VoidStealer Bypasses Chrome ABE Without Injection Variant Privilege
Security researchers are closely tracking a new variant of the VoidStealer infostealer. This malware is the first known to bypass Google Chrome’s Application-Bound Encryption (ABE) without requiring...
Security researchers are closely tracking a new variant of the VoidStealer infostealer. This malware is the first known to bypass Google Chrome’s Application-Bound Encryption (ABE) without requiring code injection or elevated system privileges.
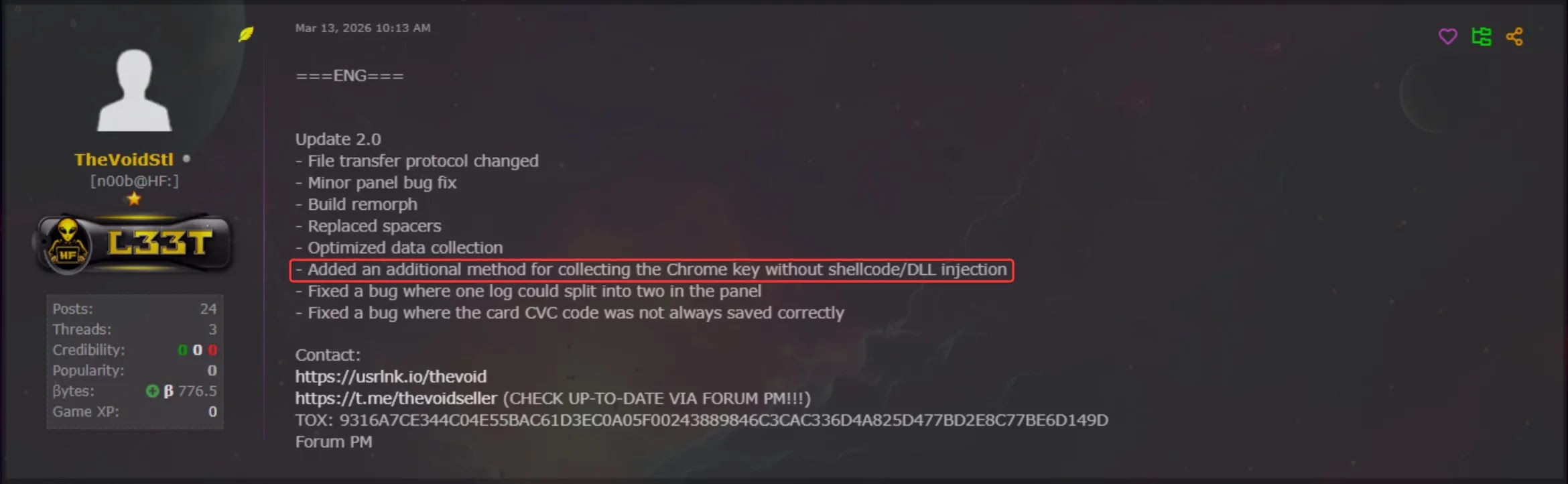
The variant, introduced in VoidStealer version 2.0 on March 13, 2026, uses a debugger-based technique to silently extract encrypted browser credentials directly from memory, marking a meaningful shift in how infostealers approach credential theft.
Google introduced ABE in July 2024 with Chrome 127, aiming to make it considerably harder for malware to access sensitive browser data such as saved passwords and cookies.
The protection works by tying the encryption key — known as the v20_master_key — to a SYSTEM-level service called the Google Chrome Elevation Service, which runs with the highest privileges on Windows.
While this raised the bar significantly, it did not stop threat actors from finding smarter ways around it. Since ABE’s rollout, various bypass techniques have emerged, each carrying different trade-offs between stealth and reliability.
GenDigital analysts identified VoidStealer as a Malware-as-a-Service (MaaS) infostealer that first appeared on darkweb forums, including HackForums, in mid-December 2025.
