DAEMON Tools Hacked: Supply Chain Attack Software Deliver
A sophisticated supply chain attack, uncovered in early May 2026, has compromised DAEMON Tools, the widely used disk image mounting software. This incident has enabled the delivery of malicious...
A sophisticated supply chain attack, uncovered in early May 2026, has compromised DAEMON Tools, the widely used disk image mounting software. This incident has enabled the delivery of malicious payloads to users worldwide.
Table Of Content
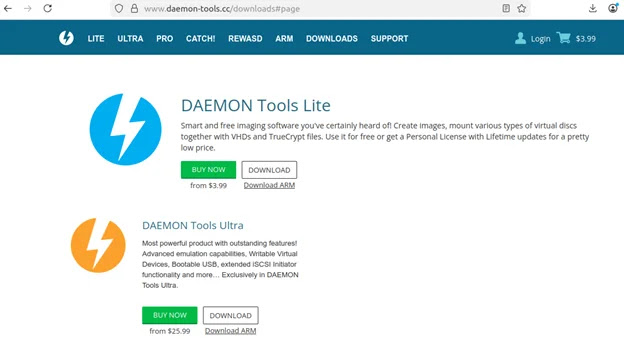
Kaspersky security researchers identified that official installers distributed from the legitimate DAEMON Tools website were trojanized starting on April 8, 2026.
These compromised installers, spanning versions 12.5.0.2421 to 12.5.0.2434, are notably signed with valid digital certificates belonging to the software’s developer, AVB Disc Soft. While thousands of infection attempts have been recorded across more than 100 countries, the threat actors demonstrated highly targeted post-compromise activity.
Artifacts within the malicious implants suggest the involvement of a Chinese-speaking threat actor, though definitive attribution remains unconfirmed. Following the discovery, AVB Disc Soft was notified to facilitate immediate remediation of the attack consequences.
DAEMON Tools Software Hacked
The attack sequence begins upon the execution of specific compromised binaries within the software installation directory, namely DTHelper.exe, DiscSoftBusServiceLite.exe, and DTShellHlp.exe.
Whenever these files are launched during system startup, a backdoor embedded in the C Runtime initialization code activates. This backdoor operates in a dedicated thread and initiates HTTP GET requests to a malicious command-and-control server designed to typosquat the legitimate domain.
Registered just over a week before the campaign commenced, this server responds with shell commands that utilize PowerShell to download and execute the first-stage payload.
This initial payload acts as an advanced information collector, compiling extensive system profiling data such as MAC addresses, hostnames, running processes, installed software, and system locales.
Embedded within this .NET executable are strings written in Chinese, providing early clues regarding the potential origin of the operators.
Telemetry data indicates that the threat actors sifted through the massive volume of profiling data to select high-value targets for subsequent exploitation.
Out of thousands of initial infections, only about a dozen machines belonging to government, scientific, manufacturing, and retail sectors in Russia, Belarus, and Thailand received a secondary payload.
This second stage is a minimalistic backdoor deployed via a shellcode loader that utilizes RC4 encryption to execute the malicious payload directly in memory.
Minimalistic Backdoor and QUIC RAT Deployment
Intriguingly, Kaspersky researchers noted misspellings such as “chiper” and “rypto.dll” in the deployment commands, suggesting that this phase involved hands-on, manual execution by the attackers.
For the most valuable targets, this minimalistic backdoor paved the way for an even more sophisticated implant dubbed QUIC RAT.
Identified exclusively on the network of a Russian educational institution, QUIC RAT is a highly obfuscated C++ backdoor statically linked with the WolfSSL library.
It supports a vast array of communication protocols, including HTTP/3 and QUIC, and actively injects payloads into core system processes like notepad.exe and conhost.exe to evade detection.
The DAEMON Tools compromise highlights a severe escalation in software supply chain attacks throughout the first half of 2026. Following similar high-profile breaches involving eScan in January, Notepad++ in February, and CPU-Z in April, advanced threat actors are increasingly weaponizing trusted applications to bypass traditional perimeter defenses.
