Perseus Android Malware Steals Notes & Enables Device
Perseus, a new Android banking trojan, has emerged in the wild, marking a concerning progression in mobile malware capabilities. This sophisticated threat represents the next step in the ongoing...
Perseus, a new Android banking trojan, has emerged in the wild, marking a concerning progression in mobile malware capabilities. This sophisticated threat represents the next step in the ongoing evolution of such malicious software, as detailed in a recent
The malware spreads through campaigns targeting users primarily in Turkey and Italy, though its reach extends to Poland, Germany, France, the UAE, Portugal, and cryptocurrency platforms.
Threat actors distribute it through fake IPTV applications, a tactic that sidesteps the Google Play Store by exploiting users’ familiarity with sideloading APK files.
Disguised as a legitimate streaming service, Perseus lowers user suspicion and improves infection rates. A dropper application is also used to bypass Android 13+ installation restrictions, making the infection process significantly harder to detect.
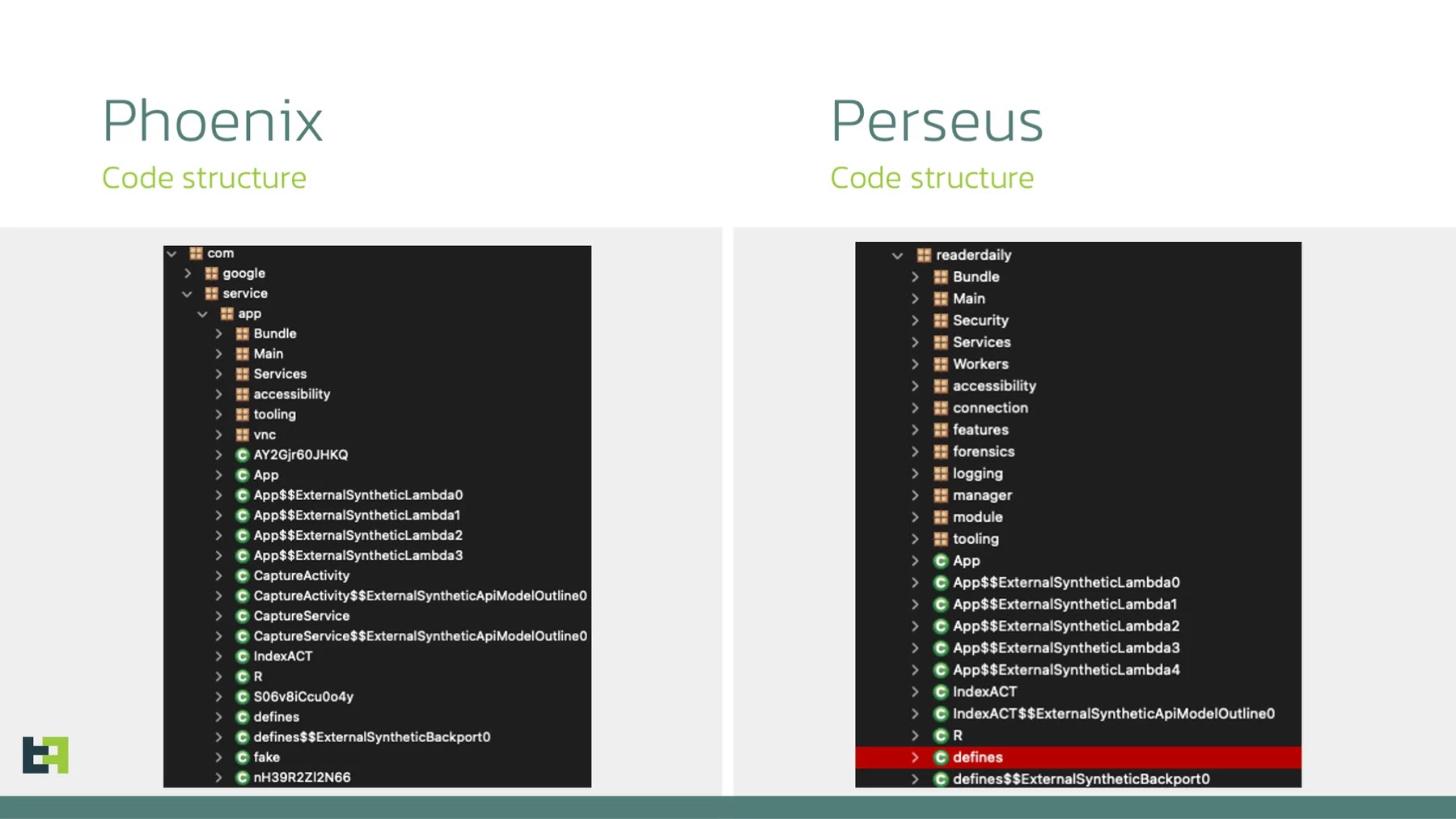
ThreatFabric analysts identified the malware as part of an active campaign and noted its connections to infrastructure shared with other known families, including Medusa and Klopatra.
The malware’s name was taken directly from the C2 login panel observed during several campaign analyses, confirming it as a deliberate and purpose-built threat.
Analysts also identified two main branches: one written in English with extensive debugging features, and a more discreet Turkish-language version, both actively targeting financial institutions and user data across multiple regions.
Once installed, Perseus requests Accessibility Service permissions, which become the backbone of its operation. These permissions allow it to monitor the screen, intercept user input, and simulate touch interactions without showing any visible signs of activity.
