Silver Fox Deploys ValleyRAT & ABCDoor Via Fake Uses Notices
The Chinese-linked threat group known as Silver Fox is actively conducting a calculated phishing campaign. This operation targets employees across multiple countries, deceiving them into opening what...
The Chinese-linked threat group known as Silver Fox is actively conducting a calculated phishing campaign. This operation targets employees across multiple countries, deceiving them into opening what appear to be official tax authority notices.
The emails, disguised as legitimate government communications, led victims to download a chain of malware that ultimately installed both the known ValleyRAT backdoor and a newly discovered Python-based implant called ABCDoor.
The campaign was first spotted in December 2025, when a wave of phishing emails impersonated the Indian tax service.
Weeks later, in January 2026, the same group launched a nearly identical operation against organizations in Russia.
Both waves used emails formatted as tax audit notices or warnings about alleged tax violations, pushing recipients to download an archive file described as a “list of tax violations.”
The attacks hit organizations across industrial, consulting, retail, and transportation sectors, with over 1,600 malicious emails recorded between early January and early February 2026 alone.
Securelist analysts identified and attributed this activity to the Silver Fox threat group. Their investigation revealed that in addition to deploying ValleyRAT, the attackers were also delivering a brand new, previously undocumented backdoor through a custom ValleyRAT plugin, which they named ABCDoor based on the “abc” third-level domain pattern consistently seen across its command-and-control (C2) addresses.
Retrospective analysis confirmed that ABCDoor had been part of Silver Fox’s toolkit since at least late 2024 and had been used in real attacks from the first quarter of 2025.
What makes this campaign particularly dangerous is not just the malware used, but the deliberate social engineering behind it.
Tax notices are taken seriously by employees, and the urgency created by a supposed government audit is enough to push people into clicking links without careful thought.
The PDF attachments in the phishing emails contained download links instead of embedded malicious code, a deliberate tactic to slip past email security gateways that scan for direct malware attachments.
How the Infection Chain Works: From Fake PDF to Full System Takeover
Once the victim clicks the download link in the phishing PDF, they retrieve a compressed archive containing a modified Rust-based loader called RustSL.
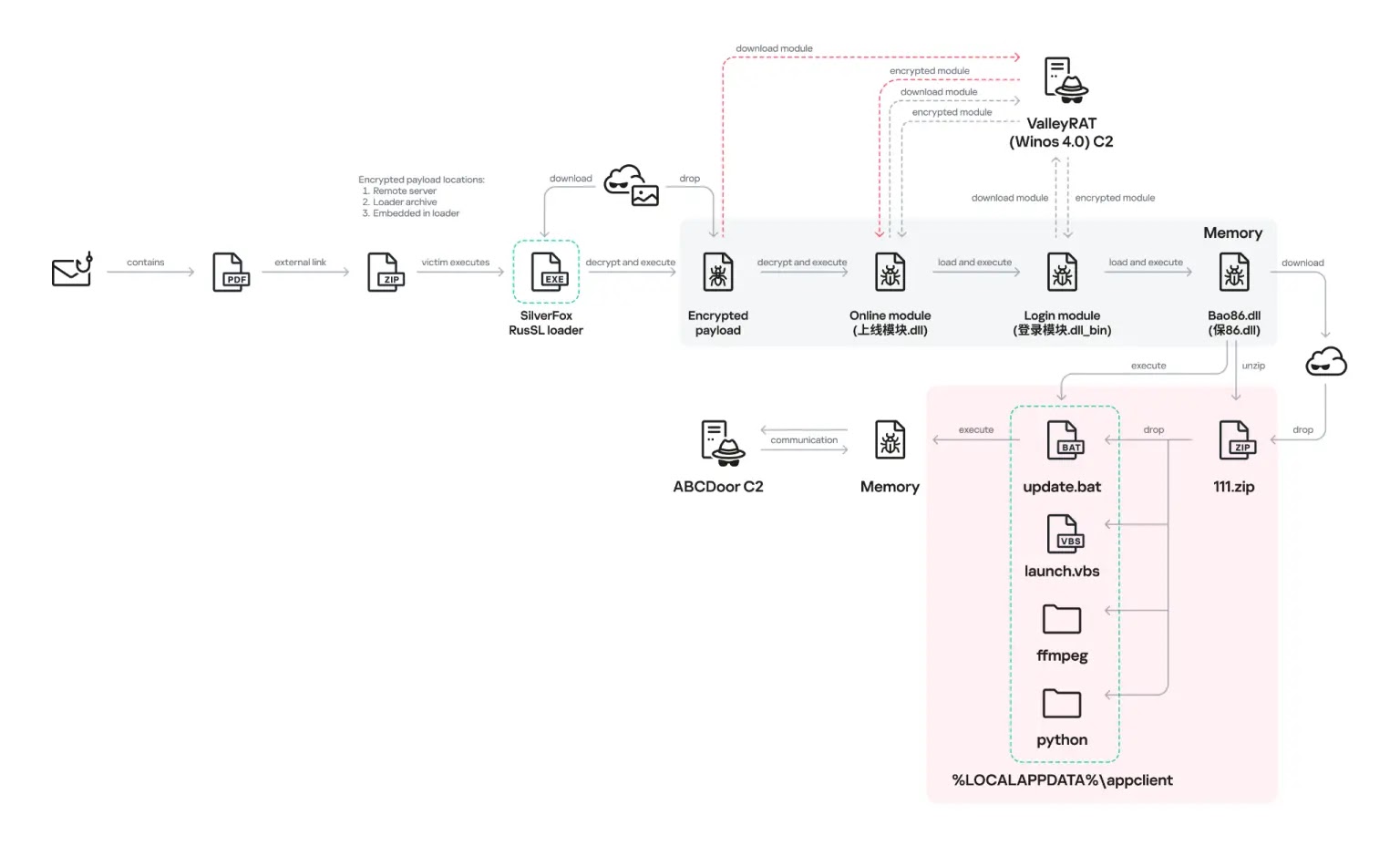
Silver Fox pulled this loader’s source code from a public GitHub repository and made significant modifications to it.
