Researchers Accessed Hacker Server Through Name Server Delegation
Recent findings from an investigation into a deceptive push-notification network reveal how a fundamental DNS misconfiguration can expose underlying criminal infrastructure. The campaign abused...
Recent findings from an investigation into a deceptive push-notification network reveal how a fundamental DNS misconfiguration can expose underlying criminal infrastructure.
The campaign abused browser notifications to flood Android users with fake security alerts, gambling lures, and adult offers. Random-looking domains and hidden hosting tried to hide the operator while keeping the flow of clicks and ad money moving.
Trouble surfaced when one domain stopped resolving, even though notifications kept arriving. Instead of live landing pages, victims saw browser errors.
What looked like a routine outage was in fact a misconfigured name server setup, leaving the domain in a lame delegation state that no longer pointed to a valid backend.
Infoblox researchers identified this weakness and realized the threat actor had let DNS control slip while devices worldwide still called home.
By legitimately claiming the same domain at the DNS provider, the team redirected traffic to infrastructure they managed, without touching victim devices or the attacker’s servers.
From that point, every push message and tracking request sent by the hacker’s network also reached the researchers’ server, creating a live view into the operation.
Over the following days, thousands of infected browsers connected from across the globe. Each request carried rich JSON logs about the device, language, lure text, and click behavior.
In total, the team captured tens of millions of records, revealing aggressive use of brand impersonation and scare tactics to chase clicks.
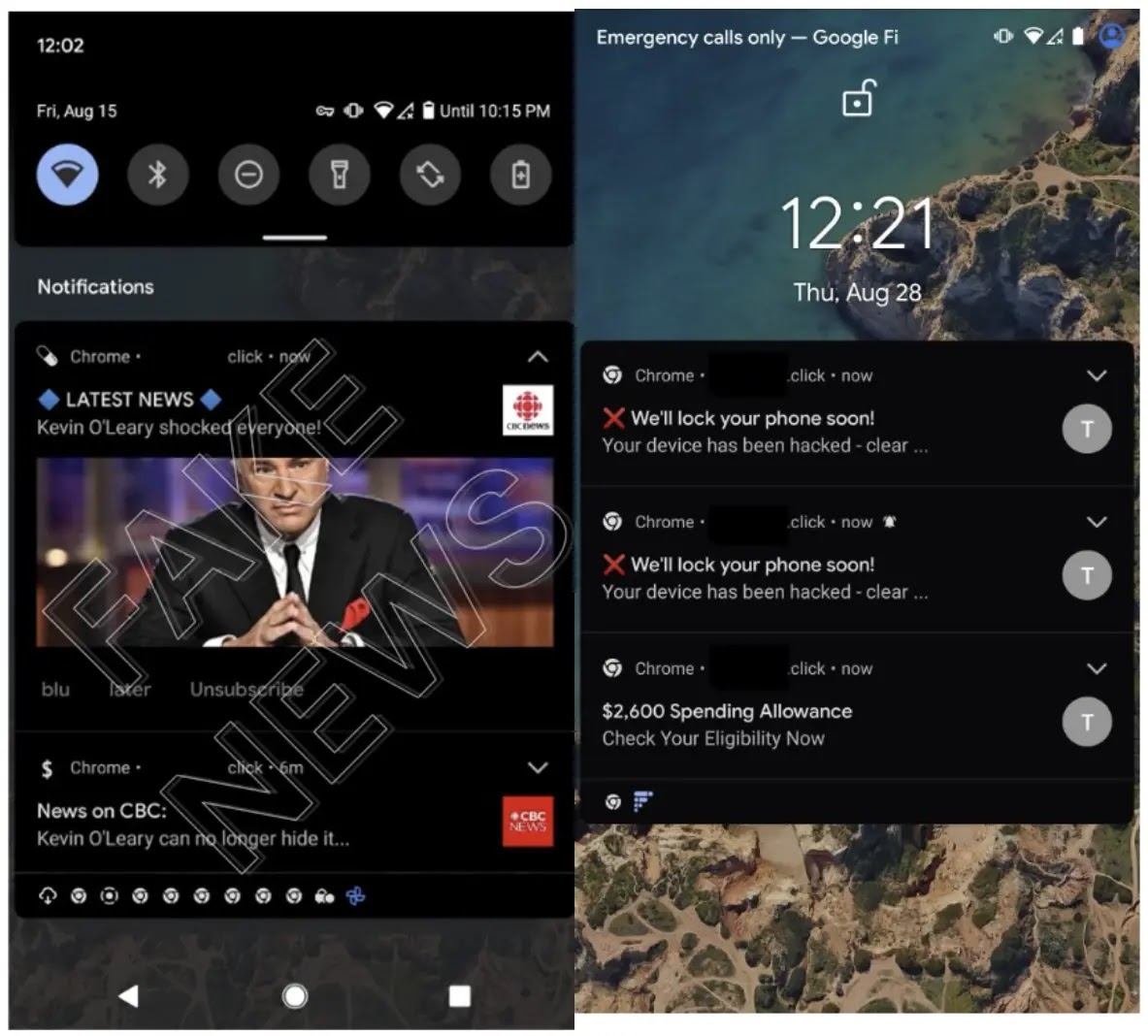
Logs showed that a typical user might receive more than one hundred notifications per day, often for months.
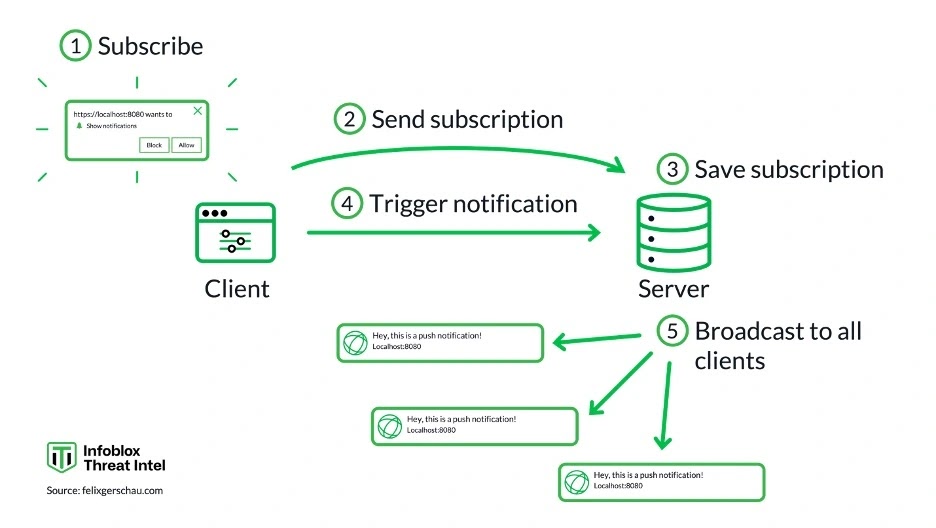
Infection Mechanism: From One Click to Ongoing Control
The infection path began with a visit to a compromised or shady site. Users were shown a browser pop-up asking them to allow notifications, mixed in with cookie banners and captcha prompts.
Once permission was granted, the site installed a custom service worker in the browser, acting like a background agent that kept the subscription active.
That service worker regularly checked in with the attacker’s push server, fetched updated scripts, and pulled scam or ad templates. If the user closed the tab, the worker stayed active and continued to trigger notifications.
In this way, the attackers gained persistent reach without classic malware files, relying instead on web standards and weak DNS hygiene.
When lame name server delegation exposed their abandoned domain, defenders used the same plumbing to watch rather than spread the campaigns.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.