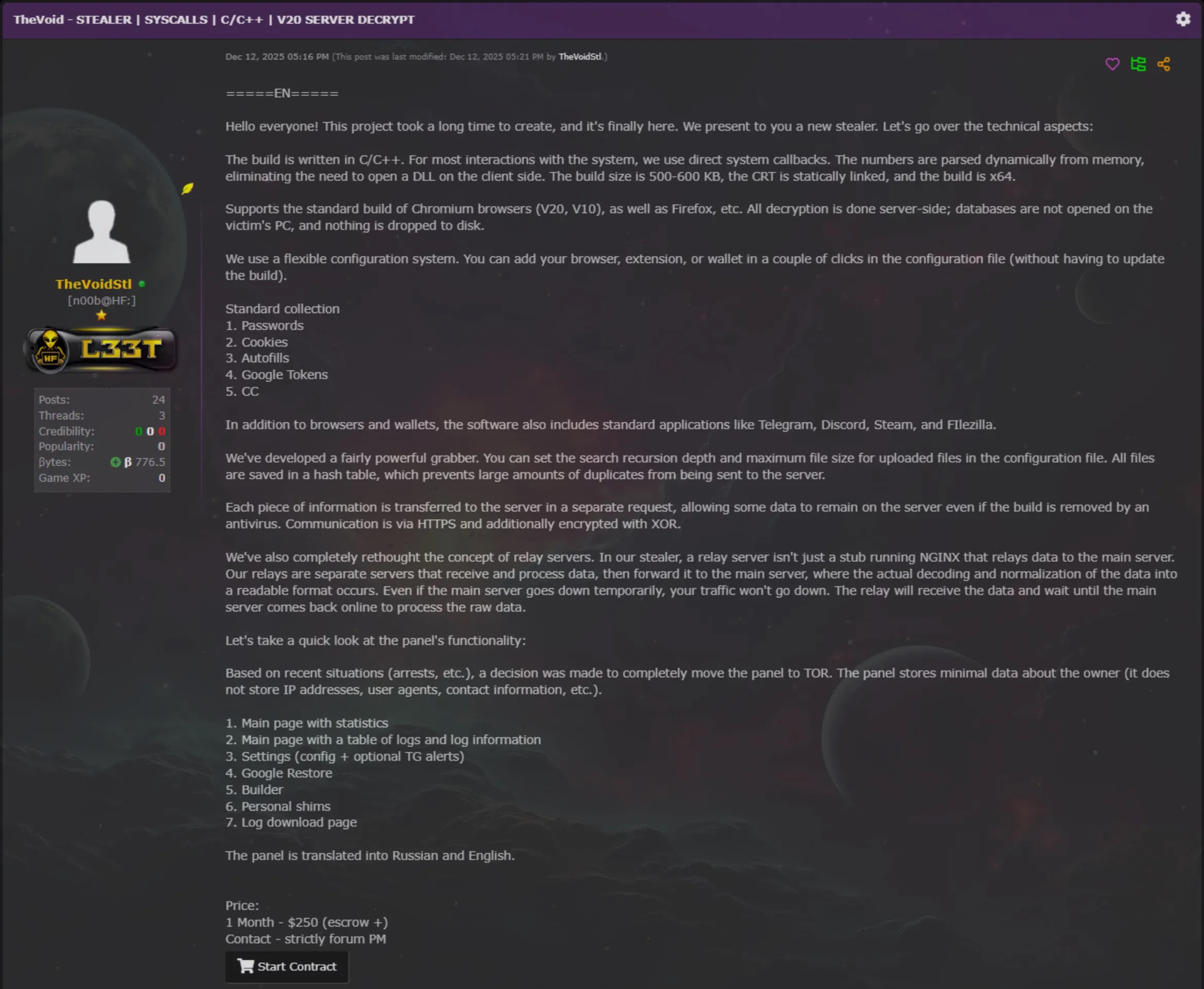
The malware evolved rapidly, advancing from version 1.0 to version 2.1 in just over three months.
While earlier versions relied on a known injection-based bypass, version 2.0 introduced a novel approach adapted from the open-source ElevationKatz project, making VoidStealer the first infostealer spotted in the wild using this technique.
