New Framework Connects APT Campaigns Across All Layers
Pinpointing the origins of Advanced Persistent Threat (APT) campaigns remains a complex challenge for the cybersecurity community. For years, analysts have relied on correlating consistent behaviors,...
Pinpointing the origins of Advanced Persistent Threat (APT) campaigns remains a complex challenge for the cybersecurity community. For years, analysts have relied on correlating consistent behaviors, tools, and infrastructure to attribute malicious activity to specific threat actors.
But that approach is showing serious cracks, as APT groups are not the rigid, predictable entities they were once assumed to be.
The old method of following Tactics, Techniques, and Procedures (TTPs) was practical when threat actors stayed consistent.
The problem today is that adversaries change operators, swap tools, rebuild infrastructure, and reshape objectives, sometimes within a single campaign cycle.
This leaves analysts working with fragmented signals and no reliable thread to connect the dots. The growing gap between how defenders track threats and how those threats actually behave has pushed researchers toward a fundamentally different way of thinking about attribution.
DarkAtlas analysts identified this structural gap and introduced a campaign-based attribution framework designed to address the limitations of traditional group-centric models.
Rather than treating APT groups as fixed identities, the framework focuses on discrete, time-bound clusters of activity called campaigns, where each cluster is defined by its objectives, infrastructure patterns, and operational behavior.
The key insight is that continuity between campaigns does not require identical TTPs. Instead, it is inferred through partial overlaps across multiple independent evidence layers.
