New Spyware Platform: Rebrand & Resell Android Lets Buyers
A new Android spyware platform is now being openly sold online. While its inherent surveillance features are concerning, the true danger lies in an additional capability that significantly amplifies...
A new Android spyware platform is now being openly sold online. While its inherent surveillance features are concerning, the true danger lies in an additional capability that significantly amplifies its potential for abuse.
For a fee, anyone can buy it, put their own name and logo on it, and start selling it as their own product.
This is not just a malware story. It is a warning about how the spyware business model is evolving in ways that make it harder for law enforcement to shut down.
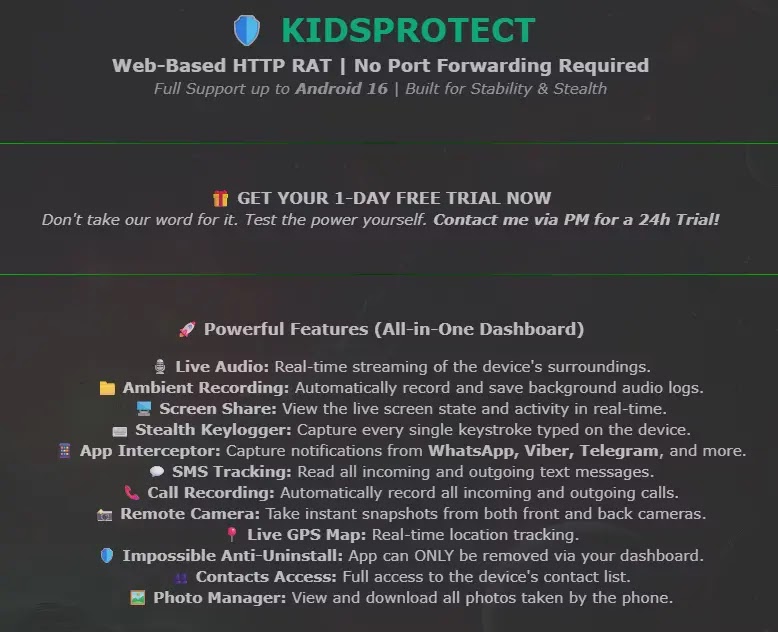
The tool is called KidsProtect. It presents itself as a parental monitoring app, but its true purpose has nothing to do with child safety.
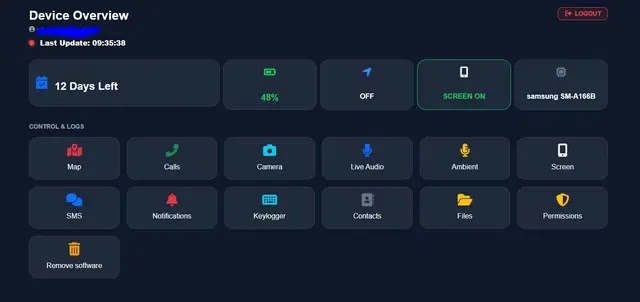
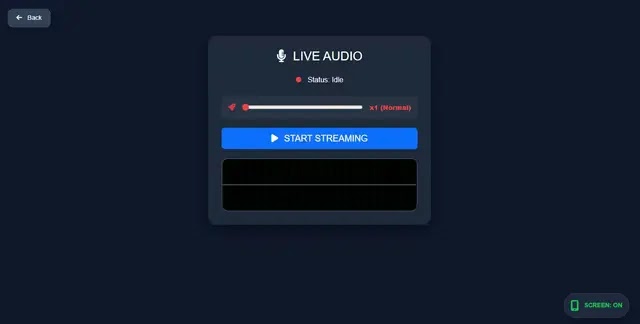
Once installed on a target device, it runs completely in the background, giving the operator full control over the victim’s phone without the victim ever knowing.
It works on Android 7 and above, claims support for Android 16, and is sold on a subscription basis starting at $60.
A separate white-label package lets buyers rebrand it entirely and resell it under their own company name and pricing structure.
Certo analysts identified KidsProtect being advertised openly on a clear-web hacking forum, an unusual place for a tool that claims to protect children.
The listing made little effort to hide the tool’s real purpose, advertising it as “Built for Stability and Stealth” and offering a one-day free trial to potential buyers.
The developer, based on forum profile details and in-app screenshots, appears to be Greek-speaking.
The white-label reseller model means that even if one operator is taken down by law enforcement, dozens of new operators can relaunch the same technology under fresh branding within hours.

This directly undermines past enforcement actions. In 2024, a New York court ordered the shutdown of PhoneSpector and Highster Mobile, two well-known stalkerware platforms. The KidsProtect reseller model is designed specifically to make such victories far less meaningful over time.
