New XWorm RAT Campaign Uses Themed Phishing Lures and
A new phishing campaign is delivering an updated variant of XWorm, a Remote Access Trojan (RAT) enabling attackers to gain full remote control of infected Microsoft Windows systems. First tracked in...
A new phishing campaign is delivering an updated variant of XWorm, a Remote Access Trojan (RAT) enabling attackers to gain full remote control of infected Microsoft Windows systems.
First tracked in 2022, XWorm is still actively distributed and is often traded through Telegram-based marketplaces, keeping it within easy reach of many threat actors.
In the latest activity, attackers used multiple business-style email themes—such as payment detail reviews, purchase orders, and signed shipment documents—to trick targets into opening a malicious Excel add-in attachment (.XLAM).
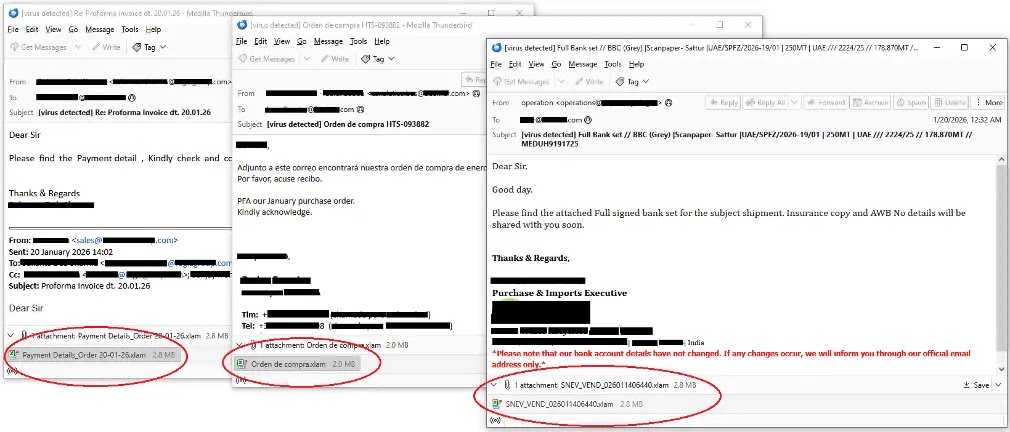
The lure is simple but effective: once the attachment is opened, the attack chain moves quickly from document execution to in-memory malware delivery, raising the risk of account theft, data loss, and hands-on keyboard control.
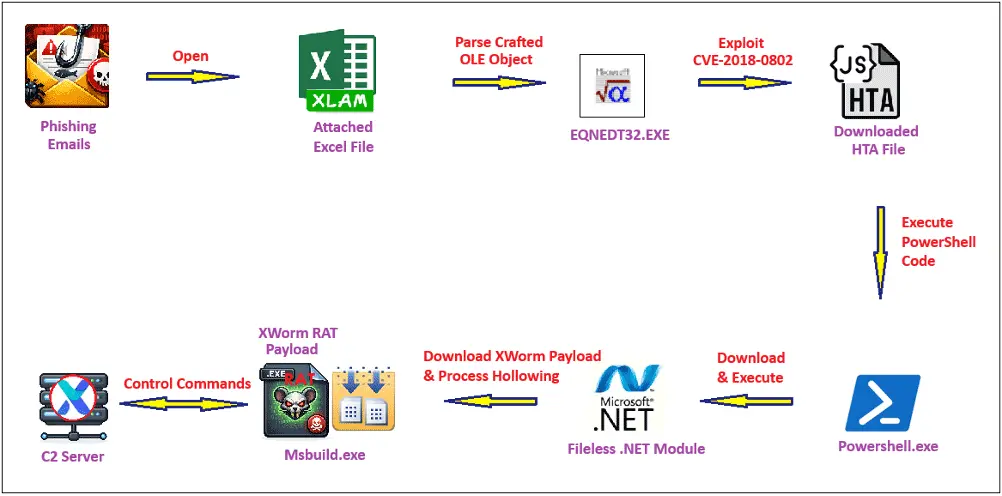
Fortinet researchers identified this campaign after capturing it in the wild, and they documented how a crafted Excel file abuses CVE‑2018‑0802, a Microsoft Equation Editor (EQNEDT32.EXE) remote code execution flaw that remains in real-world use.
