PamDOORa Backdoor Attacks Linux, Attacking Systems
Linux systems are under a new, growing threat from PamDOORa, a recently identified backdoor. This malware targets one of the operating system’s most trusted components to silently steal SSH...
Linux systems are under a new, growing threat from PamDOORa, a recently identified backdoor. This malware targets one of the operating system’s most trusted components to silently steal SSH credentials.
The malware was advertised for sale on a Russian-speaking cybercrime forum called Rehub, with its complete source code initially listed at $1,600 before the seller slashed the price to $900. That sudden drop raised red flags among researchers, suggesting either limited buyer interest or a deliberate rush to offload the tool quickly.
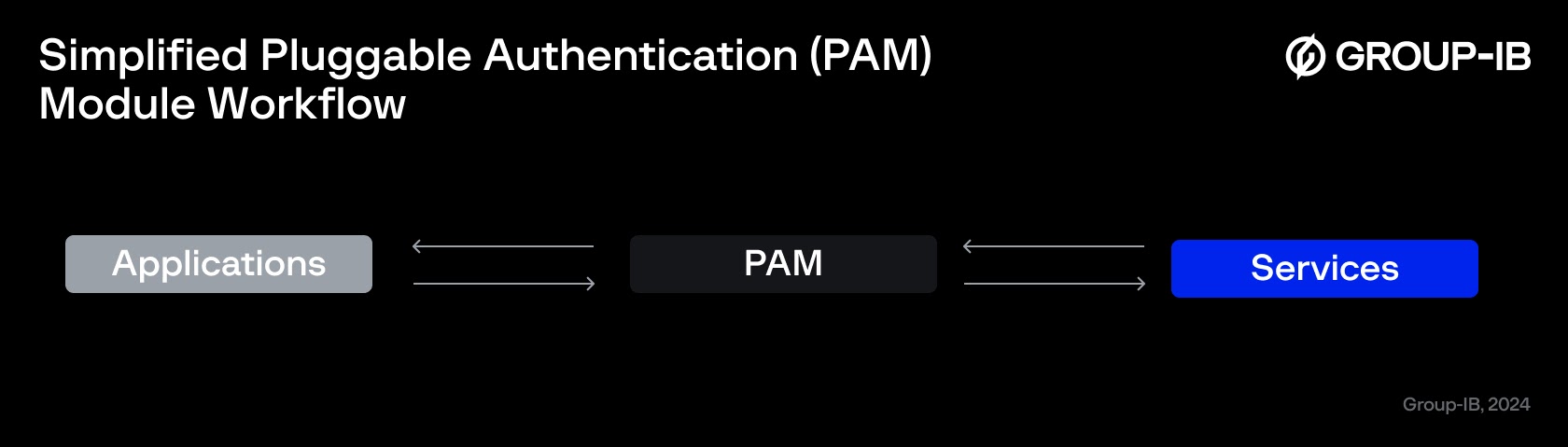
PamDOORa works by hijacking the Pluggable Authentication Module, or PAM, framework that Linux systems use to handle user logins and identity verification.
Unlike traditional malware that plants itself as a visible running process, this backdoor injects a malicious module directly into the authentication layer, where it waits silently for login attempts and harvests credentials before they can be logged. This makes it especially dangerous because the attack happens at a level most monitoring tools do not watch closely.
Researchers from Group-IB identified the technique being used in this backdoor and noted that it exploits pam_exec, a standard PAM module designed to run external commands during authentication events.
The Group-IB DFIR team found that this specific abuse method had not yet been included in the MITRE ATT&CK framework, making it a novel technique that many security teams may not be actively defending against.
How PamDOORa Operates on Linux Systems
The threat actor behind PamDOORa operates under the alias “darkworm” on the Rehub forum and demonstrates notable technical knowledge of Linux internals. Analysis of code snippets shared in the advertisement showed realistic and credible techniques that align with known PAM exploitation methods. The seller was assessed as more technically capable and serious compared to other individuals reusing the same alias on lower-tier forums.
What makes PamDOORa especially concerning is not just what it does, but how well it hides. The backdoor is built to manipulate authentication log files including lastlog, btmp, utmp, and wtmp, wiping away any trace that an attacker connected to the server. This means incident response teams called in to investigate a breach may unknowingly have their own credentials stolen the moment they SSH into the compromised machine.
