Hackers Abuse Signed Logitech Installer for TCLBANK
A new banking trojan, dubbed TCLBANKER, has been identified in the wild, utilizing a sophisticated and concerning delivery method. Threat actors are exploiting a trojanized version of a legitimate,...
A new banking trojan, dubbed TCLBANKER, has been identified in the wild, utilizing a sophisticated and concerning delivery method. Threat actors are exploiting a trojanized version of a legitimate, digitally signed installer to deploy this malware onto victim systems, effectively bypassing initial security scrutiny. A detailed analysis of this campaign further outlines the new threat and its operational tactics. You can
The campaign, tracked as REF3076, bundles a malicious MSI installer inside a ZIP file and exploits the trust people place in recognizable software names.
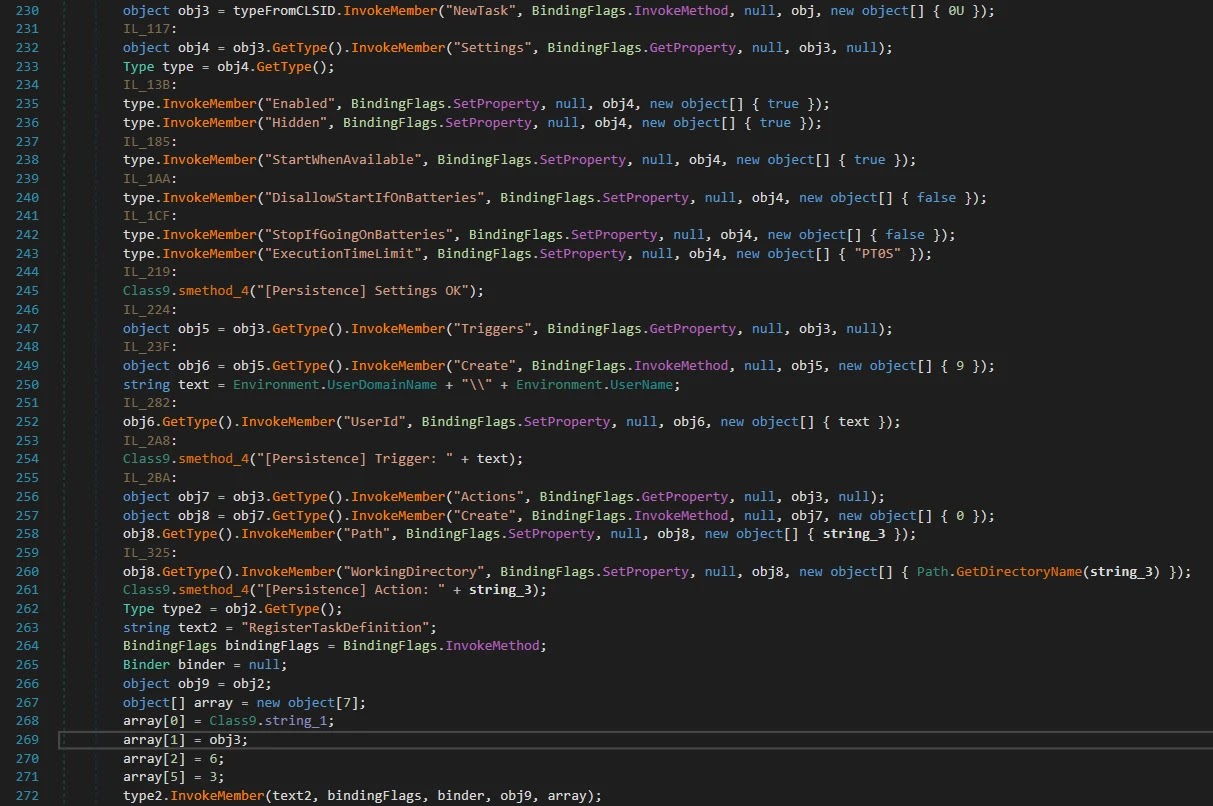
The infection begins when a victim runs what appears to be a legitimate Logitech application installer. Inside the package, threat actors have weaponized the Logi AI Prompt Builder, abusing a technique called DLL sideloading to sneak a malicious file into the process. Once the application starts, it automatically loads the harmful DLL without the user ever knowing anything went wrong.
Analysts at Elastic Security Labs identified this new Brazilian banking trojan, assessing it to be a significant evolution of an older malware family known as MAVERICK and SORVEPOTEL. The campaign appears to be in its early stages, with developer artifacts and an incomplete phishing page suggesting the attackers are still actively building out their infrastructure.
TCLBANKER primarily targets users in Brazil, specifically those who visit banking, fintech, and cryptocurrency websites. The trojan monitors the victim’s browser in real time, watching for visits to any of 59 targeted financial domains.
Hackers Abuse Signed Logitech Installer
When a match is found, it opens a live connection to the attacker’s command server and puts the operator in full control.
The scope of potential damage goes well beyond simple credential theft. The malware can display fake full-screen overlays that look like real banking interfaces, freeze the apparent desktop to confuse victims, and kill the Task Manager to prevent users from ending the malicious process. It is a coordinated operation designed to make fraud feel seamless from the attacker’s side.