The customized version, referred to as Silver Fox RustSL, includes a new module called steganography.rs that handles payload unpacking, as well as a guard.rs module that performs environment checks and country-based geofencing to ensure the malware only runs on devices in targeted countries, including India, Russia, Indonesia, South Africa, Cambodia, and later Japan.
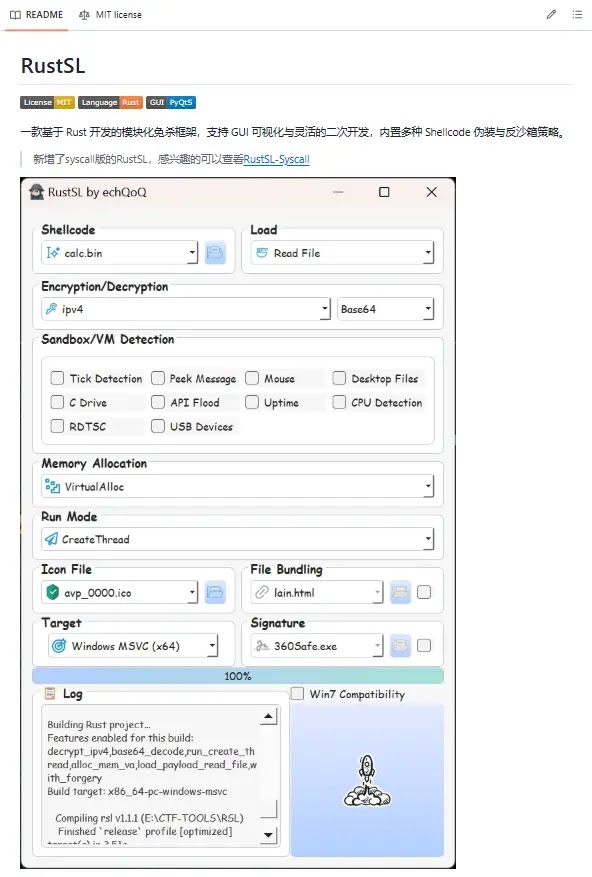
The loader is disguised with a PDF or Excel file icon to avoid raising suspicion. When the user runs it, RustSL loads an encrypted payload that functions as shellcode. This shellcode then downloads an encrypted ValleyRAT module called the “Online module” from the attackers’ server.
The Online module loads the core ValleyRAT component, the “Login module,” which manages C2 communication, executes commands, and downloads further payloads. One such additional payload is a custom ValleyRAT plugin named 保86.dll, which acts as a downloader for ABCDoor.
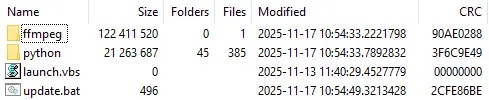
ABCDoor is a Python-based backdoor compiled with Cython 3.0.7, which helps mask its source code.
It is extracted alongside a bundled Python environment and a copy of ffmpeg.exe, a legitimate audio and video tool that the malware repurposes for screen capture and broadcasting.
Once active, ABCDoor establishes persistence in two ways: by writing itself to the Windows registry Run key and by creating a scheduled task named “AppClient” that restarts it every minute.
It disguises its installation path under C:ProgramDataTailscale, mimicking the name of the legitimate Tailscale VPN utility to blend into the system and mislead analysts.
Silver Fox RustSL also introduces a technique called Phantom Persistence, which intercepts system shutdown signals, aborts the shutdown, and triggers a reboot that re-executes the loader, ensuring the malware survives restarts.
Running within a legitimate pythonw.exe process, ABCDoor is able to stay hidden for extended periods while quietly collecting screen data, exfiltrating clipboard contents, managing files, and emulating mouse and keyboard input on the victim’s machine.
Organizations are strongly advised to train employees to verify emails claiming to be from tax authorities before downloading any attachments or clicking embedded links.
Email security solutions should be configured to flag and analyze PDF files containing external download links, not just direct file attachments.
Monitoring for unusual registry modifications, scheduled tasks named “AppClient,” the creation of directories at C:ProgramDataTailscale, and outbound connections to third-level “abc” subdomains can help detect this threat early.
Any suspicious use of pythonw.exe as a persistent process or unexplained ffmpeg.exe activity on endpoints should also be treated as a potential indicator of ABCDoor infection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.