Attackers Abuse AppSheet, Netlify, Telegram for Google Facebook
A sophisticated cybercriminal operation, dubbed “AccountDumpling,” has compromised approximately 30,000 Facebook accounts worldwide. This extensive breach leveraged the abuse of...
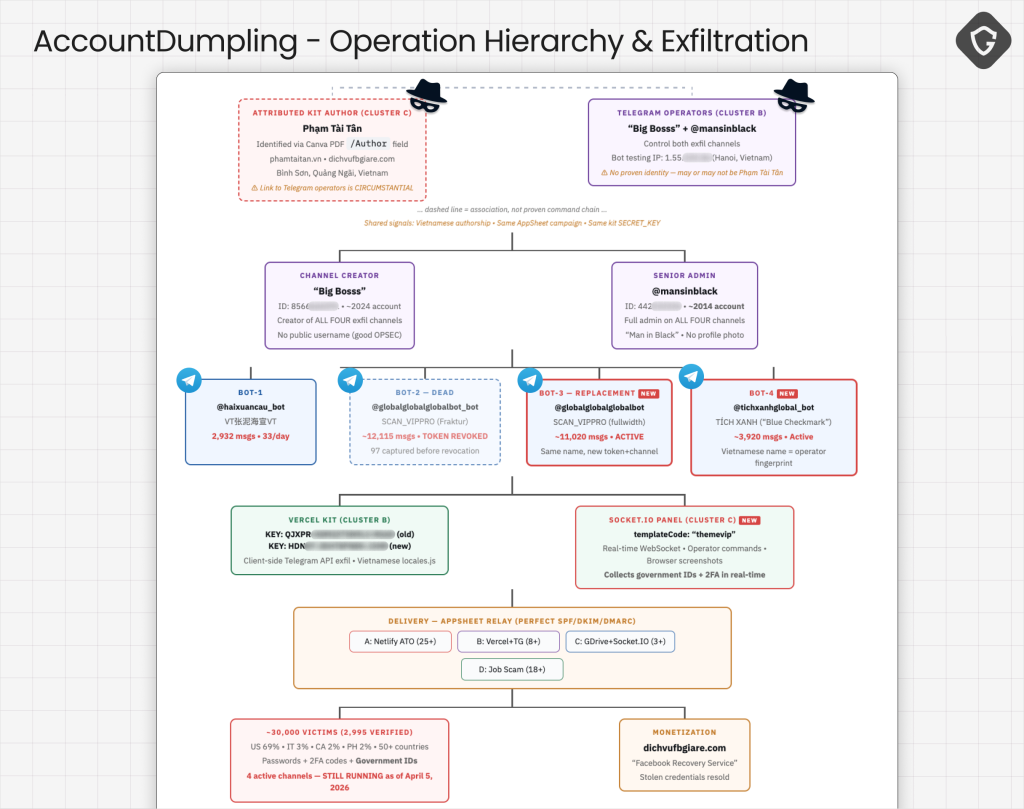
A sophisticated cybercriminal operation, dubbed “AccountDumpling,” has compromised approximately 30,000 Facebook accounts worldwide. This extensive breach leveraged the abuse of legitimate services, specifically Google AppSheet, Netlify, and Telegram, to facilitate widespread credential theft. Attackers exploited Discovered by Guardio Labs, this Vietnamese-linked campaign abuses Google’s AppSheet platform to bypass traditional email security filters.
By routing fully authenticated phishing lures through legitimate channels, the attackers successfully harvest credentials and identity documents. These stolen Facebook Business accounts are subsequently monetized or resold back to victims through an illicit storefront.
The foundation of this campaign relies on hijacking platform trust rather than spoofing domains. The threat actors use Google AppSheet, a legitimate no-code app-building service, to distribute malicious notifications.