The real danger of this variant lies in its unusually low detection footprint. Most existing ABE bypass techniques either require SYSTEM-level privileges or inject code directly into the browser — actions that security tools can more easily catch.
VoidStealer’s newer method avoids both, relying instead on standard Windows debugging APIs that attract far less attention in typical environments. This makes it harder to detect, and the malware’s rapid update cycle suggests active, ongoing development.
VoidStealer currently targets both Google Chrome and Microsoft Edge. With the technique now publicly available through ElevationKatz, researchers expect other infostealers to follow suit in the near future.
Debugger-Based ABE Bypass Mechanism
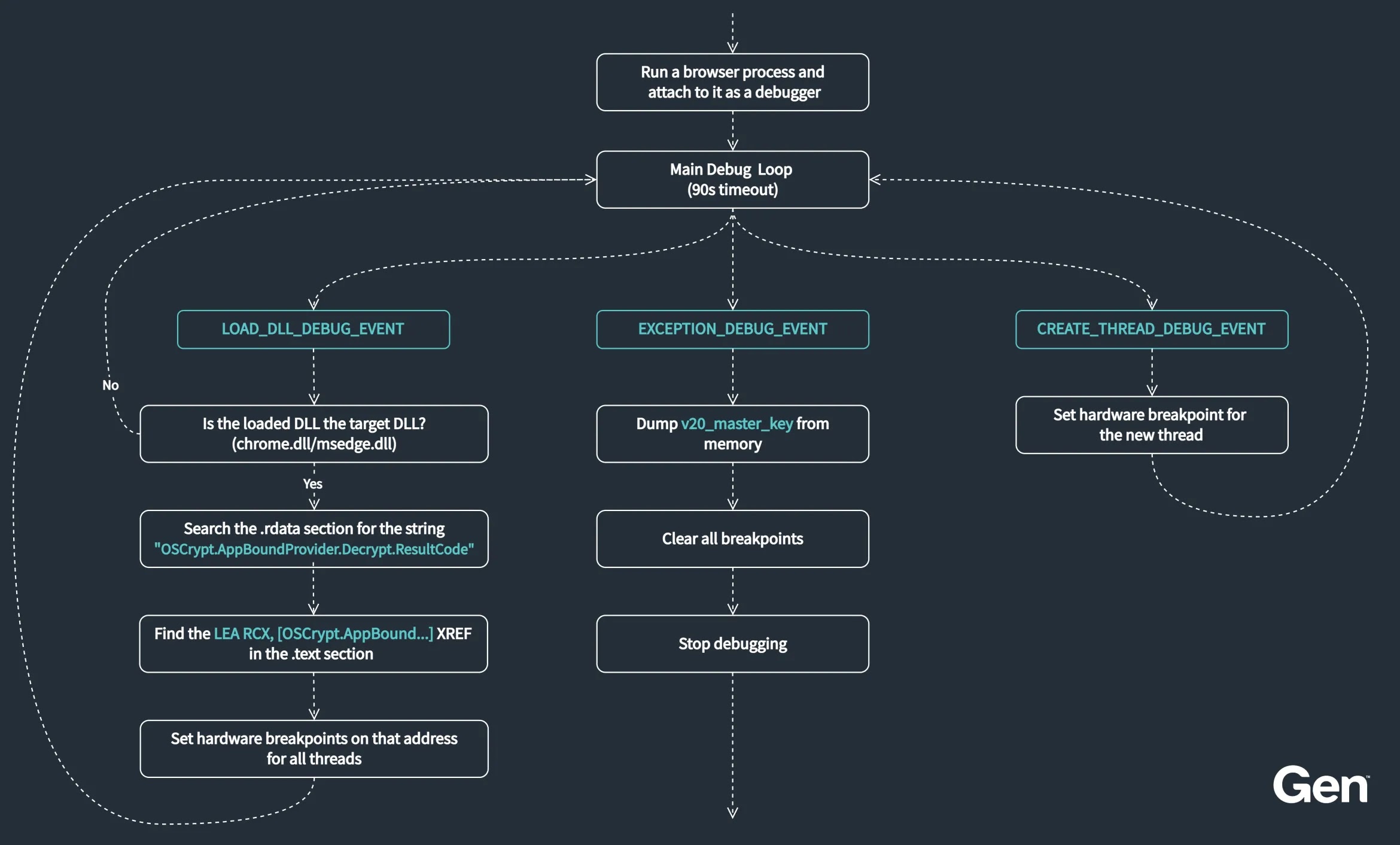
The core of VoidStealer’s novel bypass involves attaching itself to the Chrome or Edge browser as a debugger and setting hardware breakpoints at the exact moment when the v20_master_key is briefly present in memory as plaintext.
