Hackers Use Fake Reddit Posts to Deliver Vidar & TradingView Premium
A threat actor is actively exploiting Reddit, deploying fake posts that lure users with promises of free TradingView Premium access. This campaign delivers two distinct malware families: Vidar,...
A threat actor is actively exploiting Reddit, deploying fake posts that lure users with promises of free TradingView Premium access. This campaign delivers two distinct malware families: Vidar, targeting Windows systems, and AMOS, designed for macOS. The operation remains live; as older posts are removed, new ones quickly emerge to continue distributing these information stealers, as detailed in a recent report
TradingView is one of the most widely used charting platforms among retail traders, crypto investors, and forex enthusiasts. Its Premium subscription unlocks advanced indicators and real-time market data at a price many users would rather skip.
The threat actor exploits that gap by posting across multiple subreddits — some hijacked, others purpose-built — with step-by-step instructions that walk victims through the full infection chain without raising suspicion.
Hexastrike analysts traced these infections back to Reddit while handling several recent stealer cases.
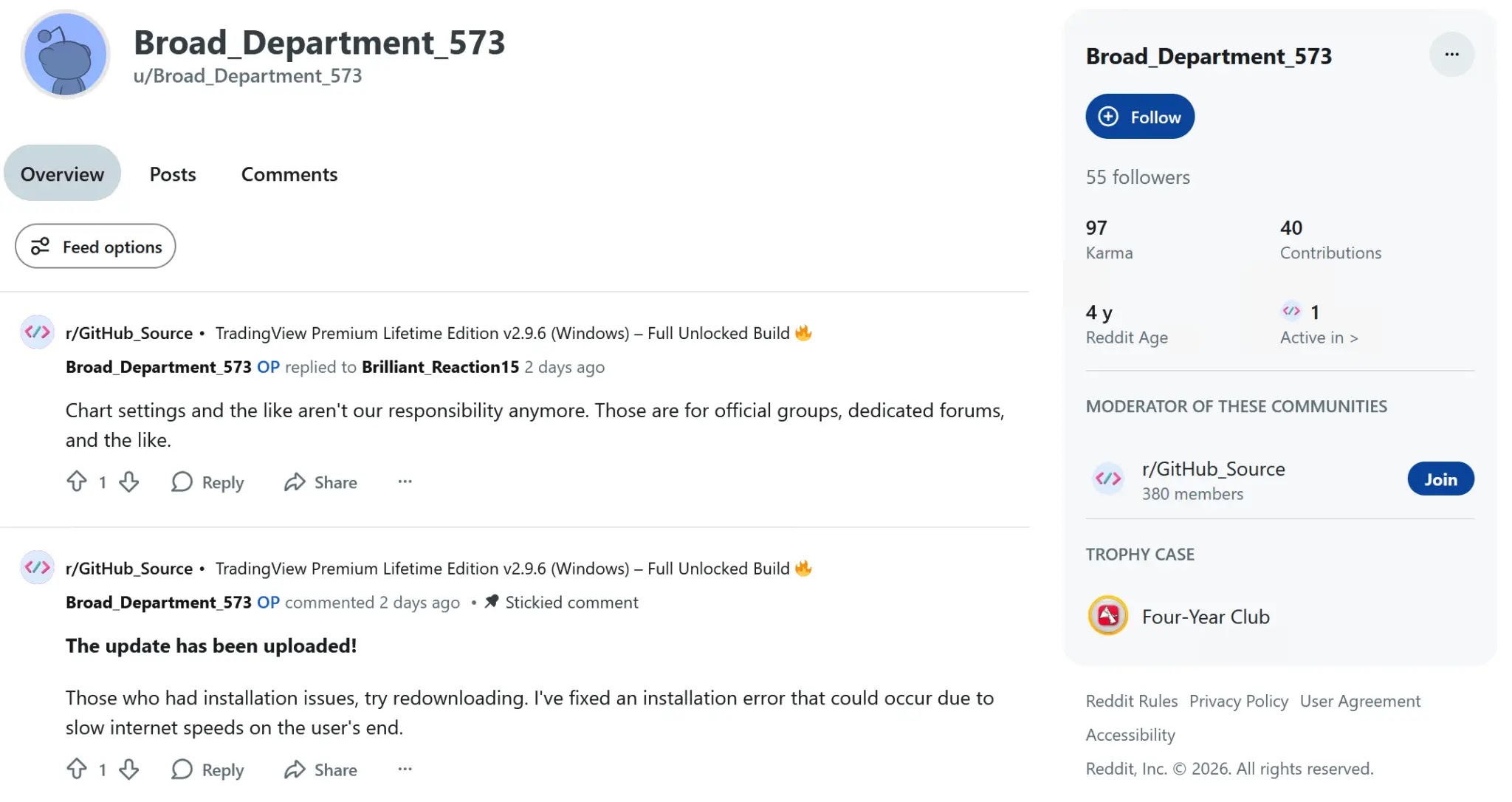
They identified a single threat actor operating across at least five subreddits, using aged, purchased, or compromised accounts to appear credible.
