ClickFix Attack: Fake Windows BSOD Tricks Uses Screens
PHALTBLYX, a sophisticated malware campaign, has emerged, leveraging social engineering deception and advanced evasion techniques to compromise organizations within the hospitality sector. The attack...
PHALTBLYX, a sophisticated malware campaign, has emerged, leveraging social engineering deception and advanced evasion techniques to compromise organizations within the hospitality sector.
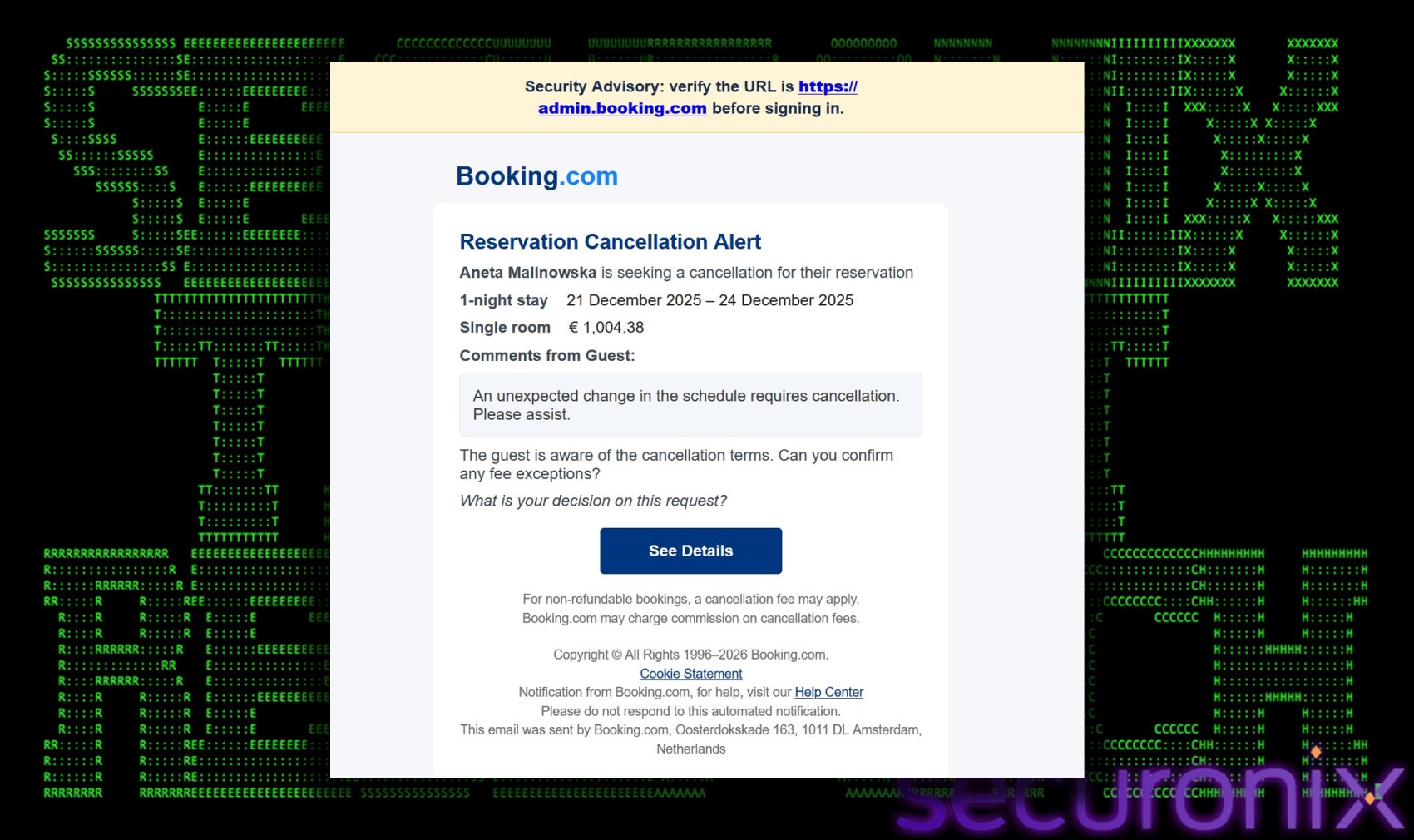
The attack chain begins with phishing emails impersonating Booking.com, featuring urgent reservation cancellation alerts with large financial charges displayed in euros.
These messages direct victims to fake Booking.com websites that appear visually identical to the legitimate service, exploiting user anxiety about fraudulent transactions.
The attack progresses through a carefully orchestrated series of stages designed to bypass traditional security controls. Once victims click the refresh button on the fake page, their browser displays a full-screen blue screen of death animation.