The DAEMON Tools incident required approximately a month to uncover, a detection timeline that is reminiscent of the highly complex 3CX supply chain attack of 2023.
Organizations are strongly advised to scrutinize any endpoints running DAEMON Tools for anomalous network connections or suspicious process executions originating on or after April 8.
Given this continuous surge in supply chain compromises, security teams must rigorously enforce Zero Trust architectures and implement comprehensive endpoint monitoring to defend against threat actors exploiting widely trusted software ecosystems.
To assist in threat hunting and incident response, security teams should actively monitor for the information collector payload utilizing the SHA1 hash 2d4eb55b01f59c62c6de9aacba9b47267d398fe4, and block all outbound communications to the typosquatted domain env-check.daemontools[.]cc as well as the hardcoded IP address 38.180.107[.]76.
Indicators of Compromise
| Type | Indicator | Notes |
|---|---|---|
| SHA1 — Infected Installer | 9ccd769624de98eeeb12714ff1707ec4f5bf196d | DAEMON Tools Lite v12.5.0.2421 |
| SHA1 — Infected Installer | 50d47adb6dd45215c7cb4c68bae28b129ca09645 | DAEMON Tools Lite v12.5.0.2422 |
| SHA1 — Infected Installer | 0c1d3da9c7a651ba40b40e12d48ebd32b3f31820 | DAEMON Tools Lite v12.5.0.2423 |
| SHA1 — Infected Installer | 28b72576d67ae21d9587d782942628ea46dcc870 | DAEMON Tools Lite v12.5.0.2424 |
| SHA1 — Infected Installer | 46b90bf370e60d61075d3472828fdc0b85ab0492 | DAEMON Tools Lite v12.5.0.2430 |
| SHA1 — Infected Installer | 6325179f442e5b1a716580cd70dea644ac9ecd18 | DAEMON Tools Lite v12.5.0.2431 |
| SHA1 — Infected Installer | bd8fbb5e6842df8683163adbd6a36136164eac58 | DAEMON Tools Lite v12.5.0.2433 |
| SHA1 — Infected Installer | 15ed5c3384e12fe4314ad6edbd1dcccf5ac1ee29 | DAEMON Tools Lite v12.5.0.2434 |
| SHA1 — Modified Binary | 524d2d92909eef80c406e87a0fc37d7bb4dadc14 | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Modified Binary | 427f1728682ebc7ffe3300fef67d0e3cb6b62948 | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Modified Binary | 8e7eb0f5ac60dd3b4a9474d2544348c3bda48045 | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Modified Binary | 00e2df8f42d14072e4385e500d4669ec783aa517 | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Modified Binary | aea55e42c4436236278e5692d3dcbcbe5fe6ce0b | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Modified Binary | 0456e2f5f56ec8ed16078941248e7cbba9f1c8eb | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Modified Binary | 9a09ad7b7e9ff7a465aa1150541e231189911afb | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Modified Binary | 8d435918d304fc38d54b104a13f2e33e8e598c82 | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Modified Binary | 64462f751788f529c1eb09023b26a47792ecdc54 | Trojanized DiscSoftBusServiceLite.exe |
| SHA1 — Payload | 2d4eb55b01f59c62c6de9aacba9b47267d398fe4 | Information collector (envchk.exe) |
| SHA1 — Payload | 9dbfc23ebf36b3c0b56d2f93116abb32656c42e4 | Minimalistic backdoor shellcode |
| SHA1 — Payload | 295ce86226b933e7262c2ce4b36bdd6c389aaaef | Minimalistic backdoor shellcode |
| File Path | C:WindowsTempenvchk.exe | Information collector drop path |
| File Path | C:WindowsTempcdg.exe | Shellcode loader drop path |
| File Path | C:WindowsTempimp.tmp | Shellcode payload drop path |
| File Path | C:WindowsTemppiyu.exe | Additional payload drop path |
| C2 Domain | env-check.daemontools[.]cc | Malicious C2, typosquats daemon-tools[.]cc |
| C2 IP Address | 38.180.107[.]76 | Hardcoded payload delivery server |
[.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.