VoidStealer begins by spawning a browser process using CreateProcessW with SW_HIDE and CREATE_SUSPENDED flags, then immediately resumes and attaches a debugger via DebugActiveProcess.
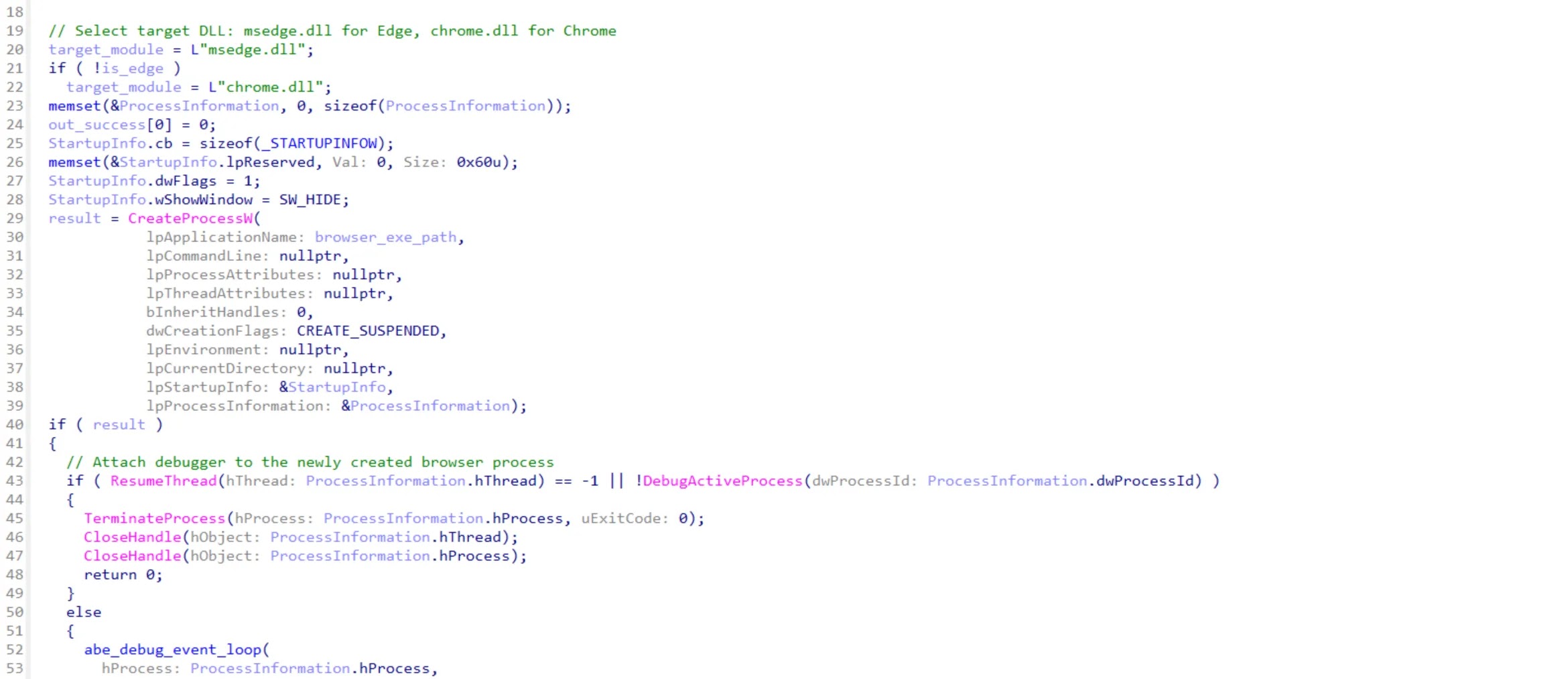
It then listens for debug events through WaitForDebugEvent, monitoring each DLL as it loads into the browser’s memory space.