This simulated crash prompts users to follow on-screen instructions that involve pressing specific keyboard combinations.
Securonix analysts identified that the malware silently copies a PowerShell command to the clipboard, which victims unknowingly execute when following the displayed instructions.
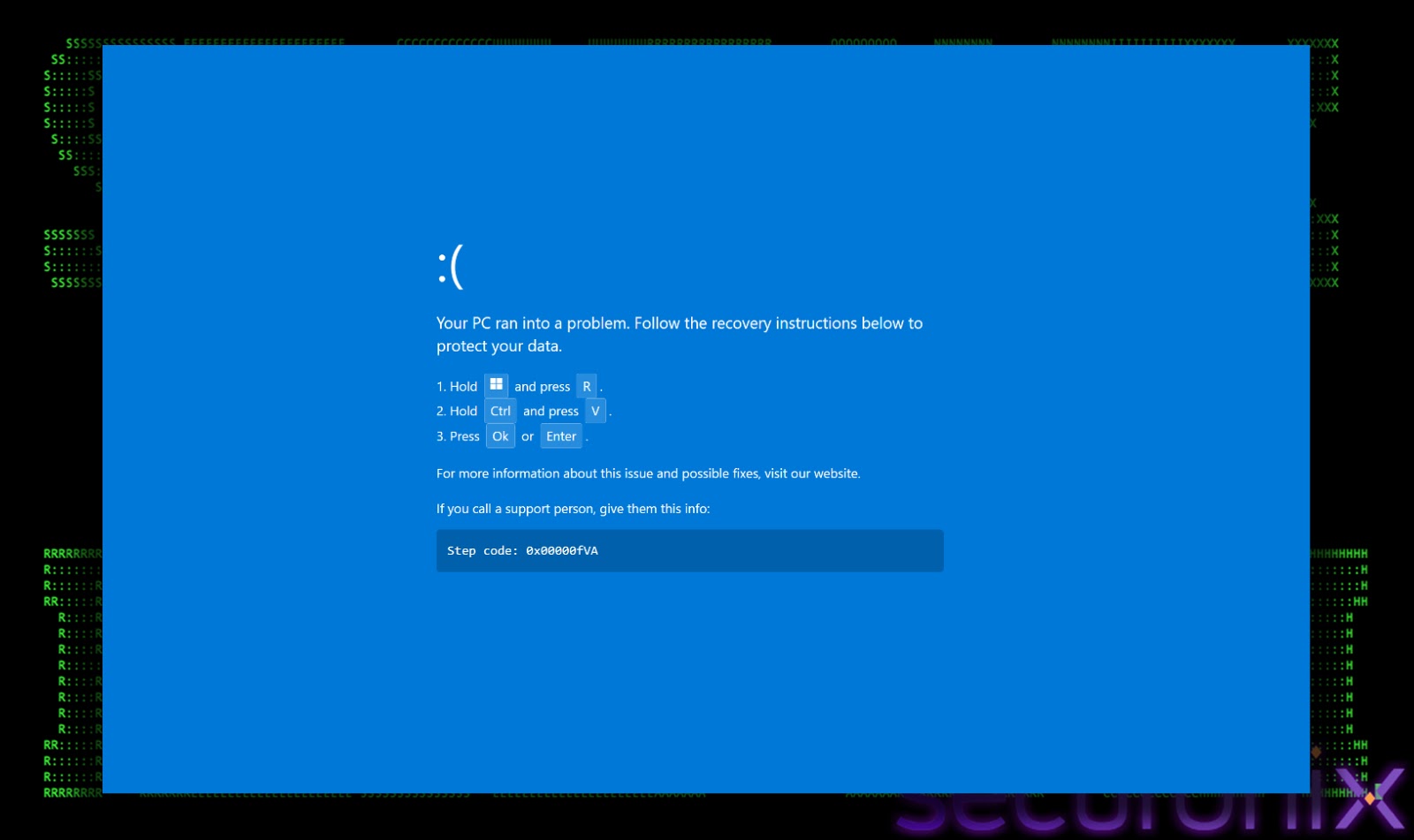
Securonix researchers noted that this click-fix social engineering method represents a critical evolution in the attack’s delivery mechanism.
The technique relies on manual user execution rather than automated processes, effectively circumventing security controls that would block script execution.
