SolyxImmortal Python Malware Steals Sensitive Data via
SolyxImmortal has emerged as an information-stealing malware, marking a notable advancement in threats targeting Windows systems. This Python-based threat combines multiple data theft capabilities...
SolyxImmortal has emerged as an information-stealing malware, marking a notable advancement in threats targeting Windows systems.
This Python-based threat combines multiple data theft capabilities into a single, persistent implant designed for long-term surveillance rather than destructive activity.
The malware operates silently in the background, collecting credentials, documents, keystrokes, and screenshots while sending stolen information directly to attackers through Discord webhooks.
Its emergence in January 2026 marks a shift toward stealthier operational models that prioritize continuous monitoring over rapid exploitation.
The attack vector centers on distributing the malware, packaged as a legitimate-looking Python script named “Lethalcompany.py,” to target systems.
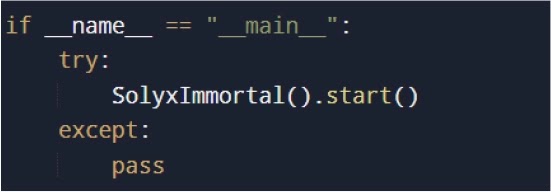
Once executed, SolyxImmortal immediately establishes persistence through multiple mechanisms and launches background surveillance threads.
The malware does not spread laterally or propagate itself; instead, it focuses entirely on harvesting data from a single compromised device.
This focused approach enables attackers to maintain long-term visibility into user activity without drawing attention.
Cyfirma analysts identified SolyxImmortal as a sophisticated threat that leverages legitimate Windows APIs and trusted platforms for command-and-control communication.
The malware’s design reflects operational maturity, emphasizing reliability and stealth over complexity.
By utilizing Discord webhooks for data transmission, attackers exploit the platform’s reputation and HTTPS encryption to avoid network-based detection.
This technique demonstrates how threat actors increasingly abuse legitimate services to hide malicious activity.
Persistence Mechanism and Browser Credential Theft
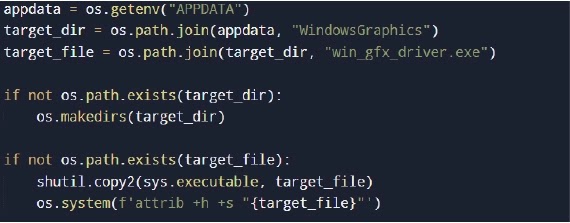
The malware establishes persistence by copying itself to a hidden location within the AppData directory, renaming it to resemble a legitimate Windows component.
It then registers itself in the Windows registry Run key, ensuring automatic execution upon each user login without requiring administrative privileges.
This approach guarantees continued operation even after system restarts.
SolyxImmortal targets multiple browsers including Chrome, Edge, Brave, and Opera GX by accessing their profile directories.
The malware extracts browser master encryption keys using Windows DPAPI, then decrypts stored credentials through AES-GCM encryption.
Recovered credentials appear in plaintext format before exfiltration, indicating minimal local security measures.
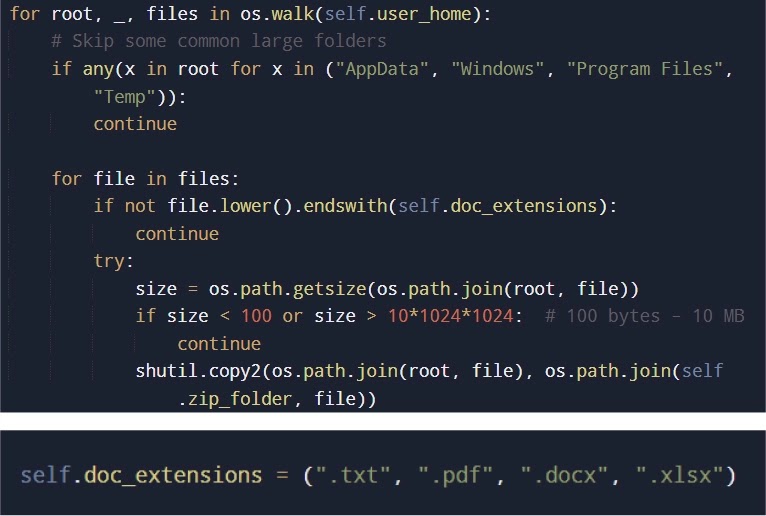
The malware also harvests documents by scanning the user’s home directory for files with specific extensions like .pdf, .docx, and .xlsx, filtering results by file size to avoid network overhead.
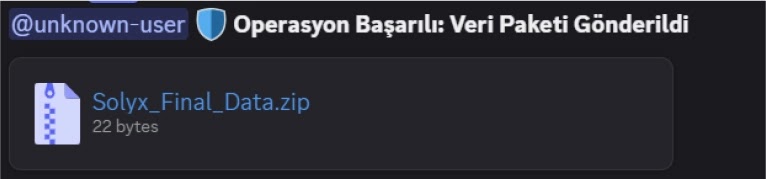
All stolen artifacts are compressed into a ZIP archive and transmitted to attacker-controlled Discord webhooks, completing the data theft cycle.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.