RondoDoX Botnet Exploits Critical React2Shell Vulnerability
Exploits Critical React2Shell Vulnerability
Alright, so there’s this pretty sophisticated threat group we’ve been tracking. And lately, they’ve really kicked their campaign against organizations into high gear. How? By exploiting all the newest vulnerabilities out there. That means weaknesses in web applications and, yep, even those Internet of Things (IoT) devices.
The RondoDoX botnet, tracked through exposed command-and-control logs spanning nine months from March to December 2025, demonstrates a relentless approach to compromising enterprise infrastructure.
The malware operates through a multi-stage infection process that begins with scanning for vulnerable systems and escalates to deploying cryptominers and botnet payloads across diverse network environments.
The campaign reveals three distinct attack phases, each progressively more sophisticated than the last. Initially, threat actors conducted manual vulnerability testing on various platforms.
By April 2025, they shifted to automated daily scanning operations targeting multiple web frameworks.
The final phase, beginning in July 2025, escalated attacks to hourly deployment attempts, showcasing the attackers’ commitment to continuous exploitation and infrastructure compromise.
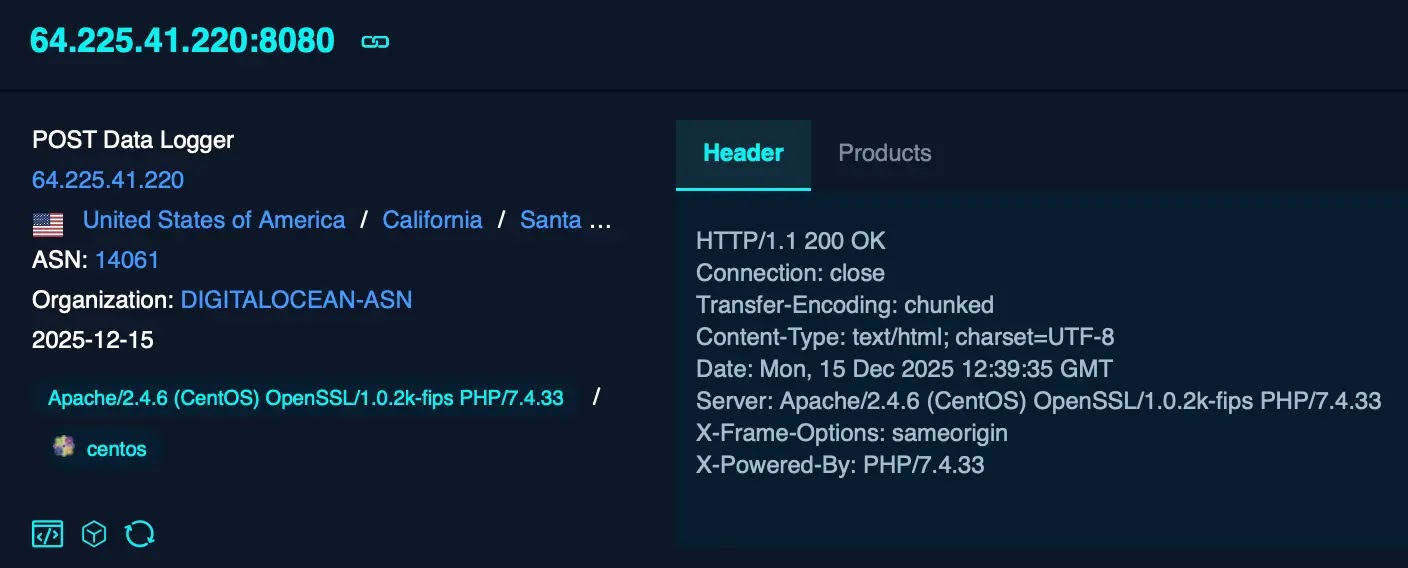
CloudSEK analysts identified the malware through routine scans for malicious infrastructure, uncovering six confirmed command-and-control servers with overlapping operational periods.
The researchers discovered evidence of at least ten botnet variants actively deployed across compromised systems, with command logs revealing detailed attack patterns and infrastructure usage spanning the entire campaign timeline.
The most alarming development emerged in December 2025, when threat actors began weaponizing a critical Next.js vulnerability to deploy React2Shell payloads.
Attack chain
This transition demonstrates the group’s ability to rapidly adapt and adopt newly disclosed security flaws.
The attack chain begins with identification of vulnerable servers through blind remote code execution testing, followed by deployment of ELF binaries that download malicious payloads from active command-and-control infrastructure.
The malware’s infection mechanism reveals sophisticated persistence and evasion capabilities. Once deployed, the botnet establishes persistence through cron job configuration in system files and aggressively terminates competing malware to monopolize system resources.
The payload includes cryptominers and support frameworks designed for long-term dominance on compromised hosts.
The botnet supports multiple processor architectures including x86, x86_64, MIPS, ARM, and PowerPC, with multiple fallback download mechanisms using wget, curl, tftp, and ftp protocols to ensure successful payload delivery across heterogeneous enterprise environments.
Organizations with internet-facing routers, cameras, and applications running Next.js Server Actions face immediate risk.
Network segmentation, immediate patching of vulnerable applications, Web Application Firewall deployment, and continuous monitoring for suspicious process execution in temporary directories remain essential defensive measures.
Additionally, blocking identified command-and-control infrastructure at perimeter firewalls provides critical short-term protection against active exploitation attempts.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.