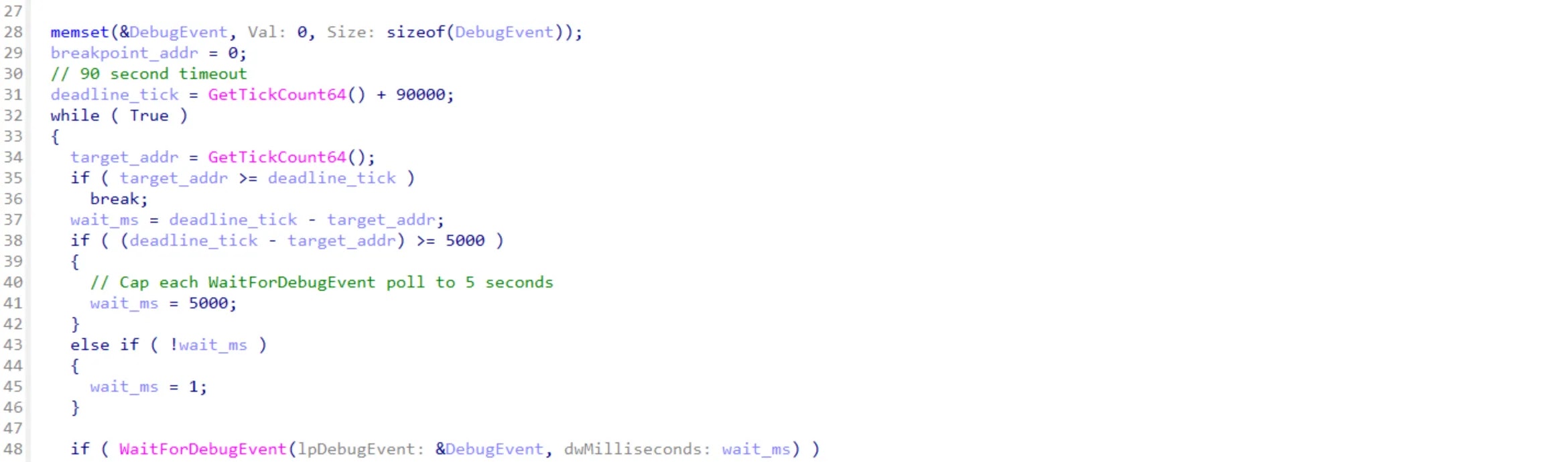
Once chrome.dll or msedge.dll loads, VoidStealer uses ReadProcessMemory to scan the DLL’s .rdata section for the string OSCrypt.AppBoundProvider.Decrypt.ResultCode — the precise point in Chrome’s code where the v20_master_key briefly appears as plaintext.
It then scans the .text section to locate the matching LEA instruction, which becomes the exact address for the breakpoint.
Hardware breakpoints are placed across all browser threads by writing to the DR0 and DR7 debug registers through SetThreadContext, without ever modifying the browser’s memory.
When the breakpoint triggers, the R15 register for Chrome or R14 register for Edge holds a direct pointer to the v20_master_key, which VoidStealer then extracts using just two ReadProcessMemory calls.
Defenders should treat any process that autonomously attaches a debugger to a browser as a serious red flag, since legitimate applications do not behave this way.
Monitoring for browser memory reads from third-party processes, flagging browsers launched with SW_HIDE or headless flags, and alerting on unexpected DebugActiveProcess calls targeting browsers are all strong detection opportunities.
The known indicator of compromise for VoidStealer v2.0 is: f783fde5cf7930e4b3054393efadd3675b505cbef8e9d7ae58aa35b435adeea4.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.