AiTM Attack: Code of Conduct Phishing Emails Target
A large-scale phishing campaign is underway, exploiting fake “code of conduct” emails to trick employees into divulging their account credentials. The attackers did not just steal passwords. They...
A large-scale phishing campaign is underway, exploiting fake “code of conduct” emails to trick employees into divulging their account credentials.
The attackers did not just steal passwords. They went a step further by hijacking active authentication sessions through an adversary-in-the-middle (AiTM) technique, making standard multi-factor authentication (MFA) protection largely ineffective.
The campaign ran between April 14 and 16, 2026, hitting more than 35,000 users across over 13,000 organizations in 26 countries.
The United States was the primary target, accounting for 92% of all affected users. Industries such as healthcare and life sciences (19%), financial services (18%), professional services (11%), and technology and software (11%) were among the most impacted.
The emails were sent in multiple distinct waves, starting at 06:51 UTC on April 14 and concluding at 03:54 UTC on April 16.
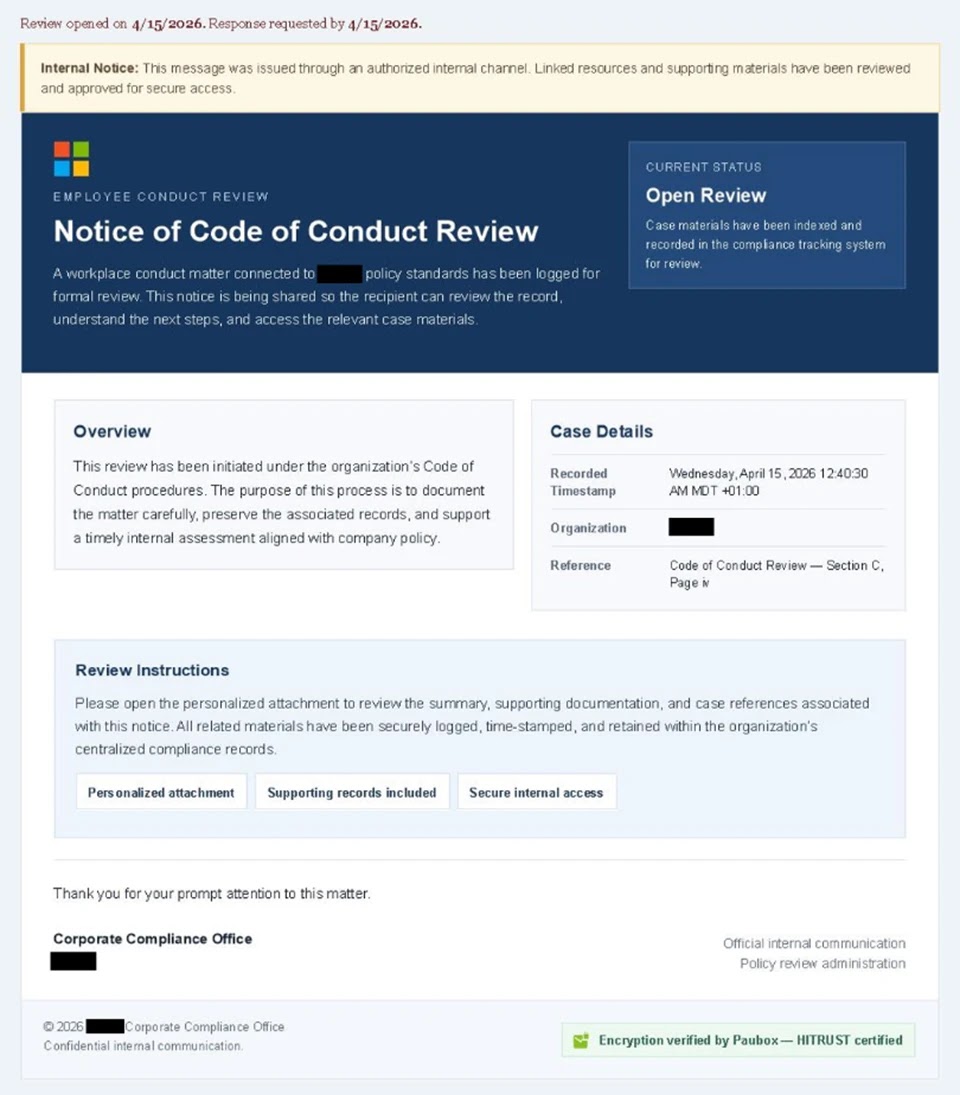
The phishing emails were crafted to look like internal compliance or regulatory notices. Display names used in the messages included “Internal Regulatory COC,” “Workforce Communications,” and “Team Conduct Report.”
Subject lines such as “Internal case log issued under conduct policy” warned recipients that a code of conduct review had been opened against them.