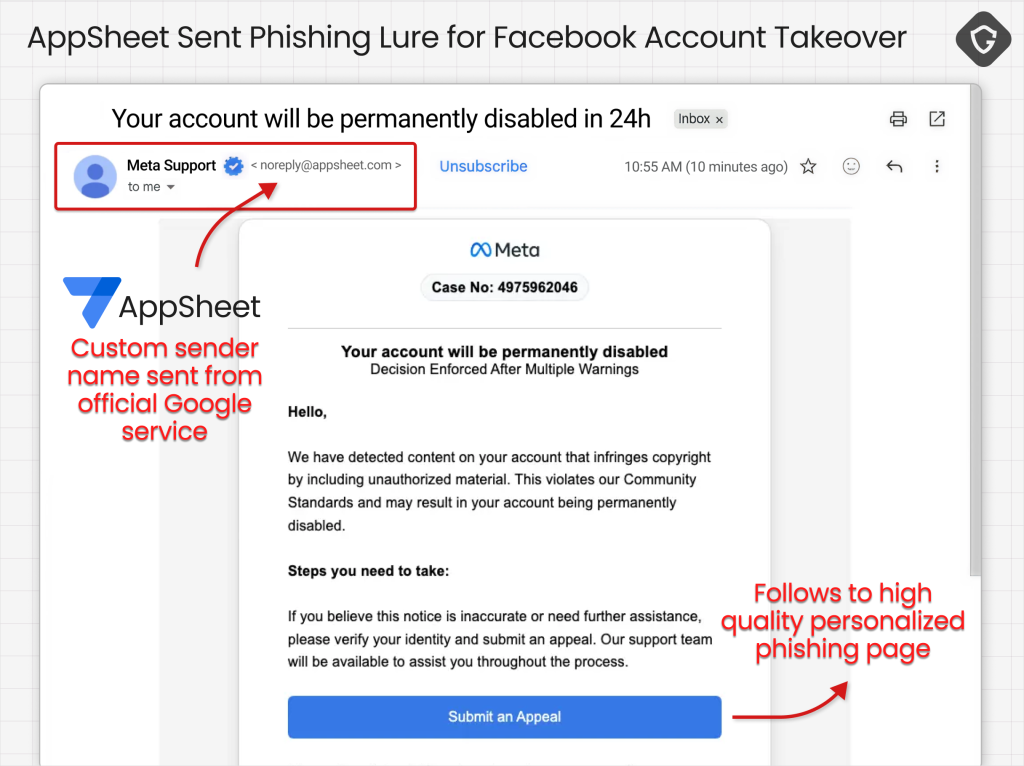
Because these emails are sent directly from Google servers using the address [email protected], they easily pass SPF, DKIM, and DMARC authentication checks.
Security defenders and spam filters consistently wave these messages through since Google genuinely owns the sending infrastructure. This forces victims to rely entirely on identifying the deceptive content within the message itself.
Attack and Evasion Methodologies
The operation is highly modular, employing four distinct phishing clusters to target victims based on different psychological triggers.
Behind the sophisticated front-end lures, the AccountDumpling operation relies entirely on Telegram bots for its command-and-control exfiltration.
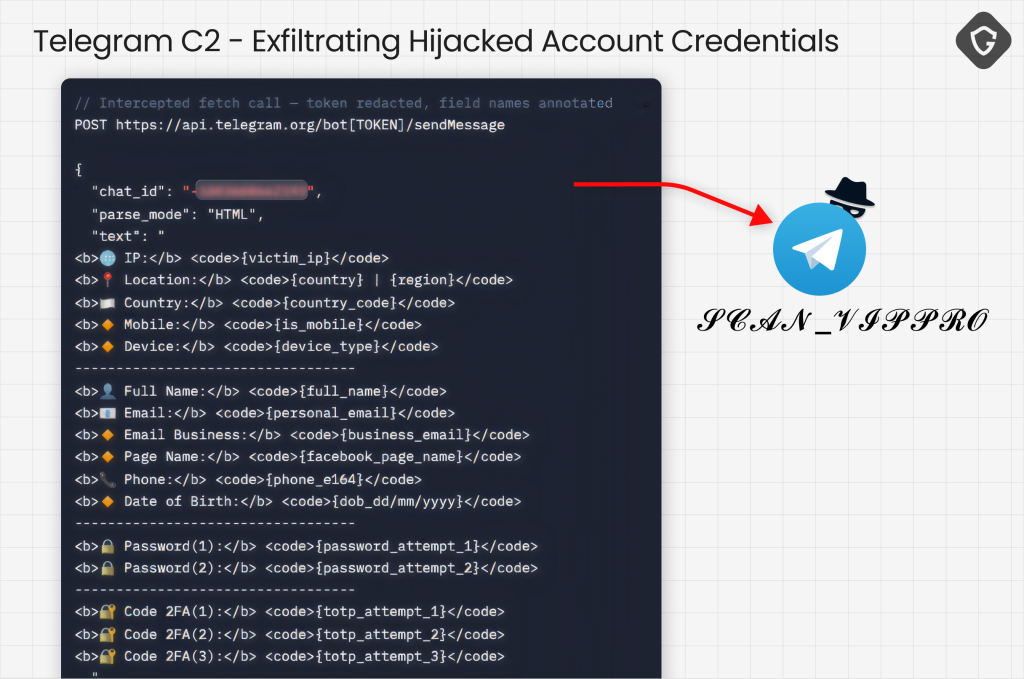
Stolen credentials, two-factor authentication codes, dates of birth, and government-issued ID photos are instantly routed to private Telegram channels.
Operators actively monitor these streams to validate the stolen data and execute account takeovers in real time. Telemetry from the recovered bot infrastructure indicates roughly 30,000 victim records have been processed.
Geographic analysis reveals that 68.6 percent of the targeted individuals and businesses are located in the United States.