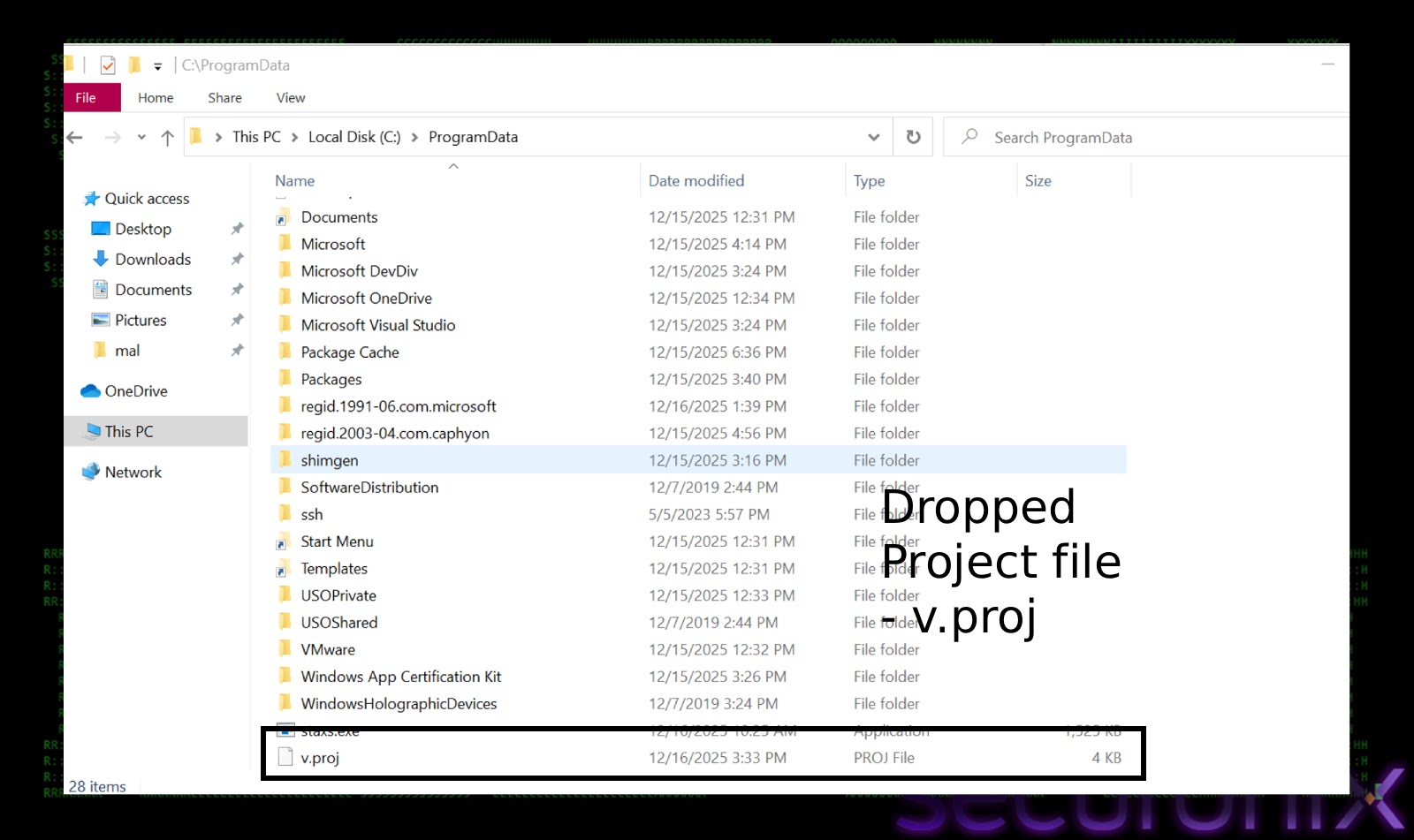
The malicious PowerShell command performs several functions, including opening the legitimate Booking.com admin page as a distraction while downloading an MSBuild project file from remote servers.
Infection mechanism
The infection mechanism leverages Microsoft’s legitimate MSBuild.exe compiler to execute the downloaded v.proj file, a technique known as living off the land.
This approach allows malware to proxy execution through trusted Windows utilities, often bypassing application whitelisting and antivirus detection.
Once executed, the malware disables Windows Defender by adding broad file extension exclusions and specific directory exclusions, ensuring subsequent payloads remain undetected.
The final payload is a customized variant of DCRat, a remote access trojan capable of extensive system compromise. The RAT establishes persistence using internet shortcut files placed in the Windows startup folder, disguised as legitimate system utilities.
Upon connection to command and control servers, the malware collects comprehensive system information including hardware identification, operating system details, installed antivirus software, and active window titles.
The malware’s capabilities include keylogging, process injection into legitimate system binaries like aspnetcompiler.exe, and downloading additional malicious payloads.
The presence of Cyrillic language artifacts and Russian debugging strings strongly indicates Russian-speaking threat actors. Organizations should implement rigorous user awareness training regarding click-fix tactics and monitor suspicious MSBuild.exe executions originating from non-standard directories to detect and prevent similar attacks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.