WhisperPair Attack Hijacks Laptops & Earbuds Allows Hijacking
A critical vulnerability in Google’s Fast Pair protocol allows attackers to hijack Bluetooth audio accessories and track users without their knowledge or consent. Security researchers from KU Leuven...
A critical vulnerability in Google’s Fast Pair protocol allows attackers to hijack Bluetooth audio accessories and track users without their knowledge or consent.
Security researchers from KU Leuven have uncovered a vulnerability, tracked as CVE-2025-36911 and dubbed WhisperPair, that affects hundreds of millions of wireless earbuds, headphones, and speakers from major manufacturers.
Including Sony, Anker, Google, Jabra, JBL, Logitech, Marshall, Nothing, OnePlus, Soundcore, and Xiaomi.
Google classified the issue as critical and awarded the researchers the maximum possible bounty of $15,000. The flaw stems from the improper implementation of the Fast Pair protocol.
Critical Flaw in Fast Pair Implementation
According to the Fast Pair specification, Bluetooth accessories should ignore pairing requests when not in pairing mode.
However, many flagship devices fail to enforce this critical security check, allowing unauthorized devices to initiate the pairing process without user interaction.
Attackers can exploit WhisperPair using any standard Bluetooth-capable device such as a laptop, smartphone, or Raspberry Pi.
The attack succeeds within a median of 10 seconds at ranges up to 14 meters without requiring physical access to the vulnerable device.
Once paired, attackers gain complete control over the audio accessory, enabling them to play audio at high volumes or record conversations through the built-in microphone.
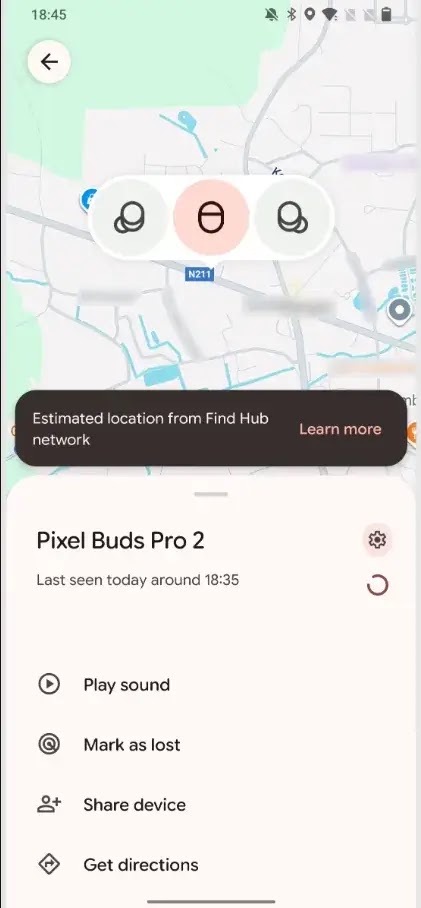
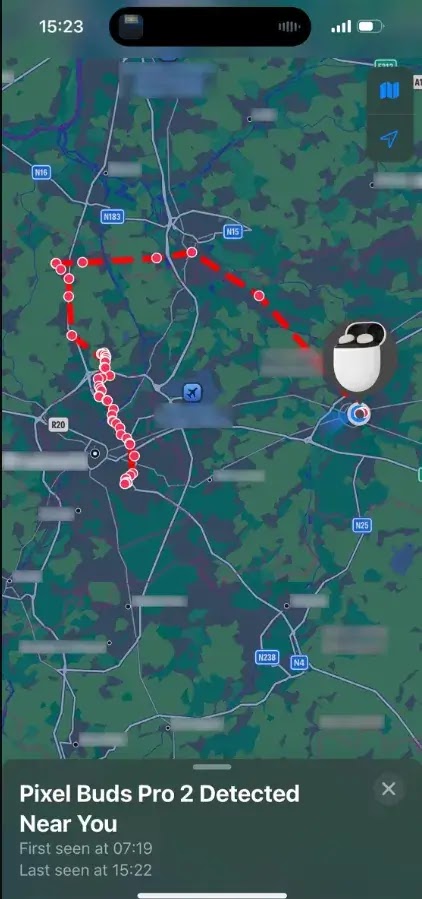
Additionally, if an accessory has never been paired with an Android device, attackers can add it to their own Google account and track the victim’s location using Google’s Find Hub network.
The tracking notification that appears shows the victim’s own device, which may lead users to dismiss the warning as a system bug, allowing prolonged surveillance.
Cross-Platform Vulnerability
The vulnerability affects users across all platforms because the flaw exists in the accessories themselves, not in smartphones.
iPhone users with vulnerable Bluetooth devices face the same risks as Android users. Since Fast Pair functionality cannot be disabled on accessories, even users outside the Android ecosystem remain vulnerable.
The WhisperPair researchers reported their findings to Google in August 2025, agreeing to a 150-day disclosure window for manufacturers to release security patches.
The only effective mitigation is installing firmware updates from device manufacturers.
While many manufacturers have released patches, software updates may not yet be available for all vulnerable devices.
Users should consult their accessory’s manual for firmware update instructions and verify patch availability directly with manufacturers.
The WhisperPair vulnerability represents a systemic failure, as vulnerable devices passed both manufacturer quality assurance and Google’s certification process before reaching the market at scale.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.