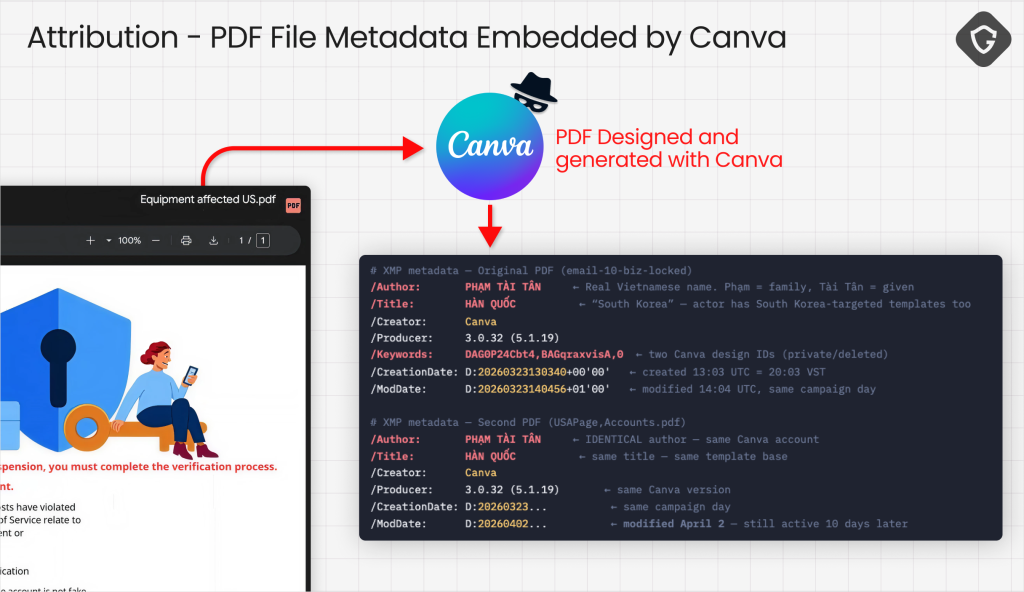
Guardio Labs successfully traced the core of the operation to a Vietnamese threat actor through a critical operational security failure.
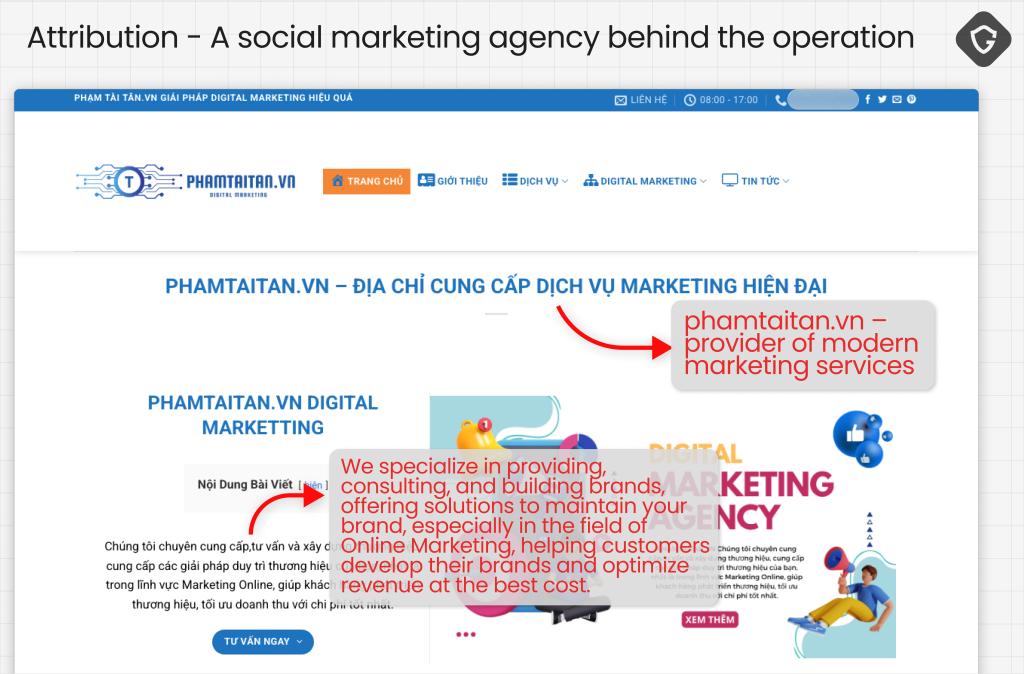
A Canva-generated PDF used in the third attack cluster retained its author metadata, exposing the real name “PHẠM TÀI TÂN”. Investigators connected this name to a public business persona in Vietnam that actively advertises Facebook account recovery and security services.
This reveals a circular criminal economy in which attackers steal valuable business assets, use them to run fraudulent campaigns, and then attempt to sell recovery services back to the original victims.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.