PDFSIDER Malware Bypasses Antivirus & EDR Actively Used
A new backdoor, dubbed PDFSIDER, has been uncovered, granting attackers long-term control over Windows systems. Notably, this malware actively bypasses many antivirus and endpoint detection and...
A new backdoor, dubbed PDFSIDER, has been uncovered, granting attackers long-term control over Windows systems. Notably, this malware actively bypasses many antivirus and endpoint detection and response (EDR) tools, presenting a significant challenge to conventional security measures.
It uses trusted software and strong encryption to hide its presence, letting intruders run commands, study the network, and move deeper inside targeted environments.
The campaign behind PDFSIDER relies on focused spear phishing. Victims receive emails that deliver a ZIP archive holding a legitimate PDF24 Creator executable, signed with a valid certificate, along with other companion files.
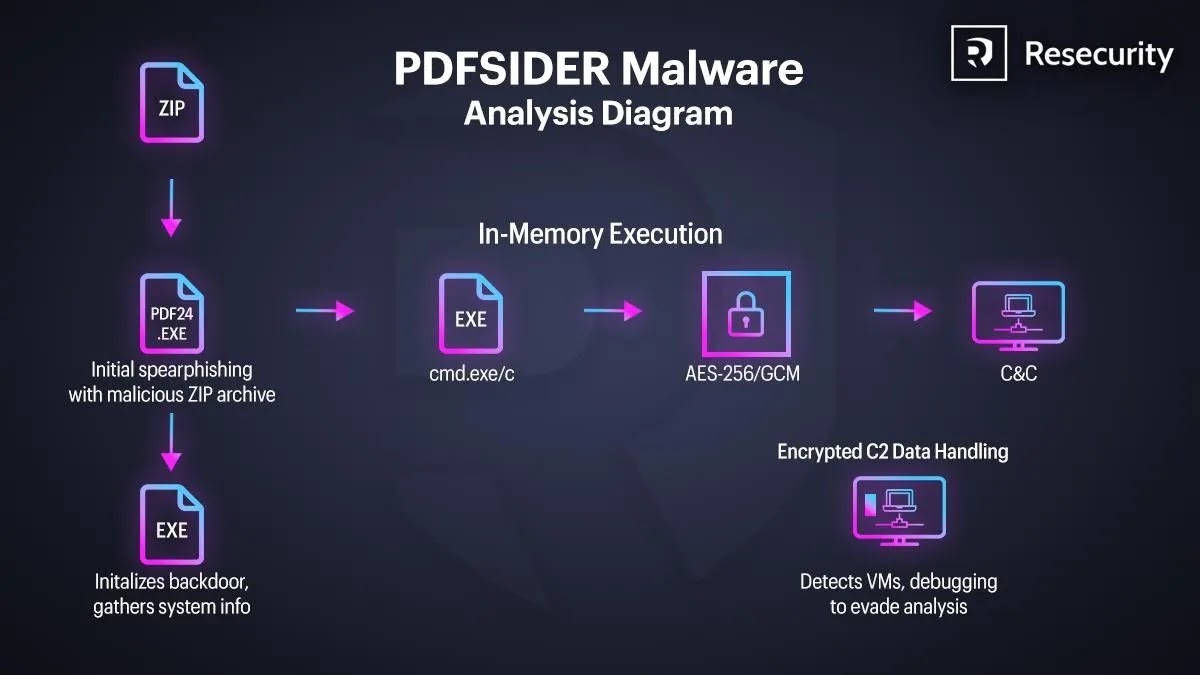
When the user launches the trusted app, a hidden payload is triggered instead of any obvious document viewer, starting the breach with almost no visible signs.
Resecurity analysts identified PDFSIDER during an attempted intrusion against a Fortune 100 enterprise that was stopped before data loss occurred.
Their investigation showed that the malware is already being used by multiple ransomware groups and advanced actors as a reliable payload loader that can slip around standard security controls.
The tool’s design more closely matches espionage tradecraft than smash and grab crime.
