Sophisticated Phishing Attack Impersonates Google Support to
Cybersecurity researchers have uncovered a dangerous new phishing campaign. The operation tricks users into surrendering credentials by impersonating legitimate Google support and notifications. The...
Cybersecurity researchers have uncovered a dangerous new phishing campaign. The operation tricks users into surrendering credentials by impersonating legitimate Google support and notifications.
The attack combines vishing (voice phishing), spoofed domains, and Google’s own trusted infrastructure to achieve exceptional success rates against organizations worldwide.
The attack employs a multi-layered social engineering approach. Threat actors initiate contact by phone, using voice-spoofing technology to mimic Google support representatives.
These calls reference suspicious account activity or security concerns, building urgency and trust.
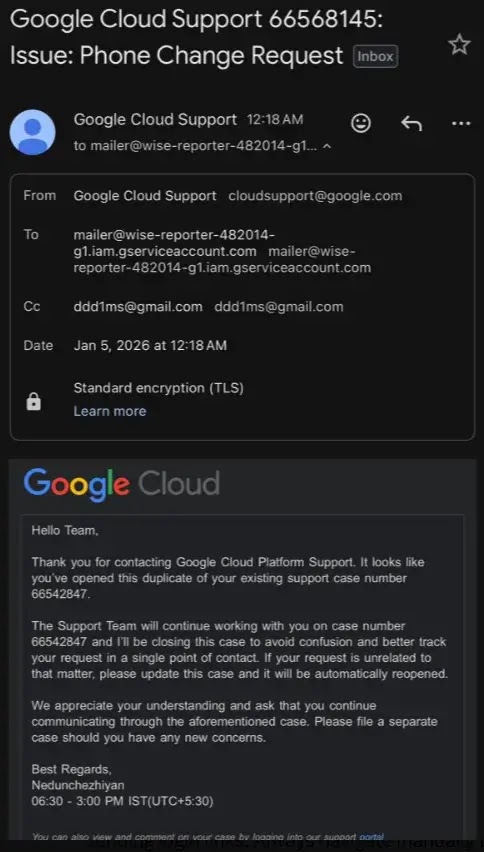
Google Support-Based Phishing Campaign
The attacker then directs victims to click links in follow-up emails that appear to originate from legitimate Google addresses, bypassing traditional email authentication checks like SPF, DKIM, and DMARC.
What makes this campaign particularly insidious is its abuse of Google’s own cloud infrastructure.
Rather than creating fake domains that might trigger security filters, attackers leverage Google Cloud Application Integration services to send phishing emails directly from legitimate Google infrastructure.
In December 2025 alone, researchers documented over 9,000 phishing emails targeting approximately 3,200 businesses across the United States, Europe, Asia-Pacific, Canada, and Latin America.
The attack flow follows a sophisticated redirection chain. When victims click embedded links, they land on pages hosted on trusted Google Cloud Storage domains, making URL reputation filters ineffective.
These pages display fake CAPTCHA verification screens that block automated security scanning while allowing human users through, as reported by Dmitrn Gmilnanets.
After verification, victims are redirected to credential-harvesting pages that mimic Google login screens or Microsoft 365 interfaces, where their usernames and passwords are stolen.
Security experts emphasize that cloud providers never initiate contact to request login credentials or direct users to external verification pages.
Users should always navigate directly to official service portals they already use rather than clicking links in unsolicited communications.
Organizations should implement multi-factor authentication (MFA), enforce the use of a password manager, restrict login locations by IP range, and provide regular security awareness training.
Additionally, security teams must move beyond traditional domain-reputation defenses and implement behavioral analysis and contextual threat detection to identify legitimate infrastructure that is being weaponized for malicious purposes.
This campaign underscores a critical shift in phishing tactics: attackers are increasingly abusing legitimate platforms rather than spoofing domains, requiring a fundamental rethink of email security strategies.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.