What stands out is not technical complexity but operational discipline — hosting domains get swapped the moment they are flagged, warning comments from real users are deleted within minutes, and the posts appear LLM-generated to keep a consistent tone.
The subreddits tell a clear story. r/BitBullito and r/CryptoCurrencyDM had just two and 29 subscribers respectively, while the accounts posting in them were three to six years old — lending false legitimacy to the operation.
One account, u/BroadDepartment573, carried a Four Year Club Reddit trophy but had only a single post across its entire history.
Every post follows the same template, claiming the software was reverse engineered with all license checks removed.
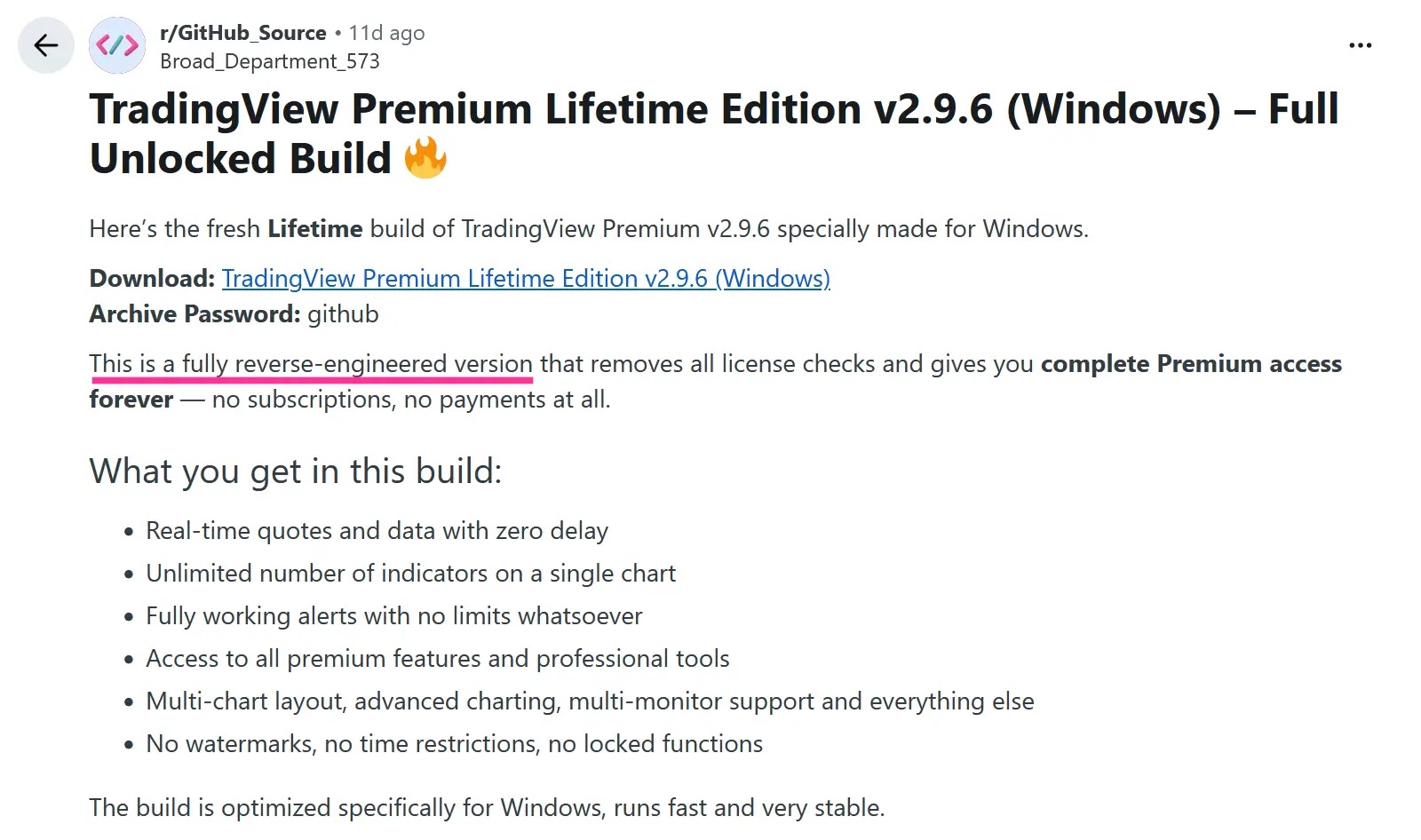
Separate download links are offered for Windows, macOS, and macOS 15 — a level of platform targeting that shows the actor understands Apple’s Gatekeeper restrictions in macOS Sequoia.
