Windows Defender 0-Day Exploit Gives Attackers Full
A zero-day local privilege escalation (LPE) exploit for Windows, named “BlueHammer,” has been publicly released. Security researcher Chaotic Eclipse (@ChaoticEclipse0) made available full...
A zero-day local privilege escalation (LPE) exploit for Windows, named “BlueHammer,” has been publicly released. Security researcher Chaotic Eclipse (@ChaoticEclipse0) made available full proof-of-concept (PoC) source code for the exploit on GitHub.
The disclosure was confirmed by vulnerability researcher Will Dormann, who noted that the exploit works and that Microsoft’s own security response process may have directly caused this uncoordinated release.
BlueHammer is a Windows zero-day LPE exploit that allows a low-privileged local user to escalate their access to NT AUTHORITYSYSTEM the highest privilege level on a Windows machine.
A screenshot shared alongside the disclosure dramatically demonstrates the impact: a command prompt launched from C:UserslimitedDownloads> — clearly a restricted user account — achieves a full SYSTEM shell within seconds, with whoami confirming nt authoritysystem.
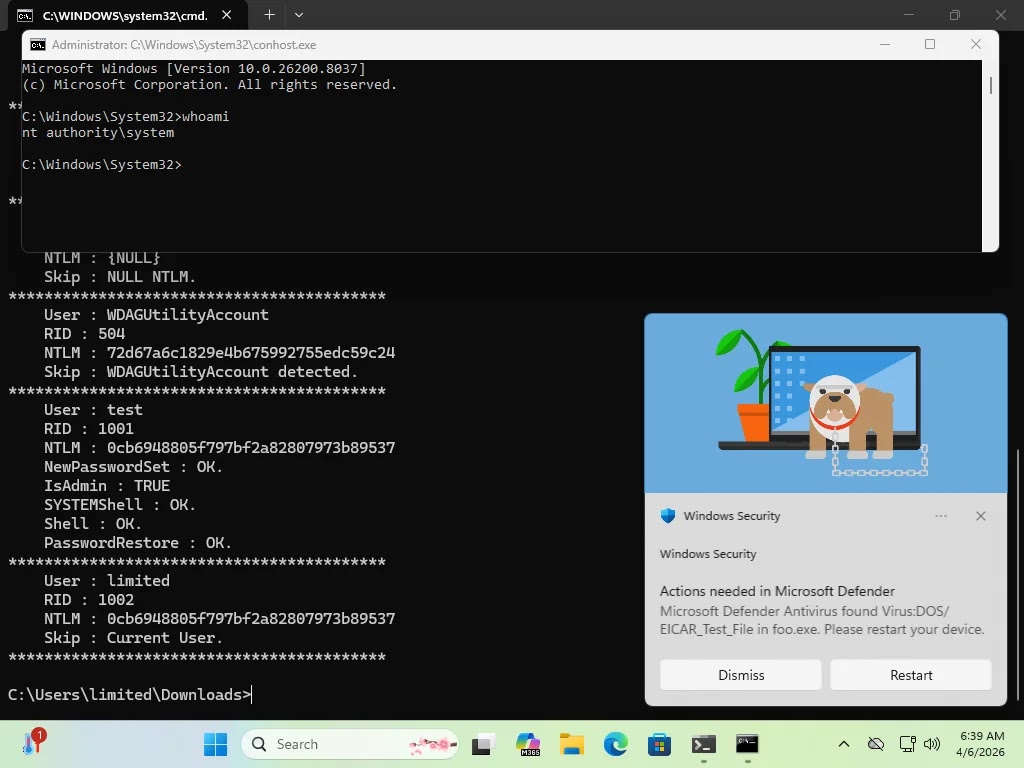
The exploit output also reveals credential-harvesting capabilities, displaying NTLM password hashes for local accounts, including an administrative user with IsAdmin: TRUE, and confirmations of SYSTEMShell: OK, Shell: OK, and PasswordRestore: OK.
The compromised system is running Windows 11 (Build 10.0.26200.8037), indicating the vulnerability affects modern, fully updated Windows installations.
The researcher cited frustration with Microsoft’s Security Response Center (MSRC) as the primary motivation behind the uncoordinated public disclosure.
According to Chaotic Eclipse, MSRC’s quality has significantly deteriorated in recent years, attributing the decline to Microsoft laying off experienced security personnel and replacing them with staff who follow rigid procedural flowcharts rather than exercising informed judgment.
A particularly pointed detail in the disclosure: MSRC reportedly required the researcher to submit a video demonstration of the exploit as part of the vulnerability reporting process, a requirement that many in the security community have found unusual and demanding.
The researcher suggests this demand may have been a deliberate friction point that ultimately led to the case being closed or stalled without resolution.
This type of disclosure, sometimes called a full drop or uncoordinated disclosure, is increasingly common when researchers feel their reports are being dismissed or mishandled by vendors. It places immediate pressure on the vendor to act, but also puts users at risk before a fix is available.
Chaotic Eclipse noted that the exploit does not work with 100% reliability, but acknowledged it functions “well enough” to be operationally useful. In the hands of a skilled threat actor, even a partially reliable LPE exploit can be refined and weaponized.
Ransomware groups and APT actors frequently integrate publicly released PoC code into their toolkits within days of disclosure.
Mitigations
Until Microsoft issues an official patch or mitigation advisory, security teams should take the following precautionary steps:
- Monitor endpoint detection and response (EDR) tools for unusual privilege escalation activity
- Restrict local user permissions to the minimum required for operations
- Apply enhanced logging on Windows systems to detect anomalous SYSTEM-level process spawning
- Watch for a Microsoft Security Update or advisory addressing the BlueHammer vulnerability
Microsoft has not yet issued a public statement or CVE assignment for this vulnerability at the time of publication.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.