QLNX Credential Theft Targets Developers for Supply Chain Comprom
A novel and previously undocumented Linux threat, dubbed QLNX, has emerged, specifically targeting software developers and posing a direct risk to global supply chains. This credential theft malware,...
A novel and previously undocumented Linux threat, dubbed QLNX, has emerged, specifically targeting software developers and posing a direct risk to global supply chains. This credential theft malware, detailed in a
The attack begins long before any obvious sign of infection. QLNX executes entirely in memory, copies itself to a RAM-backed file, and then deletes its own binary from disk, leaving no trace on the hard drive.
The malware disguises its process using names that mimic normal Linux kernel threads, such as [kworker/0:0] or [migration/0], so even a careful administrator would not notice anything unusual.
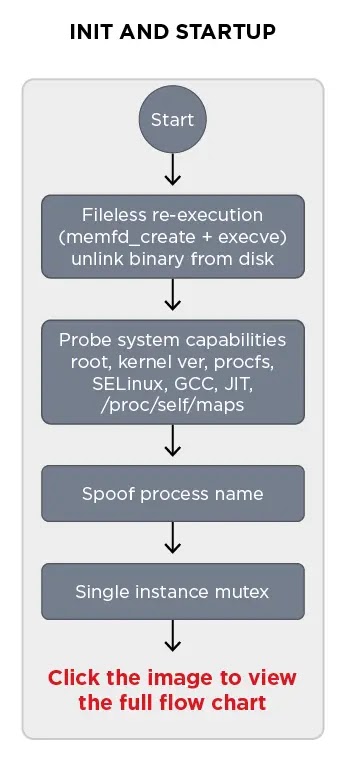
Researchers from Trend Micro identified and analyzed QLNX after their AI-driven threat hunting platform flagged an unusual Linux implant with notably low detection rates. The team found that the malware carries embedded source code for both its rootkit and PAM backdoor inside the binary itself.
It compiles these components at runtime using the system’s own GCC compiler, then loads them through /etc/ld.so.preload to intercept system-wide activity.
What makes QLNX particularly alarming is its scope. It runs a multi-stage credential harvesting routine that sweeps SSH private keys, browser login databases, cloud configuration files for AWS and Kubernetes, Docker credentials, Git tokens, NPM tokens, PyPI API keys, and any .env files it finds.
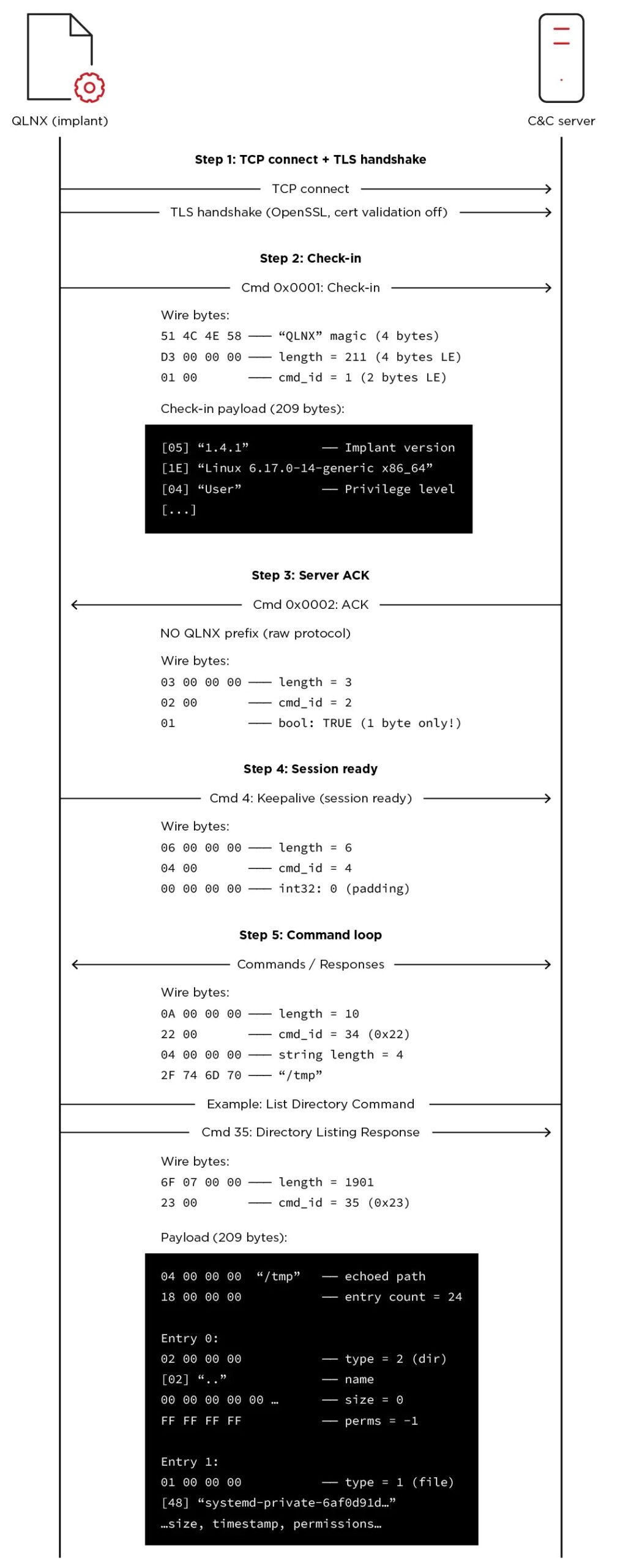
All stolen data is sent to the attacker’s command-and-control server over an encrypted connection.