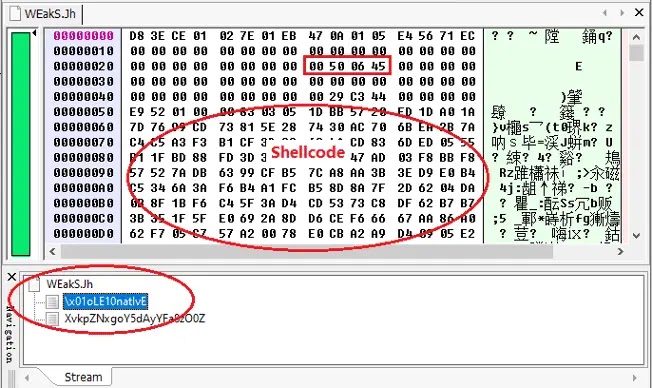
Their analysis shows an embedded OLE object set to auto-load, which leads to shellcode execution when the file is opened.
Infection mechanism
When CVE‑2018‑0802 is triggered, the shellcode downloads an HTA from retrodayaengineering[.]icu/HGG.hta and saves it as %APPDATA%VA5.hta, then launches it via ShellExecuteExW.
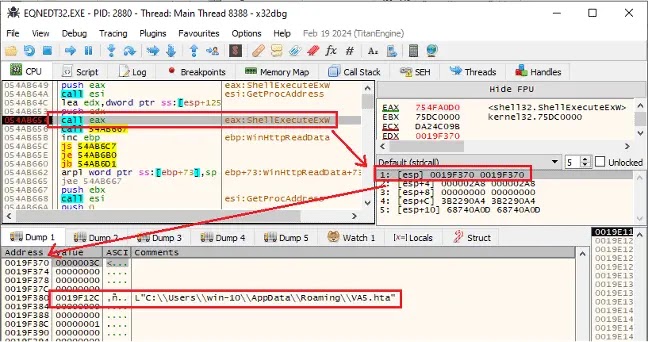
This step shifts the chain from a document exploit to script-based execution, helping the operator blend into normal Windows activity while the payload is staged.
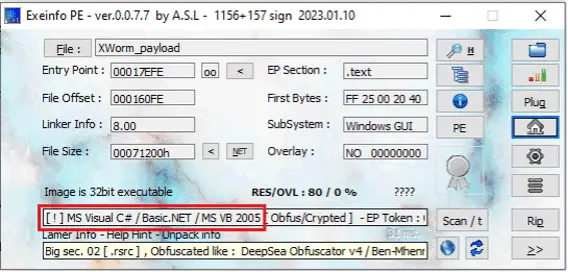
Next, the obfuscated HTA runs under mshta.exe and drops a Base64 PowerShell payload that fetches optimized_MSI_lpsd9p.jpg from a Cloudinary URL and extracts a hidden .NET module placed between “BaseStart” and “-BaseEnd” markers.
The loader module is disguised with the assembly name Microsoft.Win32.TaskScheduler and runs filelessly in memory, avoiding a clean on-disk malware binary in the early stages.
From there, the .NET loader decodes a reversed Base64 URL, pulls wwa.txt from pub-3bc1de741f8149f49bdbafa703067f24[.]r2[.]dev, reconstructs the XWorm payload in memory, and injects it into a newly created Msbuild.exe using process hollowing.
After execution, the RAT decrypts its configuration, connects to berlin101[.]com:6000, and uses AES-encrypted traffic, so defenders should prioritize patching Equation Editor exposure, blocking or isolating .XLAM/HTA execution paths, tightening controls on mshta.exe/PowerShell/Msbuild.exe, and adding detections for the listed domains and URLs.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.