CrashFix: Hackers Use Malicious Extensions for Fake
Cybersecurity researchers have recently uncovered a sophisticated malware campaign that employs an unusual, yet remarkably effective, tactic: intentionally crashing users’ web browsers. The threat,...
Cybersecurity researchers have recently uncovered a sophisticated malware campaign that employs an unusual, yet remarkably effective, tactic: intentionally crashing users’ web browsers.
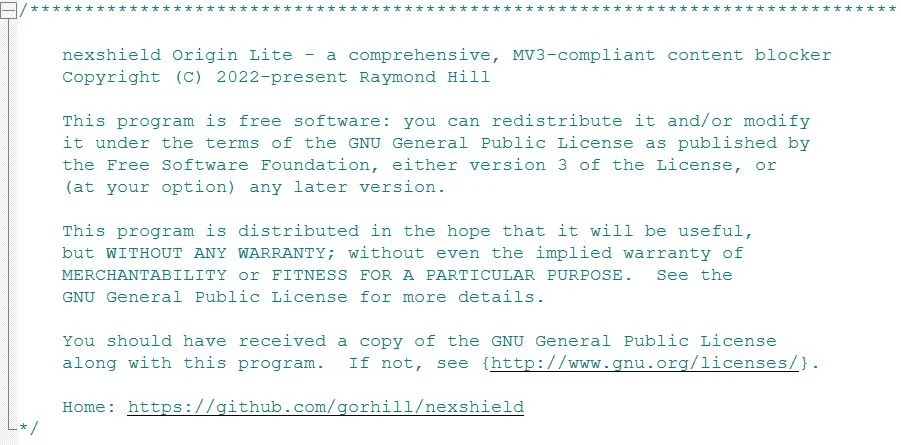
The threat, named CrashFix, operates through a malicious Chrome extension disguised as the legitimate ad blocker NexShield.
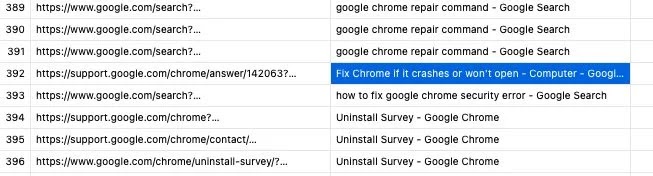
When users search for privacy tools online, malicious advertisements direct them to download what appears to be a trustworthy extension from Google’s Chrome Web Store.
The fake extension launches a coordinated attack designed to frustrate users into executing dangerous commands.
The campaign reveals a multi-layered infection approach targeting both home and corporate networks. Upon installation, the extension remains dormant for the first hour before activating its destructive payload.
This timing strategy creates distance between installation and problems, making it harder for victims to blame their browser troubles on recently added software.
The operation demonstrates careful planning by threat actors who understand user behavior.
Huntress analysts noted that the campaign originates from KongTuke, a tracked threat actor group active since early 2025.
Researchers identified multiple sophisticated components including the NexShield extension mimicking uBlock Origin Lite, the CrashFix attack mechanism, and a previously unknown Python-based remote access tool called ModeloRAT.

Corporate targets receive preferential treatment, with domain-joined machines accessing more powerful malware compared to standalone systems, suggesting attackers prioritize enterprise compromises.
The Browser Denial-of-Service Attack Mechanism
CrashFix’s core relies on a deliberate denial-of-service attack against the victim’s browser. The extension contains code creating one billion runtime port connections in an infinite loop.
Each port consumes memory while the array expands without bound, overwhelming the browser’s internal messaging system and consuming CPU cycles.
Memory usage climbs until system limits are reached, causing severe slowdown, frozen tabs, and complete browser crashes requiring force-quit.