The malware also includes peer-to-peer mesh networking, so each infected system can relay commands to other compromised hosts, making eradication harder.
Organizations are advised to monitor for process names mimicking kernel threads, inspect /etc/ld.so.preload for unexpected entries, audit developer endpoints for suspicious shared library files, and review cloud credential stores after any suspected infection.
QLNX Targets Developers for Supply Chain Access
The most alarming aspect of QLNX is not what it does to a single machine, but what it enables downstream.
Developers are high-value targets because their credentials unlock publishing pipelines for packages used by thousands of users.
By stealing NPM and PyPI authentication tokens, QLNX gives its operator the ability to push malicious packages into trusted registries without raising immediate red flags.
Supply chain attacks through open-source ecosystems like PyPI and npm have become one of the most effective methods available to threat actors today.
A single compromised maintainer account could be used to trojanize a legitimate package, inject backdoors into build artifacts, or pivot into cloud environments where production infrastructure lives. The damage from one infected developer machine can be enormous.
The malware harvests SSH keys to move laterally to other servers in the user’s known host chain. This means the initial compromise can quietly spread to cloud instances and CI/CD pipelines long before anyone detects a problem.
QLNX’s ability to wipe system logs including auth.log, syslog, and bash_history makes forensic investigation significantly harder after the fact.
Stealth, Persistence, and PAM Backdoor
QLNX goes to exceptional lengths to remain hidden and survive reboots. It registers persistence through systemd services, crontab reboot entries, init.d scripts, and modifications to the user’s .bashrc file. Even if one persistence method is removed, the others ensure the malware restarts automatically, making full eradication genuinely difficult.
The PAM backdoor is one of QLNX’s most technically sophisticated components. PAM, or Pluggable Authentication Module, handles logins on Linux systems. QLNX injects a malicious PAM module that intercepts credentials in plaintext the moment a user authenticates, then stores captured passwords in a hidden log file at /var/log/.ICE-unix using XOR-encrypted logging.
The eBPF-based kernel rootkit hides the malware’s process IDs, file names, and network ports at the kernel level, making standard tools like ps, top, or netstat ineffective.
The combination of in-memory execution, log wiping, and PAM interception creates a threat that is difficult to detect even on monitored systems. Organizations running Linux developer environments should treat this as an urgent concern and review their endpoint visibility practices immediately.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-256 | ea1d34b21b739a6bbf89b3f7e67978005cf7f3eda612cefc7eac1c8ead7c5545 | Quasar-implant binary |
| SHA-256 | 82DAA93219BA40A6E41CDF3174BA57EB5D3383D1CD805584E9954EB0200182A1 | libsecurity_utils.so.1 (LD_PRELOAD rootkit) |
| SHA-256 | 42D0C420EB5FE181388F2E4F0B7D7C0D302971E7A06FDC1BEC481B68C8CCAE1F | pam_security.so (PAM backdoor) |
| SHA-256 | C99CF0DC1EF1057D713CB082ACAF42E4DF4656809C91741752BDDCAB39BBFACA | hide_src_39ZoR.cb |
| SHA-256 | CEA89CAAB82181881D971BE312412795051F6322B105C8B9D29CFB5729FAB8D33 | pam_src_51yC3.f |
| SHA-256 | F417430b2d4ae8d005224a9ff5dcb4007d452338acbcbcbb62c4e8ed1a70552dd | libpam_cache.so |
| SHA-256 | d55549d5655e2f202e215676f4bdb0994ea08a93d15ec4ded413f64cfa7facc8 | pcs_3kf9x.c |
| MD5 | 570f707430f28a7ab836d1c659333152ab9a | quasar-implant (MD5) |
| SHA-1 | b0f2c668cbdd63a87c1c090c95b2c6f9c3e9c3111158752e | quasar-implant (SHA-1) |
| File Path | /usr/lib/libsecurity_utils.so.1 | LD_PRELOAD rootkit shared object |
| File Path | /usr/lib/.libpam_cache.so | PAM credential hook shared object |
| File Path | /etc/ld.so.preload | Modified to load rootkit and PAM hook |
| File Path | /tmp/.pam_cache | Plaintext credential log |
| File Path | /var/log/.Test-unix | Hidden log for captured SSH passwords |
| File Path | /var/log/.ICE-unix | Hidden log for captured PAM passwords |
| File Path | /tmp/.X752e2ca1-lock | Single-instance mutex lock file |
| File Path | ~/.config/systemd/user/quasar_linux.service | Systemd user service persistence file |
| File Path | ~/.config/autostart/quasar_linux.desktop | XDG autostart persistence file |
| File Path | /etc/systemd/system/quasar_linux.service | Systemd system service persistence file |
| File Path | /etc/init.d/quasar_linux | init.d script persistence file |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.