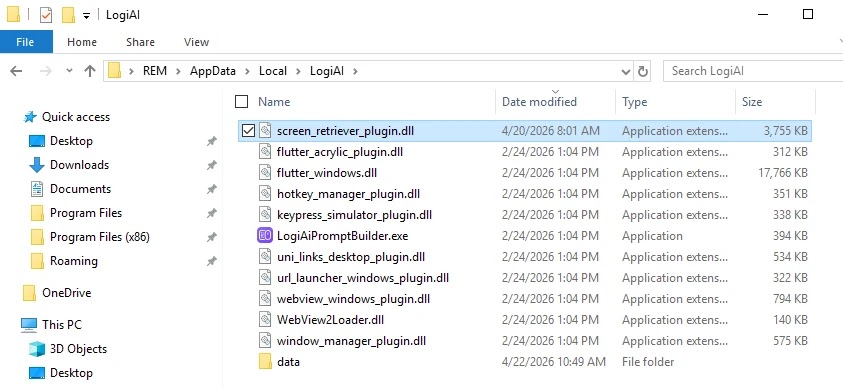
The attackers took care to make the infection chain look as normal as possible. The malicious ZIP file contains an MSI installer that mimics the legitimate Logi AI Prompt Builder, a real Flutter-based application.
When installed, the trojanized package drops a fake DLL called screen_retriever_plugin.dll, which masquerades as a genuine Flutter plugin and gets loaded automatically at startup.
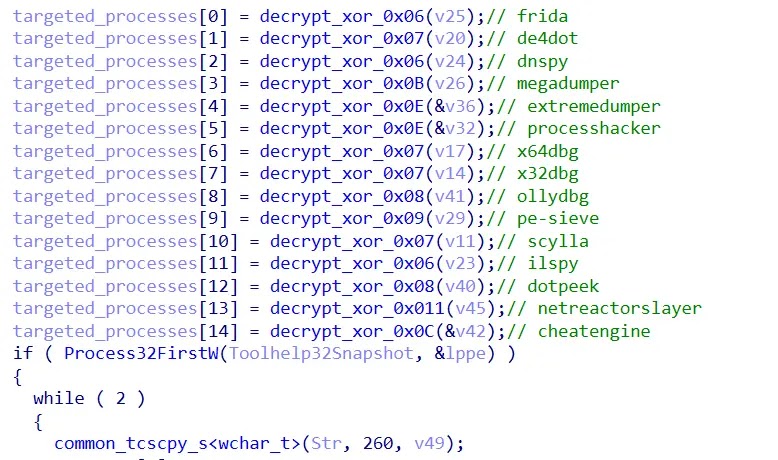
The loader inside this DLL is packed with tricks to avoid detection. It checks whether the system is running inside a sandbox or virtual machine, verifies that the user’s default language is Brazilian Portuguese, and even measures timing to catch emulation frameworks that speed up sleep calls.
If anything seems off, the malware simply stops running without leaving obvious traces. This environment-gating approach means the payload only decrypts itself on real, qualifying machines.
Self-Spreading Worm Modules Amplify the Threat
What makes TCLBANKER particularly dangerous is not just what it does on a single machine, but how far it can spread from there. The malware comes with two worm modules designed to send itself to the victim’s contacts using channels those contacts already trust.
The first hijacks the victim’s active WhatsApp Web session in the browser, silently messaging Brazilian contacts with a link to download the malware. The second abuses Microsoft Outlook through automation, sending phishing emails directly from the victim’s own email account.
Because these messages come from real, known senders, they are far harder for security filters to catch. The Outlook bot first harvests the victim’s contact list, then sends targeted emails that look completely authentic.
Elastic researchers noted that all command and file-serving infrastructure runs on Cloudflare Workers under a single account, making it easy for operators to rotate infrastructure quickly when needed.
Organizations and individuals can take several steps to reduce exposure. Keeping security software updated ensures the latest detection signatures are in place.
Being cautious about ZIP files or MSI installers received through messaging apps or email, even from known contacts, is critical given this trojan’s self-spreading behavior. Monitoring for unusual scheduled tasks, unexpected DLL loads alongside legitimate software, and suspicious outbound connections can also help flag infections early.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-256 | 701d51b7be8b034c860bf97847bd59a87dca8481c4625328813746964995b626 | TCLBanker loader component (screen_retriever_plugin.dll) |
| SHA-256 | 8a174aa70a4396547045aef6c69eb0259bae1706880f4375af71085eeb537059 | TCLBanker loader component (screen_retriever_plugin.dll) |
| SHA-256 | 668f932433a24bbae89d60b24eee4a24808fc741f62c5a3043bb7c9152342f40 | TCLBanker loader component (screen_retriever_plugin.dll) |
| SHA-256 | 63beb7372098c03baab77e0dfc8e5dca5e0a7420f382708a4df79bed2d900394 | TCLBanker initial ZIP file (XXL_21042026-181516.zip) |
| Domain | campanha1-api.ef971a42[.]workers.dev | TCLBanker C2 |
| Domain | mxtestacionamentos[.]com | TCLBanker C2 |
| Domain | documents.ef971a42.workers[.]dev | TCLBanker file server |
| Domain | arquivos-omie[.]com | TCLBanker phishing page (under development) |
| Domain | documentos-online[.]com | TCLBanker phishing page (under development) |
| Domain | afonsoferragista[.]com | TCLBanker phishing page (under development) |
| Domain | doccompartilhe[.]com | TCLBanker phishing page (under development) |
| Domain | recebamais[.]com | TCLBanker phishing page (under development) |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.