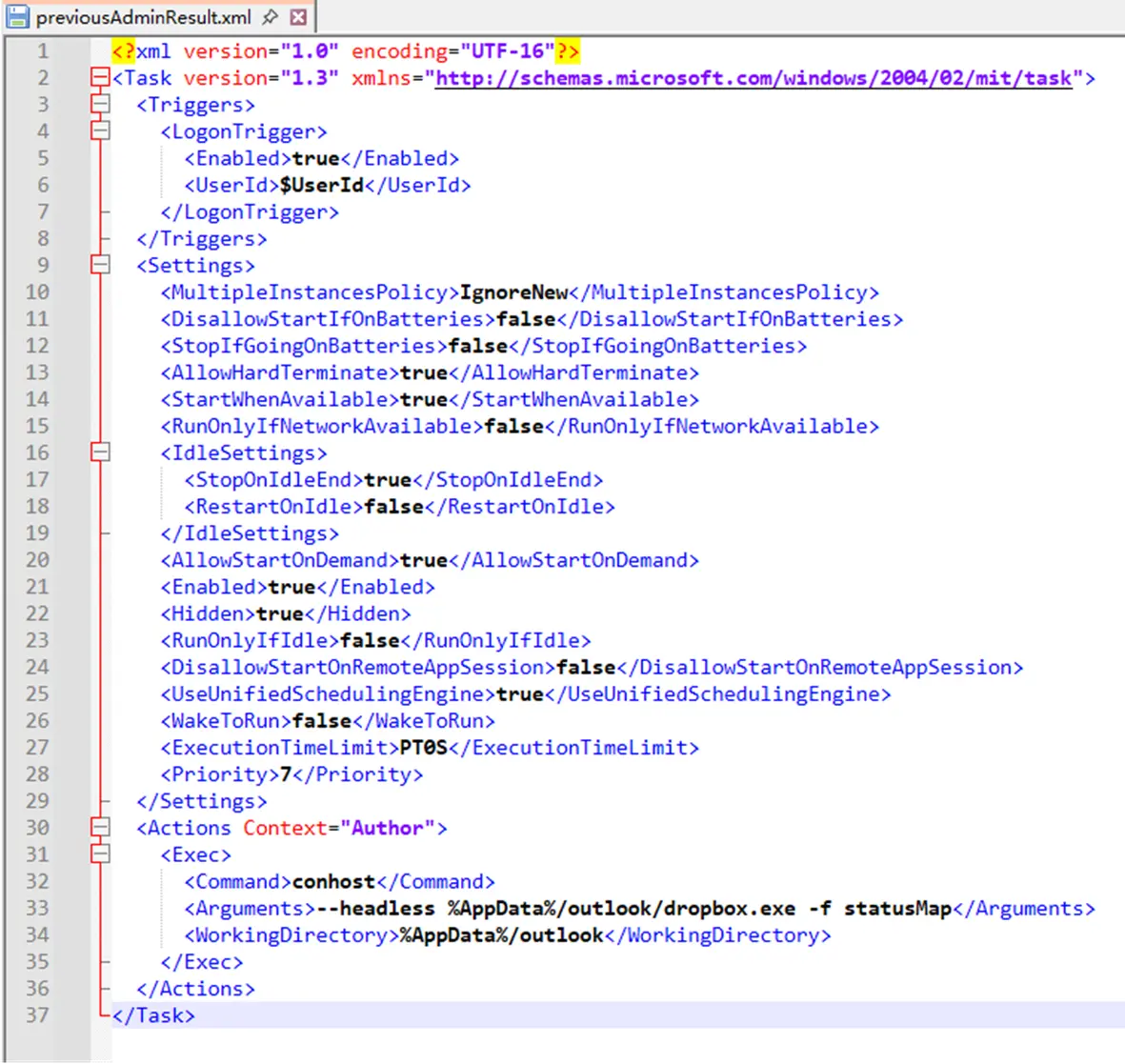
These tasks launched two disguised executables: operagx.exe, which was actually an OpenSSH daemon, and dropbox.exe, which was a Tor server.
A third file, safari.exe, acted as an obfs4 traffic obfuscation plugin, reshaping all Tor traffic into random TCP streams to bypass enterprise firewalls and deep packet inspection systems.
A fourth file, obsstudio.exe, served as an SFTP server for silent file transfers. The SSH daemon was configured to listen only on local loopback port 20321, keeping it invisible to external network scans.
Once the Tor service started, it generated a hidden .onion hostname. The main control script read this hostname and sent the victim’s identity details to a hardcoded C2 address at kvk46su7d2qi6g4n43syp4zbsf2rihnc6ztj77qtc2ojvewjqvqilnqd.onion using curl with high-frequency retry settings to maintain the connection, completing a permanent encrypted shadow control channel inside the victim’s network.
Organizations should regularly audit scheduled tasks for entries impersonating trusted applications like browsers or cloud storage programs.
Security teams should configure firewalls to detect and block Tor-related and obfs4 traffic at the perimeter.
Employees need ongoing training to avoid opening ZIP attachments from unknown senders, especially files with LNK shortcuts disguised as documents.
Deploying endpoint detection tools that identify SSH server processes running from AppData directories with non-standard port configurations is strongly recommended.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.