The framework draws on what researchers describe as the “Ship of Theseus” problem in attribution. If an adversary group replaces every component of its operation, from personnel to tools to infrastructure, is it still the same group? Traditional attribution models would struggle to answer that question confidently.
The new campaign-linkage approach sidesteps this paradox by measuring relationships between campaigns rather than assuming a stable group identity.
This framework does not eliminate uncertainty. Instead, it introduces a confidence-based attribution model where conclusions are expressed as high, medium, or low confidence depending on how many independent evidence layers converge.
High-confidence attribution requires strong, multi-layered overlap across strategic, operational, technical, infrastructure, and human dimensions.
Medium confidence reflects partial alignment, and low confidence applies when only a single dimension shows similarity or when data is limited.
How the Overlap Model Works in Practice
At the core of the framework is what DarkAtlas researchers call the Overlap Model, a multi-dimensional correlation approach that replaces single-indicator attribution with layered analysis.
No single artifact, whether a reused IP address, a shared tool, or a matching technique, is treated as sufficient evidence of continuity. Attribution confidence builds only when multiple dimensions align independently.
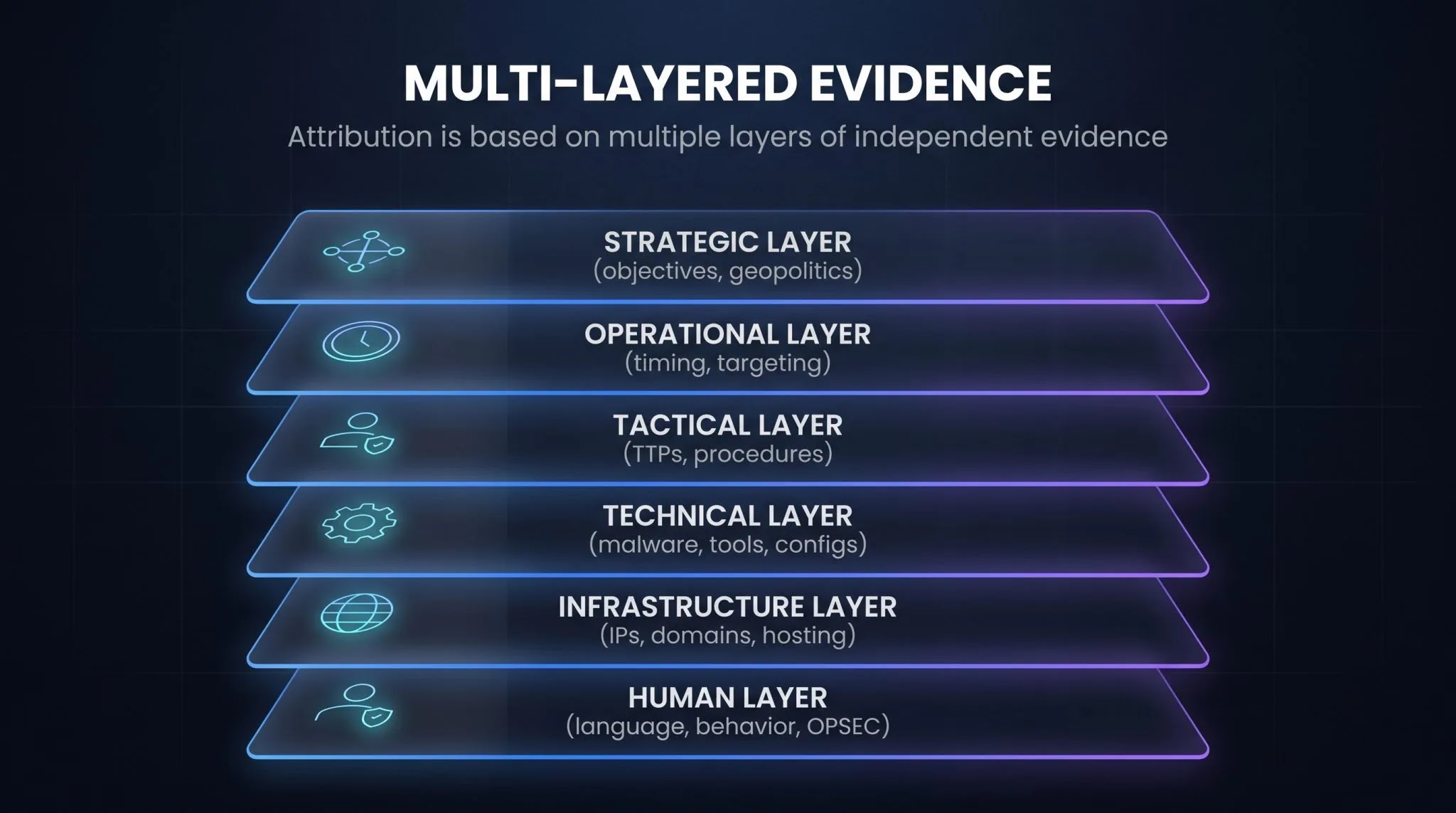
The model examines six analytical layers. The strategic layer looks at geopolitical alignment and targeting intent, which tends to remain stable even as tactics evolve.
The operational layer tracks targeting patterns, campaign timing, and victim sequencing. The tactical layer maps procedural execution against frameworks like MITRE ATT&CK, while the technical layer examines custom malware characteristics, encryption routines, and build artifacts.
The infrastructure layer studies domain naming conventions, TLS certificate reuse, and DNS behavior, and the human layer captures operator-specific traits like coding style, language artifacts, and OPSEC habits.
