New Brutus Brute-Force Tool Targets Fortinet Services
A threat actor, identified by the moniker “RedTeam,” is now advertising a New Brutus Brute-Force Tool Targets Fortinet services. The tool is priced at $1,500, signaling growing interest in automated...
A threat actor, identified by the moniker “RedTeam,” is now advertising a New Brutus Brute-Force Tool Targets Fortinet services.
The tool is priced at $1,500, signaling growing interest in automated credential-stuffing attacks against enterprise infrastructure.
Brutus is engineered to attack multiple remote access protocols, making it versatile for attackers seeking to compromise diverse systems.
The tool supports SSH, RDP, VNC, and shell-based connections, allowing attackers to target common remote access services deployed in enterprise environments.
This multi-protocol approach significantly increases the attack surface for organizations that rely on Fortinet appliances for network security.
The tool includes a built-in scanner that automatically identifies vulnerable or exposed services, streamlining reconnaissance and target identification.
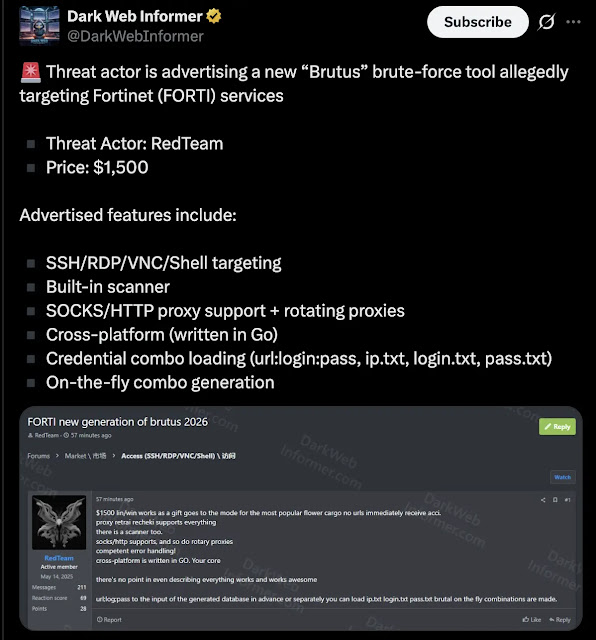
Additionally, Brutus supports SOCKS and HTTP proxying with rotating proxies, allowing attackers to mask their origin and evade network detection systems.
This obfuscation feature is critical for attackers seeking to avoid triggering security alerts or IP-based blocking measures. Developed in Go, Brutus is cross-platform compatible, enabling deployment on Windows, Linux, and macOS.
This language choice emphasizes performance and ease of compilation, allowing the tool to be rapidly adapted for different environments.
The tool supports flexible credential management, accepting combo lists in multiple formats, including URL:login: password combinations and separate IP, login, and password text files.
Notably, Brutus includes on-the-fly combo generation, enabling attackers to generate credential variations during attacks dynamically.
This feature reduces reliance on pre-compiled credential databases. It enhances the likelihood of successful compromise against systems with common password patterns.
Fortinet products are extensively deployed in enterprise and government networks worldwide. According to recent dark web intelligence observation, a specialized brute-force tool targeting these systems poses a significant risk, particularly for organizations with weak authentication policies or outdated Fortinet appliances.
The $1,500 price point suggests it is accessible to relatively well-funded threat actors or organized cybercriminal groups.
Security teams managing Fortinet infrastructure should prioritize implementing strong authentication mechanisms, including multi-factor authentication where possible.
Organizations should also conduct regular security assessments to identify exposed services and enforce strict access controls.
Monitoring for unusual login attempts and implementing rate limiting on authentication endpoints remain critical defensive measures against brute-force attacks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.