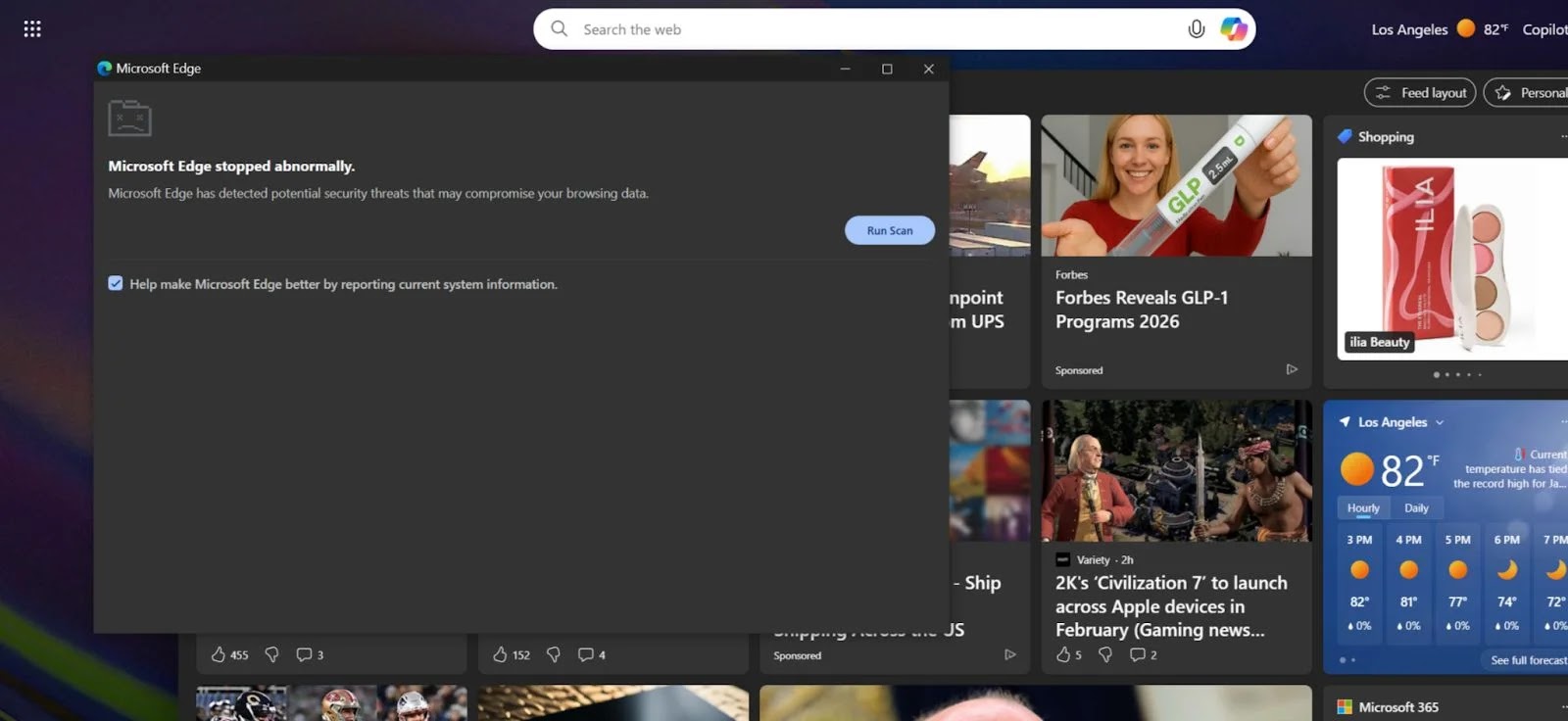
When users restart their browser, they encounter a fake security warning claiming the browser “stopped abnormally.” The warning instructs victims to open Windows Run dialog, paste a clipboard command, and press Enter.
Unknown to users, the malicious extension previously copied a PowerShell command to their clipboard. The displayed command appears legitimate but executes a dangerous payload instead.
Attackers intentionally trigger the attack only after establishing C2 connectivity and confirming user interaction with the popup, demonstrating operational awareness.
This combines social engineering with technical exploitation for devastating results.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.