Google Ads Used to Weaponize PDF Editor with Tampered
A potent malvertising campaign, first identified in September 2025, now poses a significant global threat. This operation specifically targets Windows users worldwide. Attackers created fake PDF...
A potent malvertising campaign, first identified in September 2025, now poses a significant global threat. This operation specifically targets Windows users worldwide.
Attackers created fake PDF editing applications and promoted them through Google Ads to distribute a dangerous information-stealing malware called TamperedChef.
The malware targets users searching for appliance manuals and PDF editing tools online, exploiting common search behaviors to deliver silent infections across multiple industries and regions.
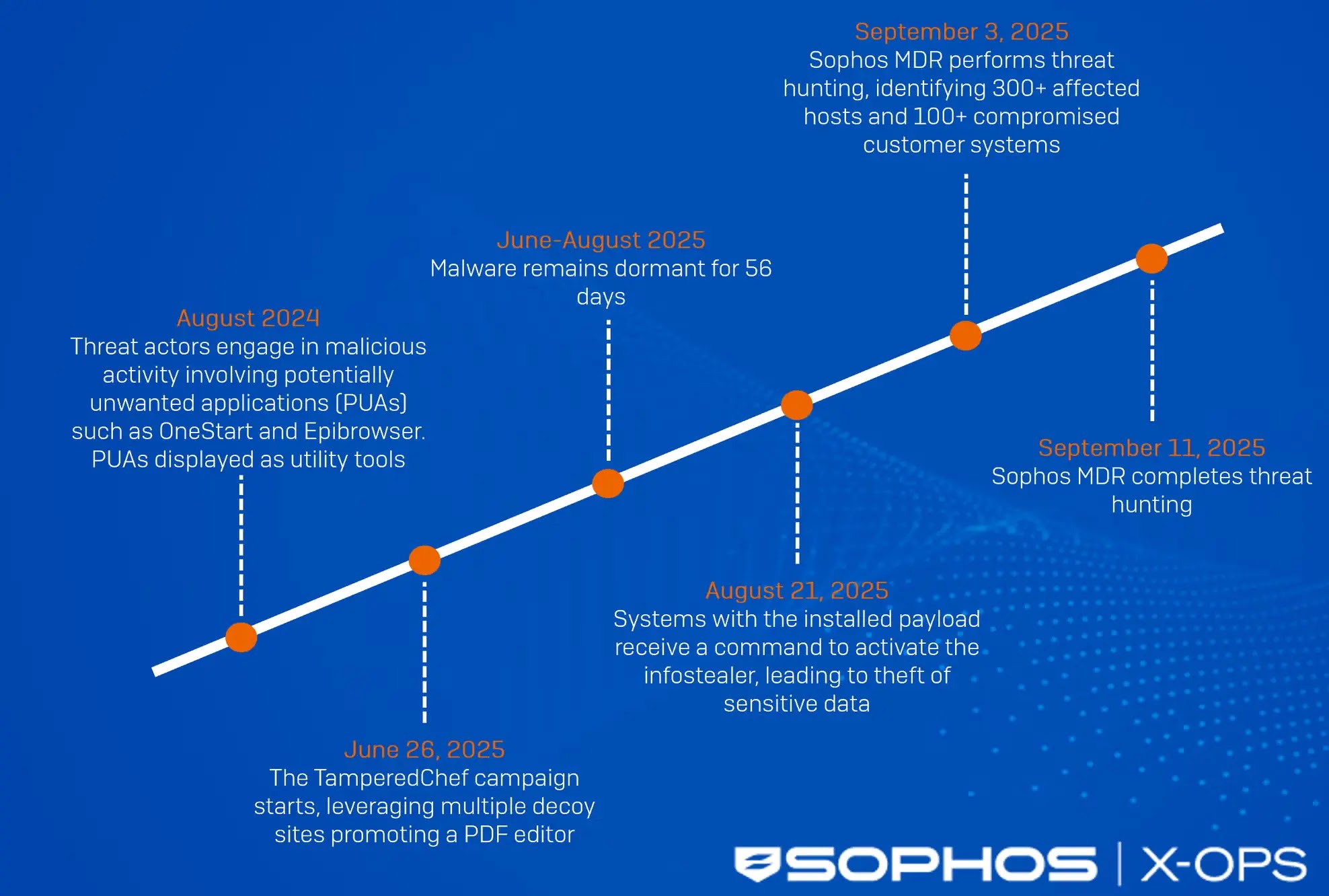
The campaign began officially on June 26, 2025, when threat actors registered multiple look-alike websites promoting a trojanized application named AppSuite PDF Editor.
Users believed they were downloading legitimate software, but the installer actually contained hidden malicious code designed to steal sensitive browser data.
What makes this attack particularly deceptive is its timing—the malware remained dormant for approximately 56 days, matching typical advertising campaign cycles.
This strategic delay allowed the malware to infect as many devices as possible before displaying harmful behavior.
Sophos analysts and researchers identified the malware after discovering over 100 affected customer systems during their managed detection and response operations.
Their investigation revealed that victims primarily came from Germany, the United Kingdom, and France, though the campaign affected at least 19 countries globally.