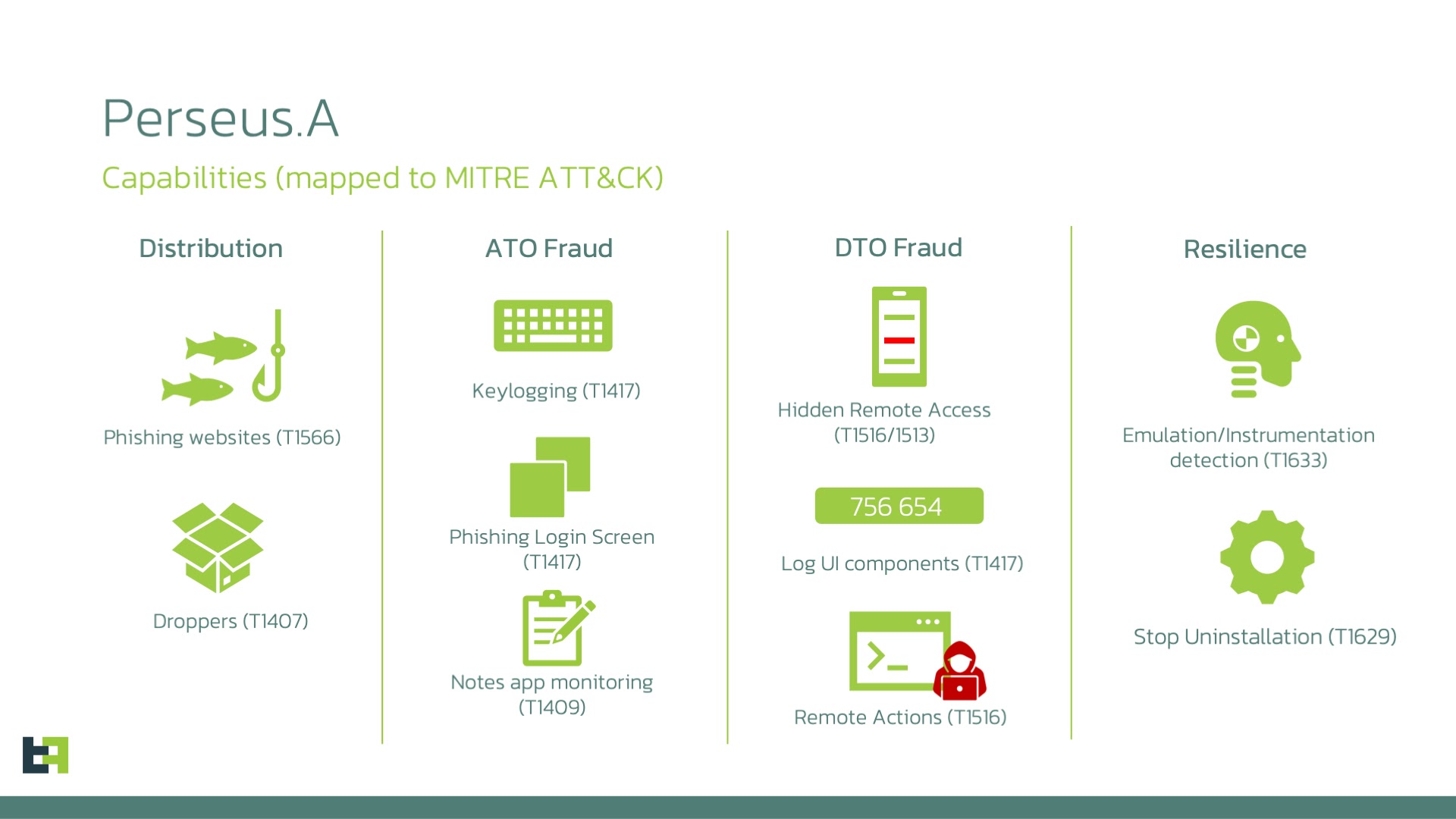
The malware launches overlay attacks by displaying fake login pages over legitimate banking applications, while its keylogging capability records everything a user types.
When combined with its remote control features, this gives an attacker full interactive control over the compromised device, allowing them to conduct fraud and authorize transactions without the victim’s knowledge.
The wider impact of Perseus is difficult to underestimate. Targeting more than 50 institutions across eight countries and nine cryptocurrency platforms, it presents a serious financial threat.
Its ability to perform full Device Takeover while staying hidden demonstrates how far modern Android banking malware has advanced.
Taking Notes: A Capability Others Lack
What separates Perseus from most Android banking trojans is its ability to target note-taking applications on the victim’s device.
Many people store passwords, cryptocurrency recovery phrases, and financial account details in note apps, often without realizing the risk.
Perseus exploits this through a command called scan_notes, which identifies installed note applications and silently opens each one to read through its stored content, all without any user interaction.
Perseus executes this process using Android Accessibility Services to navigate each application’s interface autonomously.
It moves through individual notes, triggers tap actions to open entries, captures the text, then performs a back-navigation action before moving to the next.
The entire routine runs silently in the background with no visible indication for the victim. All captured note data is logged and forwarded to the attacker’s command-and-control server alongside other stolen credentials and device information.
The applications monitored by Perseus include Google Keep, Xiaomi Notes, Samsung Notes, ColorNote, Evernote, Microsoft OneNote, Simple Notes Pro, and Simple Notes.
This broad targeting reflects a calculated effort to extract high-value personal and financial data that victims typically assume is safe on their own devices.
Users should avoid installing applications from outside official app stores and ensure Google Play Protect remains enabled. Keeping Android devices updated with the latest security patches is a critical step in reducing exposure to threats like Perseus.
Most importantly, users should never store passwords, wallet recovery phrases, or sensitive credentials inside note-taking applications, since malware abusing Accessibility Services can access that data without ever alerting the device owner.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.