Hiding in Plain Sight: How KidsProtect Evades Detection
Perhaps the most deliberate aspect of KidsProtect is how hard it works to remain invisible on a device. Once installed, it does not appear under its real name.
Instead, it shows up as “WiFi Service” or “WiFiService Installer,” a generic label that most users would overlook without a second thought.
Its accessibility service is labeled “WiFiService Assistant” and its notification listener is called “WiFiService Monitor,” keeping every visible component looking like a harmless system process.
The app’s package name, com.example.parentguard, raises immediate red flags for anyone with software development knowledge.
The “com.example” prefix is a placeholder used in beginner coding tutorials and almost never appears in real commercial software sold to paying customers.
Its use here strongly suggests a deliberate choice to avoid leaving a traceable identity within the app itself.
Certo researchers obtained and analyzed the APK file, confirming the app requests an extensive list of Android permissions including ACCESS_BACKGROUND_LOCATION, RECORD_AUDIO, CAMERA, READ_SMS, READ_CALL_LOG, and READ_CONTACTS, among many others.
The app also abuses Android’s Accessibility Service permission, which grants it the ability to read any content shown on the screen and intercept passwords as they are typed, giving the attacker full visibility across the entire device.
The app requests SYSTEM_ALERT_WINDOW and REQUEST_IGNORE_BATTERY_OPTIMIZATIONS permissions, which prevent Android from shutting it down to save battery.
A BootReceiver component restarts it automatically on every device reboot. To block removal, it registers as a Device Administrator through MyDeviceAdminReceiver, making it impossible to uninstall through normal phone settings.
Its download page instructs users to disable Google Play Protect before installing, a signal the app would be flagged as malware if Android’s built-in scanner were active.
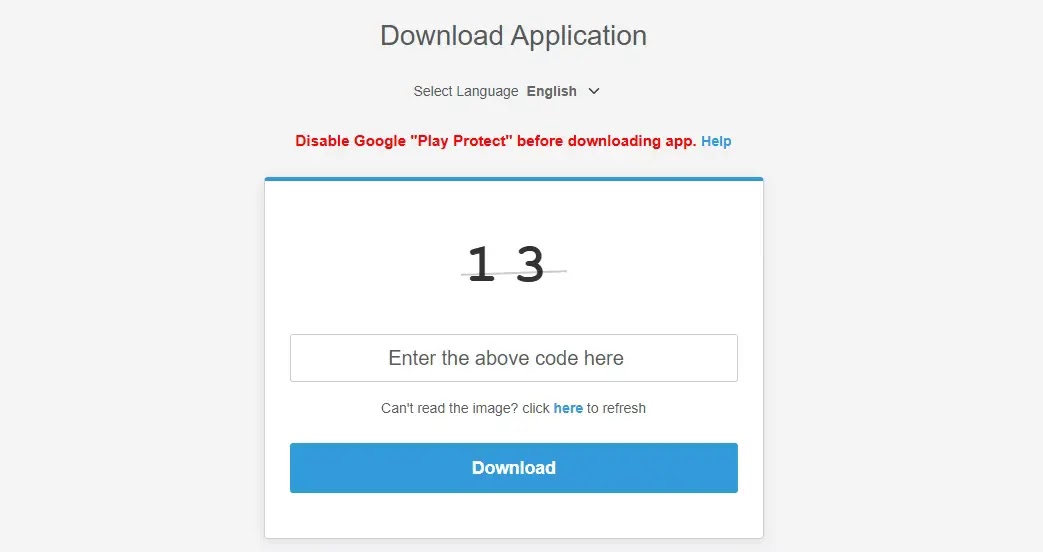
Users are strongly advised to keep Google Play Protect enabled at all times and never install APK files from sources outside the official Google Play Store.
Any app requesting Accessibility Service access should be carefully reviewed before granting permission. Checking the Device Administrator list in Android security settings can help identify unauthorized entries.
If the package name com.example.parentguard is detected on any device, it should be treated as a confirmed infection and reported immediately.
Indicators of Compromise:-
Package Name: com.example.parentguard
SHA-256 Hashes:–
- 9864db6b5800d9e03b747c46fdef988e035cadde83077a41c5610d5d89f753a0
- 1b1d9b260deec0c612ec67579fd36fec7722b2b8446ab32284a08f44f4ea64da
- f4e9733d93ce35ecd3c83f18addf77f8ff49444d09847eaeef9c8e87837d0165
- 17817d9e29920493bb20ed626c3026e3c29eb6f1d56ef9462c306066ce2ad171
- f0d01b28ddfdbefe0697994a6b30f2b8a4e39ef1ad6c9427b921b2ccd945a8c5
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.