The Infection Mechanism
Payloads are hosted on compromised legitimate business websites, lending added credibility to the download links.
On Windows, the extracted executable is bloated to over 784 megabytes through null-byte padding in its PE resource section, deliberately sized to exceed antivirus scan limits.
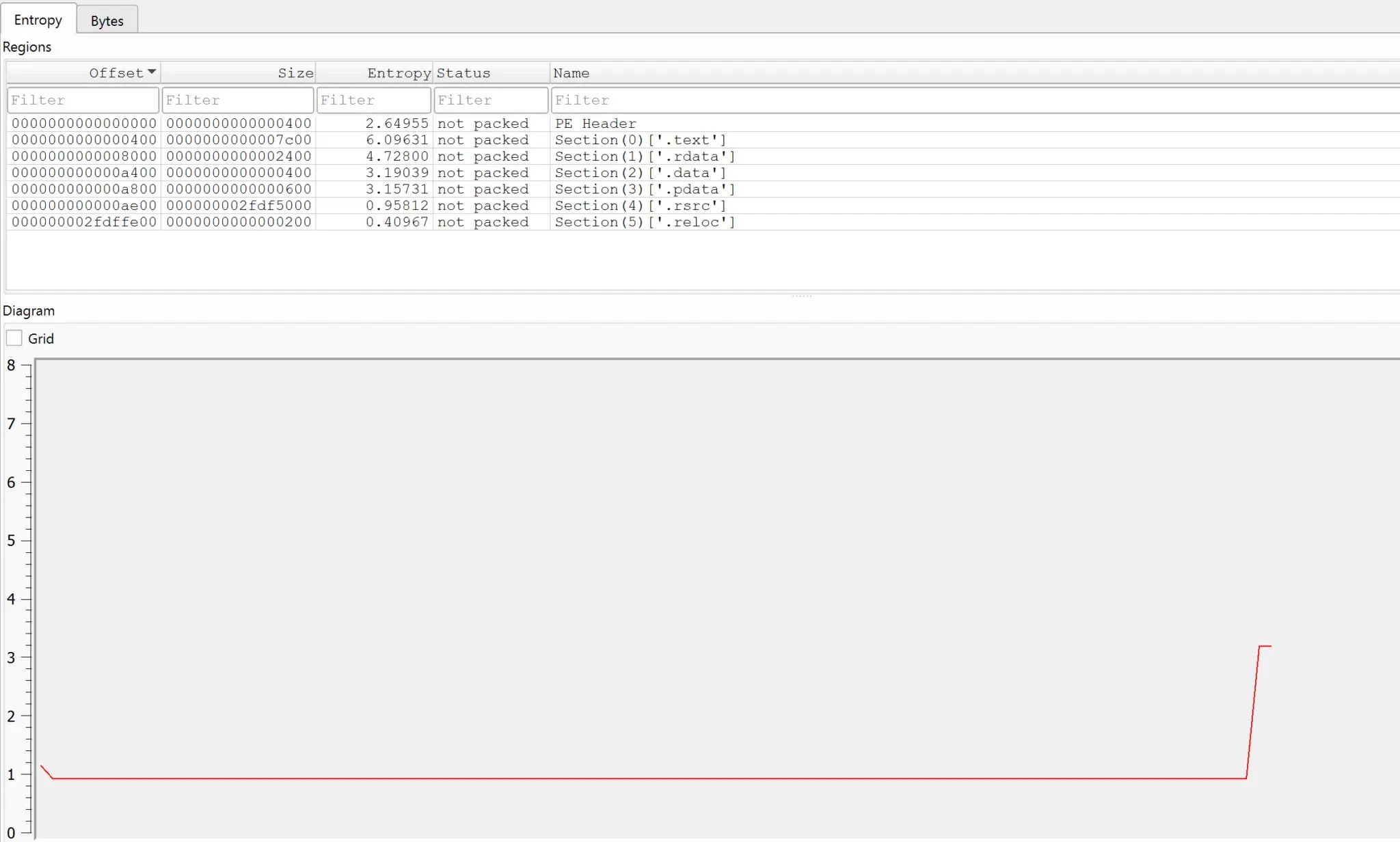
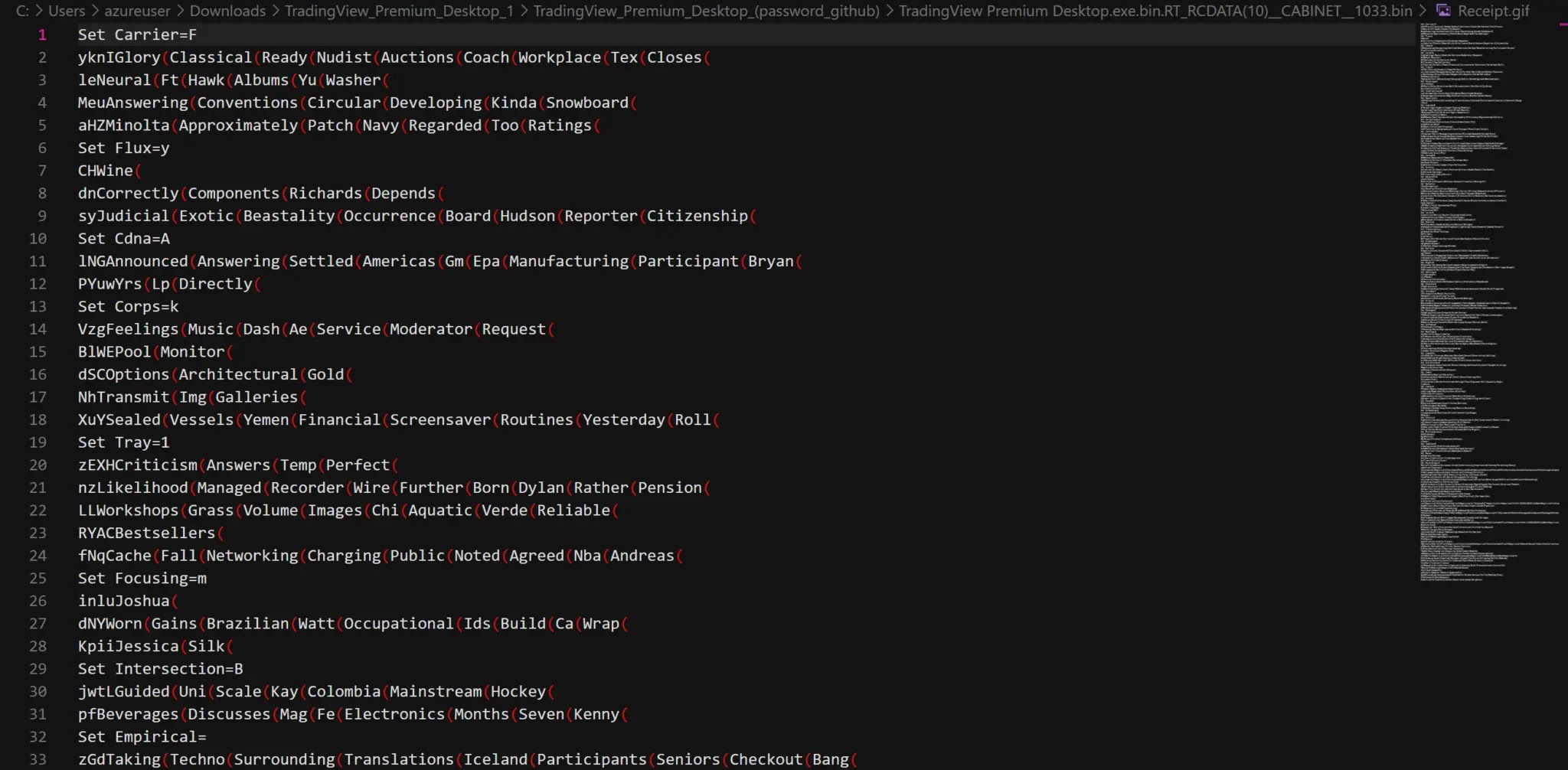
Beneath the padding sits a 44-kilobyte self-extracting cabinet that drops a batch script named Receipt.gif.