Impact on defenders
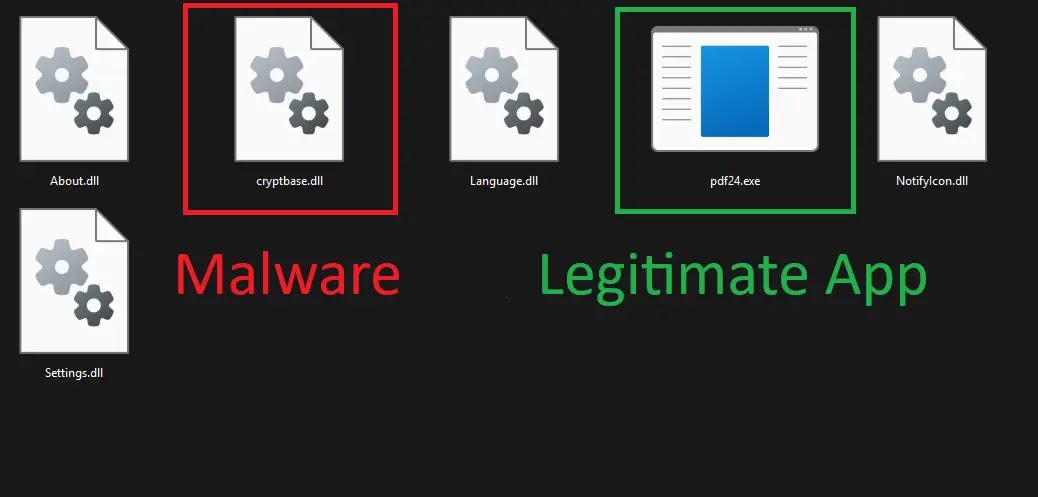
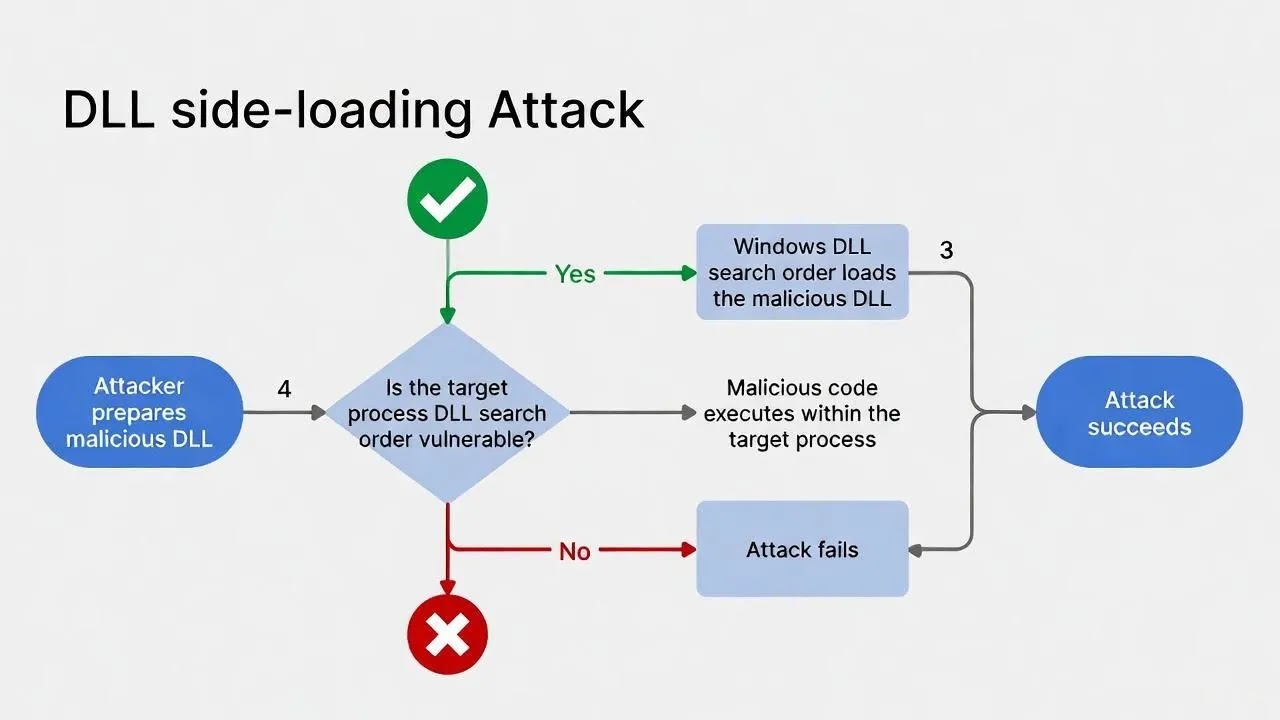
The impact on defenders is serious because PDFSIDER blends a valid application, a fake Windows cryptbase.dll, and encrypted command and control traffic over DNS port 53.
By operating mainly in memory, checking for virtual machines and debuggers, and avoiding noisy exploit chains, it makes traditional signature based detection and sandbox testing far less effective.
The infection flow begins when the victim runs the trojanized PDF24 executable from the delivered archive. In the same folder, the attackers place a malicious cryptbase.dll that abuses DLL side loading rules, so the program loads their library instead of the real system file.
Once loaded, PDFSIDER initializes Winsock, gathers system details, builds a unique host identifier, and sets up an in memory backdoor loop.
Next, the malware creates anonymous pipes and launches a hidden cmd.exe process using the CREATE_NO_WINDOW flag.
Any commands sent by the operators are executed without a console window, and the output is captured and sent back over an AES 256 GCM encrypted channel powered by the Botan library.
Because all traffic is strongly protected and never written to disk, security tools see only normal looking DNS requests while attackers enjoy full remote shell control.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.