OysterLoader Evasion Loader: Obfusc Multi‑Stage Uncovered
OysterLoader, a sophisticated malware loader, poses a significant threat across the cybersecurity landscape. It employs multiple layers of obfuscation to evade detection and deliver dangerous...
OysterLoader, a sophisticated malware loader, poses a significant threat across the cybersecurity landscape. It employs multiple layers of obfuscation to evade detection and deliver dangerous payloads.
First identified in June 2024 by Rapid7, this C++ malware is distributed primarily through fake websites that impersonate legitimate software applications such as PuTTy, WinSCP, Google Authenticator, and various AI tools.
The malware masquerades as Microsoft Installer (MSI) files, often digitally signed to appear legitimate, making it particularly deceptive to unsuspecting users.
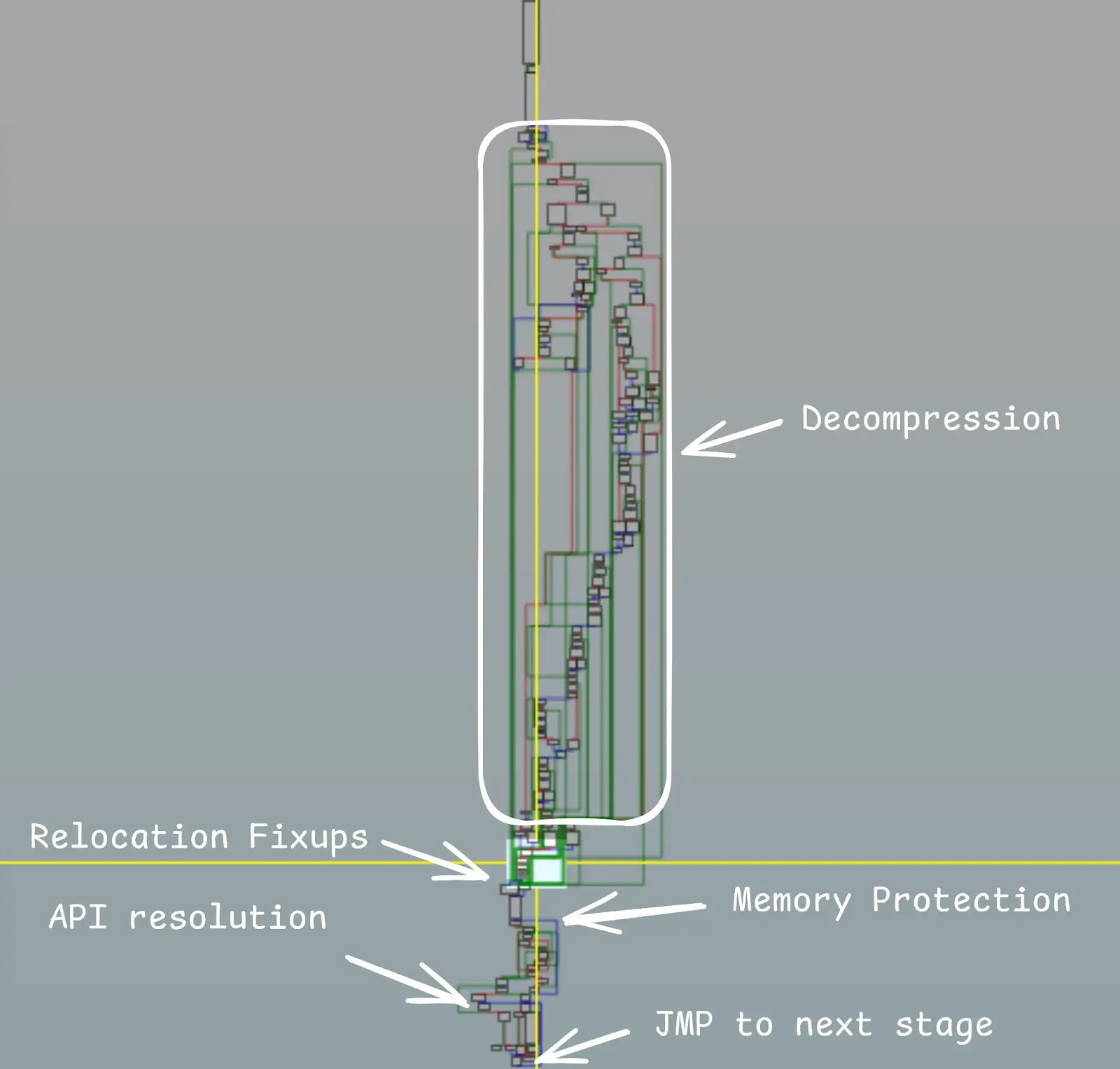
OysterLoader operates through a complex four-stage infection chain that begins with a TextShell packer, progresses through custom shellcode execution, and ultimately delivers the core malicious payload.
The loader has been primarily associated with Rhysida ransomware campaigns, though security researchers have also observed it distributing commodity malware like Vidar, one of the most widespread infostealers as of January 2026.
The connection to the Rhysida ransomware group, which is closely linked to the WIZARD SPIDER threat actor nebula, highlights the severity of this threat.
Sekoia analysts identified that OysterLoader maintains a two-tiered command and control infrastructure, with delivery servers handling initial connections and final C2 servers managing victim interactions.
The malware exhibits advanced anti-analysis capabilities, including API hammering, dynamic API resolution through custom hashing algorithms, and timing-based sandbox detection.
Its developers have continuously evolved the malware’s code, updating communication protocols and obfuscation techniques to maintain effectiveness against security solutions.
Advanced Infection Mechanism and Steganography Techniques
The infection process demonstrates remarkable technical sophistication in how OysterLoader conceals and deploys its malicious components.
After initial environment checks that verify the infected system has at least 60 running processes, the malware establishes communication with command and control servers over HTTPS.
During this phase, it employs steganography to hide the next-stage payload within icon image files, disguising malicious code as legitimate visual content.
The malware uses RC4 encryption with a hardcoded key to protect the embedded payload within these image files.
This payload is hidden after a specific marker pattern labeled “endico,” making detection through conventional security tools extremely challenging.
Once decrypted, the payload is written as a DLL file to the user’s AppData directory and executed through scheduled tasks that run every 13 minutes, ensuring persistent access to compromised systems.
The malware communicates using custom JSON encoding with a non-standard Base64 alphabet and random shift values, making network traffic analysis particularly difficult for security teams monitoring infected environments.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.