Each message instructed users to open a personalized PDF attachment to review their case materials. A green banner at the bottom of the emails falsely stated that the contents had been encrypted using Paubox, a legitimate HIPAA-compliant service, to give the campaign a professional and trustworthy appearance.
Microsoft Defender Research analysts identified and tracked this campaign across multiple organizations, noting that the messages were distributed through a legitimate email delivery service and likely originated from a cloud-hosted Windows virtual machine.
The team noted that attacker-controlled sending domains were used, including addresses such as [email protected] and [email protected].
Researchers also noted that the email templates used polished, enterprise-style HTML layouts with preemptive authenticity statements, making them far more convincing than typical phishing messages.
Once a recipient opened the attached PDF, which carried filenames like “Awareness Case Log File – Tuesday 14th, April 2026.pdf” and “Disciplinary Action – Employee Device Handling Case.pdf”, they were directed to click a “Review Case Materials” link.
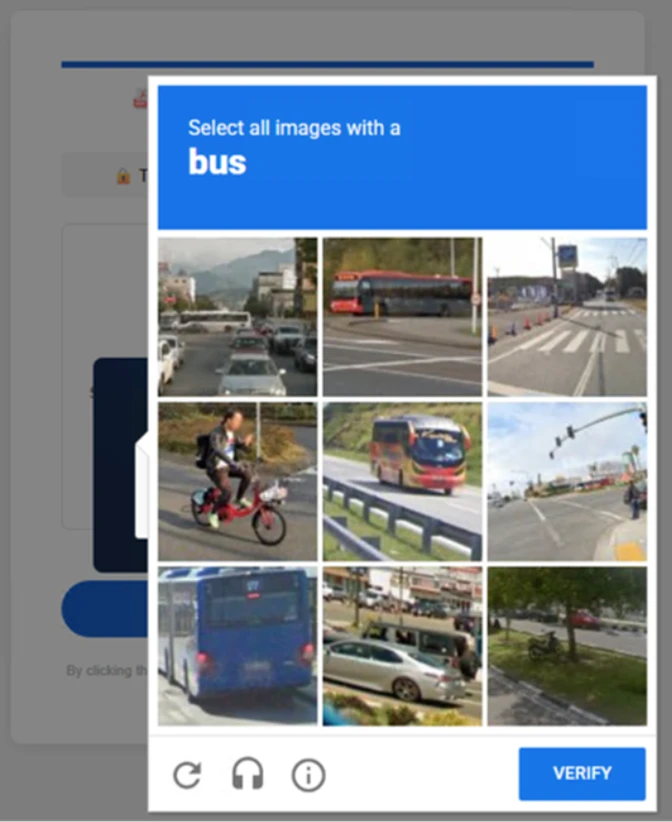
This link led to attacker-controlled landing pages hosted on domains such as compliance-protectionoutlook[.]de, where a Cloudflare CAPTCHA was presented to filter out automated security tools and sandboxes.
Inside the Multi-Stage Attack Chain
After passing the first CAPTCHA, users landed on an intermediate page that claimed the requested documentation was encrypted and required account verification.
This page prompted users to click a “Review and Sign” button and then enter their email address, followed by a second CAPTCHA involving image selection.
Once these steps were completed, users saw a confirmation message stating that their “case” was being prepared.
The final stage varied depending on whether the user was on a mobile device or a desktop. In both cases, users were told their case materials had been “securely logged” and “time-stamped,” and they were asked to sign in to schedule a discussion.
Clicking “Sign in with Microsoft” launched a real Microsoft authentication page, but the entire session was being proxied in real time by the attacker.
This is the core of an AiTM attack as the attacker sits between the user and the legitimate service, capturing authentication tokens the moment they are issued.
These tokens give direct account access without needing the user’s password again, bypassing standard MFA entirely.
Organizations and users should take the following steps to reduce risk from this type of attack. Reviewing recommended settings for Exchange Online Protection and enabling Zero-hour auto purge (ZAP) in Defender for Office 365 helps quarantine malicious messages after delivery.
Turning on Safe Links and Safe Attachments adds another detection layer for PDF-embedded phishing links. Enabling network protection in Microsoft Defender for Endpoint and encouraging use of browsers that support SmartScreen help block access to attacker-controlled domains.
Organizations should also enable phishing-resistant MFA methods such as FIDO keys, Windows Hello, or the Microsoft Authenticator app, and apply Conditional Access policies to strengthen privileged accounts.
Running user awareness training and phishing simulation exercises helps staff recognize social engineering tactics like this campaign.
Finally, configuring automatic attack disruption in Microsoft Defender XDR can limit the impact of active intrusions while security teams work to contain the threat.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.






No Comment! Be the first one.