The attackers targeted industries relying on specialized equipment, where employees frequently search for product manuals online—a behavior the threat actors exploited systematically to spread their malicious installer.
The Silent Infection: How TamperedChef Operates
The infection mechanism of TamperedChef demonstrates sophisticated multi-stage deployment tactics designed to evade detection.
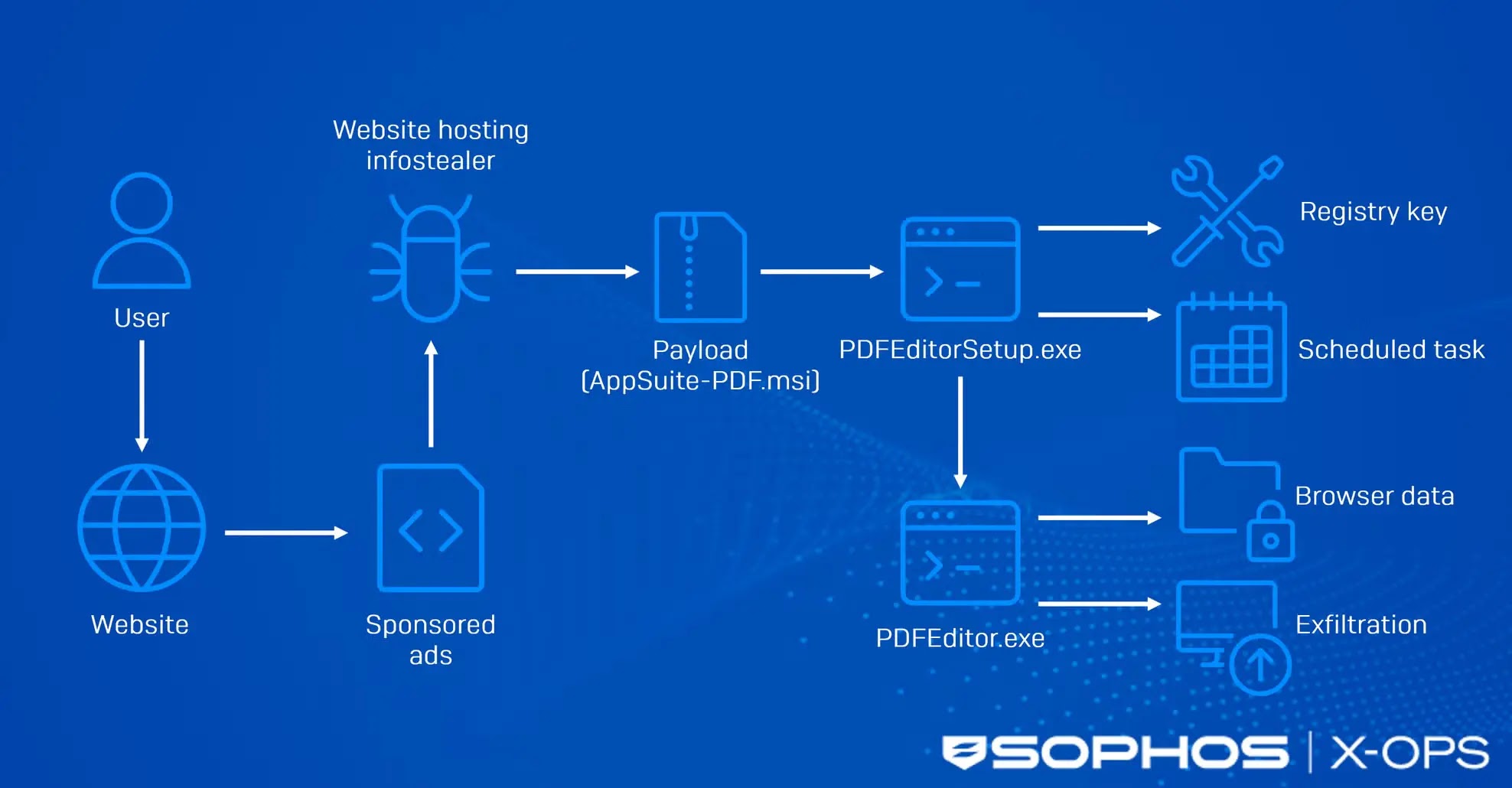
Users begin by clicking malicious advertisements appearing in search results on platforms like Google and Bing.
These ads direct them to deceptive websites such as fullpdf.com and pdftraining.com, where they download the Appsuite-PDF.msi installer.
Once executed, this file drops a setup executable called PDFEditorSetup.exe along with an obfuscated JavaScript file and an additional executable.
PDFEditorSetup.exe then silently establishes persistence by creating registry entries and Windows scheduled tasks, ensuring the malware survives system restarts.
Finally, the installer deploys PDF Editor.exe, the actual infostealer component, which awakened on August 21, 2025, to begin harvesting browser credentials, cookies, and autofill data.
The attackers further enhanced their operation by abusing legitimate code-signing certificates from Malaysian and US-registered entities, enabling their malicious files to bypass Windows SmartScreen protections and appear trustworthy to unsuspecting users.
This layered infection process showcases how modern threat actors combine malvertising, legitimate-looking software interfaces, and system-level evasion techniques to maximize infection success and minimize early detection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.