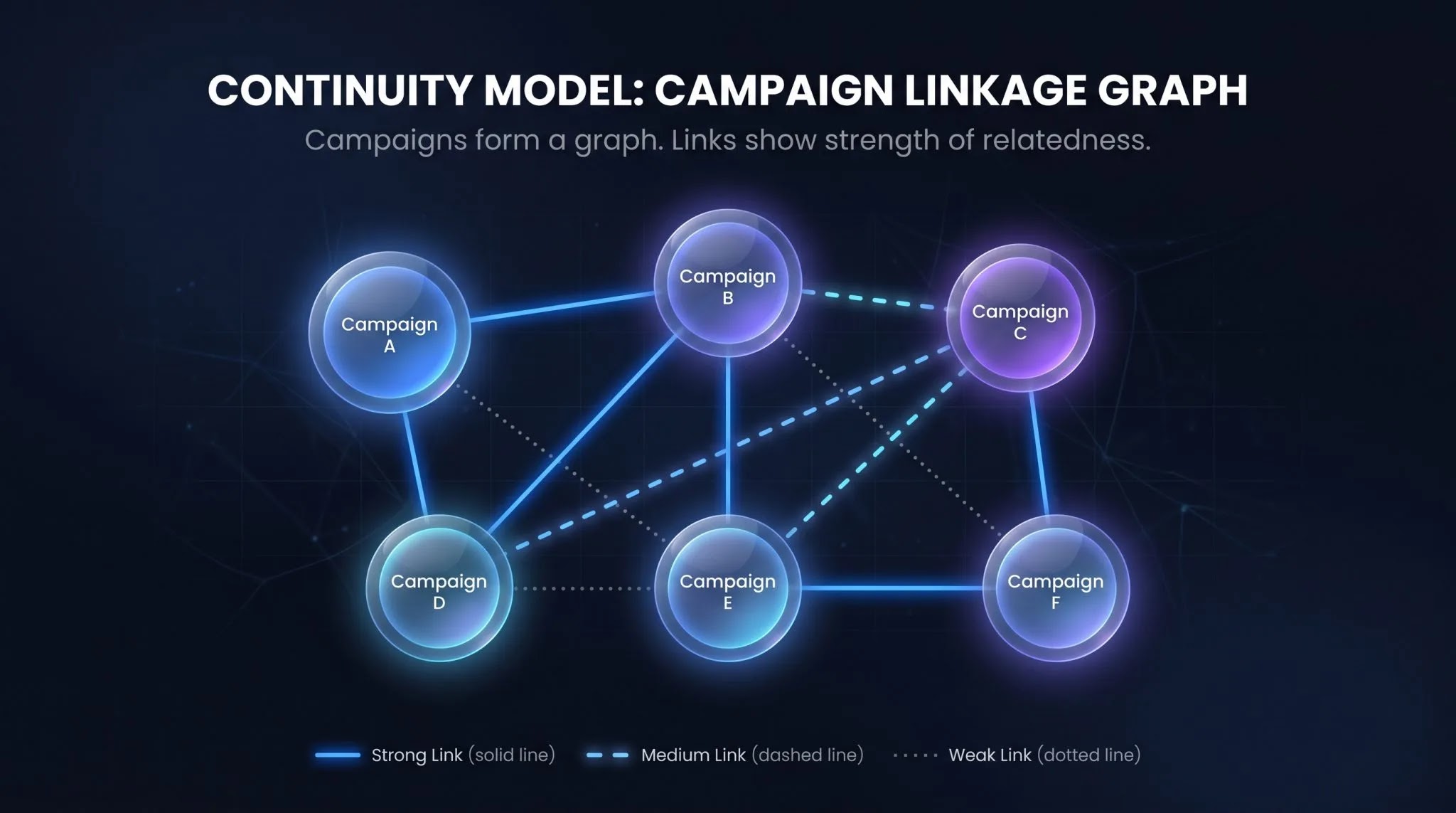
Together, these layers feed into a Campaign Linkage Graph, a structured network where each node represents a distinct campaign and each edge represents a weighted relationship between campaigns.
Strong links indicate substantial overlap across multiple layers, medium links reflect partial alignment, and weak links flag tentative connections that require further validation.
This graph-based approach handles adversary evolution naturally, absorbing tooling changes as new nodes, treating infrastructure rotation as weaker but traceable connections, and capturing group fragmentation as branching paths within the network.
Security teams and threat intelligence practitioners should consider the following based on the framework’s findings:-
- Move away from single-indicator attribution and require multi-layer evidence before drawing conclusions about campaign origin or group identity.
- Treat TTPs as behavioral signals rather than fingerprints, since adversaries routinely modify or share techniques across groups to create false attribution trails.
- Adopt a campaign-centric tracking model where each operation is logged as a discrete unit, making it easier to build relationship graphs over time without depending on group labels.
- Assign confidence tiers to all attribution assessments and revisit earlier conclusions as new campaign data emerges, particularly when infrastructure or tooling patterns resurface.
- Focus additional monitoring resources on stable indicators such as victimology and geopolitical timing, which persist longer than tools or infrastructure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.