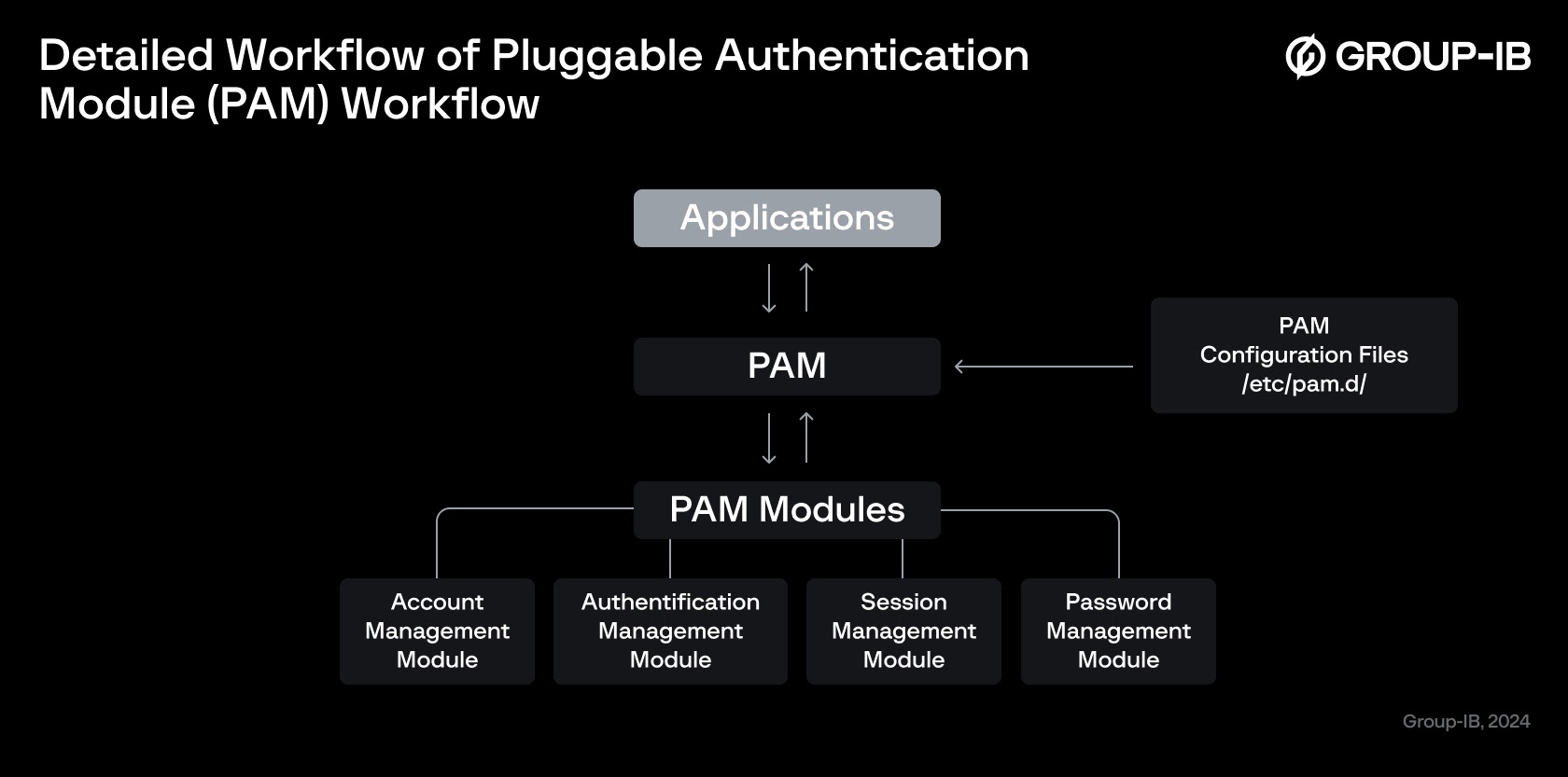
PamDOORa is designed as a post-exploitation tool, meaning the attacker must already have root access before deploying it. Once installed, the backdoor injects a malicious PAM module that produces a file called pam_linux.so, loaded into the authentication stack alongside legitimate system modules.
This design allows it to blend in with normal system files rather than replacing them, making detection significantly harder.
The backdoor grants persistent SSH access through a combination of a specific TCP port and a secret “magic password” that only the attacker knows. A special routine scans open connections and applies conditional logic to identify when the attacker is connecting, granting silent access while normal users see nothing unusual.
Credentials submitted by legitimate users during login are intercepted within the PAM stack, encrypted using XOR with a runtime-generated key, and written to /tmp with randomly generated filenames and timestamps.
Anti-Forensics and the Challenge of Detection
What sets PamDOORa apart from simpler backdoors is its built-in anti-forensic capability. The tool actively erases attacker login traces from system logs, leaving behind only failed login entries that investigators are likely to dismiss as noise.
Since credential theft happens inside the PAM layer, application-level logging tools never capture the stolen data, and detection methods focused on user-space processes will miss it entirely.
Security teams are advised to treat any compromised Linux server as having fully exposed credentials, regardless of how limited the breach appears.
Researchers recommend enabling SELinux and AppArmor for stronger process isolation, installing Auditd with DISA-STIG recommended rules to monitor changes to system files, and deploying rkhunter to detect rootkits and unauthorized software. Disabling root login over SSH, locking the root account, and restricting sudo access to authorized users only are essential steps in reducing the attack surface that PamDOORa relies on.
Indicators of Compromise (IoCs):-
Based on information disclosed in the source material, the following indicators were identified from the malicious script executed during SSH authentication:-
| Type | Indicator | Description |
|---|---|---|
| File Name | pam_linux.so | Malicious PAM shared object injected into the authentication stack |
| File Name | tn.sh | Script executed via pam_exec during SSH authentication attempts |
| Directory | /tmp/ | Location where captured credential files are written with dynamic names |
| Network Port | 1234 | Remote port used by netcat (nc) to exfiltrate stolen credential data |
| PAM Config Path | /etc/pam.d/sshd | SSH PAM configuration file modified to load the malicious module |
| PAM Module | pam_exec.so | Legitimate PAM module abused to execute the malicious script silently |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.