Despite the image extension, it is a 235-line obfuscated script that reassembles a Vidar infostealer from split file fragments using character substitution to defeat signature-based detection.
The archive password — either “github” or “codeberg” — is posted directly in the Reddit thread, both names chosen to evoke legitimate developer platforms and lower suspicion.
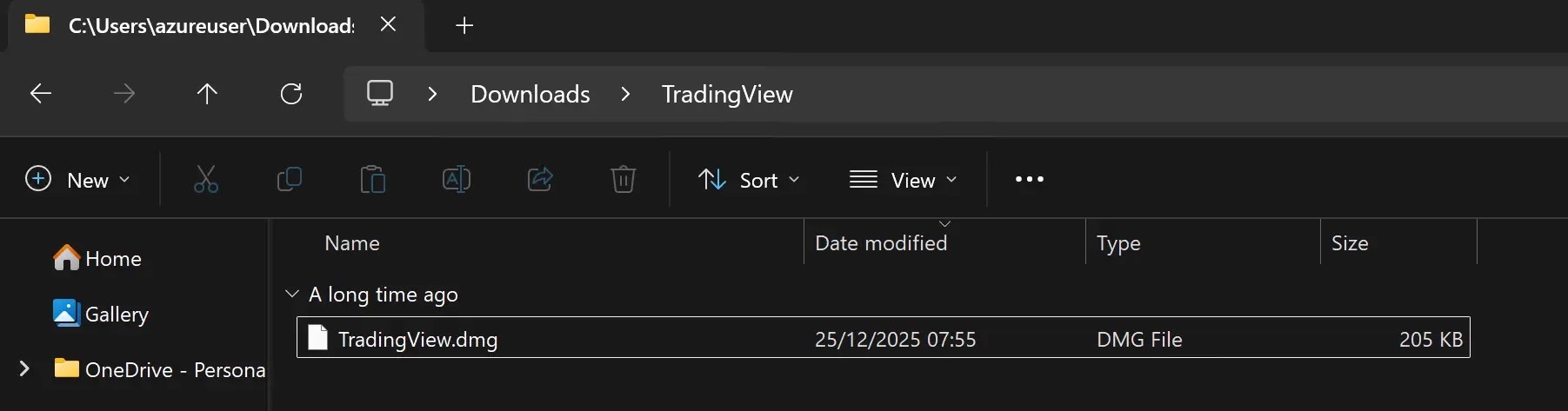
On macOS, the download is a disk image that mounts with a TradingView-branded background to mimic a real installer. Inside sits a compact 217-kilobyte Mach-O binary that decrypts an AMOS stealer at runtime through a polymorphic XOR loop.
Once executed, AMOS harvests credentials and cookies from Chrome, Firefox, Safari, Brave, Edge, and Opera, copies wallet files from Exodus, Electrum, and MetaMask, and exfiltrates everything over HTTP within seconds.
Organizations should add the identified distribution domains to web proxy and DNS blocklists, and hunt for patterns where Reddit browsing is followed quickly by a large ZIP download from an unrelated domain.
On Windows, flag wextract.exe spawning cmd.exe with delayed variable expansion. On macOS, monitor for unsigned applications calling osascript or making unexpected dscl authonly credential validation attempts.
Anyone with any doubt about exposure should treat it as a confirmed compromise — browser passwords, session cookies, and crypto wallet keys should all be considered stolen. Downloading cracked software remains one of the most reliable ways threat actors find victims today.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.